CVE MCP Server connects Claude to 27 security tools for faster vulnerability triage
A new open-source project called CVE MCP Server gives Claude access to 27 security intelligence tools across 21 data sources. The goal is simple: help security teams investigate CVEs, exposed hosts, malicious IPs, suspicious files, and vulnerable dependencies from one natural-language workflow.
The project uses Anthropic’s Model Context Protocol, or MCP, to connect Claude with external security APIs. Instead of switching between NVD, EPSS, CISA KEV, GitHub Advisories, VirusTotal, Shodan, GreyNoise, OSV.dev, and other tools, analysts can ask one question and receive a structured risk summary.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
CVE MCP Server does not remove the need for human review. However, it can reduce the manual work behind vulnerability triage by gathering evidence, calculating a composite risk score, and ranking CVEs by urgency.
What CVE MCP Server does
CVE MCP Server works as a bridge between Claude and security data sources. Claude receives the user’s question, calls the relevant MCP tools, and returns a report that combines vulnerability details, exploitation probability, known exploitation status, proof-of-concept availability, and threat intelligence.
The project supports Claude Desktop and Claude Code. It runs as a local MCP server and communicates with outside services through outbound HTTPS requests.
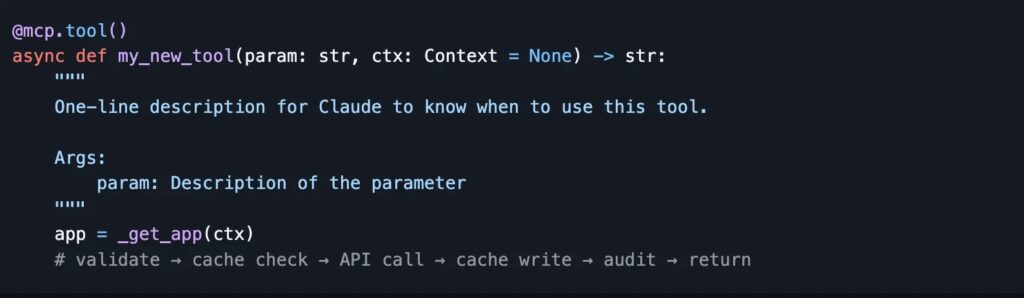
The developer describes it as a production-grade MCP server built with Python, FastMCP, httpx, aiosqlite, Pydantic v2, and defusedxml. It also includes rate limiting, caching, audit logging, and graceful fallback behavior when some API keys are missing.
At a glance
| Item | Details |
|---|---|
| Project name | CVE MCP Server |
| Developer | Mahipal, also known as mukul975 on GitHub |
| Main purpose | AI-assisted vulnerability and threat intelligence triage |
| AI client | Claude Desktop and Claude Code |
| Protocol | Model Context Protocol |
| Tool count | 27 tools |
| Data sources | 21 APIs and security intelligence sources |
| License | MIT |
Why this matters for security teams
Vulnerability triage often requires several separate checks. A team may need to inspect CVSS severity, EPSS probability, CISA KEV status, public exploits, vendor advisories, GitHub patches, exposed systems, and malware references before deciding what to patch first.
CVE MCP Server brings those signals into one workflow. For example, an analyst can ask whether a CVE needs emergency patching, and Claude can query NVD, EPSS, CISA KEV, exploit sources, and MITRE ATT&CK-related data before producing a recommendation.
This approach fits the wider shift away from CVSS-only prioritization. FIRST describes EPSS as a daily estimate of the probability that exploitation activity will be observed for a vulnerability within the next 30 days.
The 27 tools are grouped by security task
| Category | Examples of tools | Purpose |
|---|---|---|
| Core vulnerability intelligence | lookup_cve, search_cves, get_epss_score, check_kev_status | Pull CVE details, exploitation probability, KEV status, CVSS data, CWEs, and references. |
| Exploit and attack intelligence | search_exploits, get_mitre_techniques, check_poc_availability, get_attack_patterns | Find public exploit signals, map weaknesses to attack patterns, and connect CVEs to tactics. |
| Risk and reporting | calculate_risk_score, generate_risk_report, prioritize_cves, get_trending_cves | Rank vulnerabilities, create reports, and identify urgent patching candidates. |
| Network intelligence | lookup_ip_reputation, check_ip_noise, shodan_host_lookup, passive_dns_lookup | Investigate IP reputation, scanning activity, open services, and passive DNS history. |
| Threat intelligence | virustotal_lookup, search_malware, search_iocs, check_ransomware | Check hashes, domains, malware samples, IOCs, and ransomware payment data. |
| DevSecOps | scan_dependencies, scan_github_advisories, urlscan_check | Scan packages, GitHub advisories, and suspicious URLs. |
How the risk score works
The project includes a composite risk score from 0 to 100. It weighs CVSS, EPSS, CISA KEV status, and public proof-of-concept availability.
The formula gives the largest weight to EPSS at 35 percent, followed by KEV status at 30 percent, CVSS at 20 percent, and proof-of-concept availability at 15 percent. The project also applies boost multipliers when a vulnerability appears in KEV with an active PoC, has a high CVSS score with high EPSS probability, or was published recently.
A score of 76 to 100 receives a critical label in the project’s model, with a recommended 24 to 48-hour emergency patching window. Scores below that receive lower urgency labels and longer remediation timelines.
Data sources supported by the project
- NVD for CVE records, CVSS scores, CWEs, references, and affected products.
- FIRST EPSS for exploitation probability and percentile data.
- CISA KEV for known exploited vulnerabilities.
- OSV.dev for open-source package vulnerability data.
- GitHub Advisories and GitHub Code Search for advisory and exploit signals.
- MITRE ATT&CK and CAPEC for attack mapping.
- AbuseIPDB, GreyNoise, Shodan, and CIRCL Passive DNS for network intelligence.
- VirusTotal, MalwareBazaar, ThreatFox, Ransomwhere, and AlienVault OTX for threat intelligence.
- URLScan.io for URL analysis.
- MSRC, Red Hat Security, and Ubuntu Security for vendor advisory context.
Eight tools can run without API keys, including EPSS, CISA KEV, OSV.dev, MITRE ATT&CK, CWE lookup, CVSS parsing, Ransomwhere, and reduced-rate NVD lookup.
For stronger coverage, teams can add keys for NVD, GitHub, AbuseIPDB, VirusTotal, GreyNoise, Shodan, URLScan.io, and CIRCL Passive DNS.
Why MCP is important here
MCP is an open standard introduced by Anthropic to connect AI-powered tools with external data sources. In this case, it lets Claude call security tools and receive structured results instead of relying only on model memory.
That distinction matters for vulnerability management. CVE data, EPSS scores, KEV entries, advisories, exposed hosts, and malware references change constantly. A live tool layer helps Claude work with fresher evidence.
It also gives security teams a more repeatable workflow. Instead of asking an analyst to manually check a dozen sites, the MCP server can call the same sources in a consistent order and return the results in a report format.
Useful examples
- Ask whether CVE-2024-3400 needs emergency patching.
- Scan a requirements.txt-style dependency list for vulnerable packages.
- Rank 20 CVEs by composite risk score.
- Check whether a suspicious IP appears in AbuseIPDB, GreyNoise, or Shodan.
- Look up a file hash, domain, or URL across threat intelligence sources.
- Generate an executive report for a group of high-risk CVEs.
The DevSecOps tools are especially useful for software teams. A developer can provide package names and versions, then receive vulnerability findings and upgrade recommendations.
Security teams can also use the project during incident response. For example, an analyst can ask Claude to investigate an IP address, review its reputation, check scanning activity, and summarize whether blocking is justified.
Security and privacy design
The project says all traffic uses outbound HTTPS and no inbound ports are opened. API keys are loaded from environment variables and are not logged.
The repository also says private and internal IP addresses are blocked from lookup tools. That helps reduce the risk of accidental internal network exposure through external enrichment services.
Even with those safeguards, teams should test the tool in a controlled environment before using it in production. MCP tools can connect AI agents to real systems, so organizations should review permissions, logs, API keys, and allowed actions carefully.
What teams should consider before using it
- Run the server in a restricted environment first.
- Use least-privilege API keys for external services.
- Do not expose sensitive internal IPs, hostnames, or incident data without policy review.
- Log tool calls for audit and troubleshooting.
- Validate risk-score outputs against existing vulnerability management rules.
- Keep human approval in the patching workflow.
- Review MCP server code before connecting it to production security tooling.
The biggest value is speed and correlation. The biggest risk is over-trusting automated conclusions. Security teams should treat the output as an analyst-assist layer, not a final decision engine.
Used carefully, CVE MCP Server could help small teams triage more vulnerabilities with less manual tab-switching. Larger teams may find value in using it as a front end for repeatable enrichment and reporting.
FAQ
CVE MCP Server is an open-source Model Context Protocol server that connects Claude to security intelligence tools for CVE triage, threat intelligence, network checks, and dependency scanning.
The project includes 27 MCP tools across 21 data sources and APIs.
Some tools work without API keys, including EPSS, CISA KEV, OSV.dev, MITRE ATT&CK, CWE lookup, CVSS parsing, Ransomwhere, and reduced-rate NVD lookup. Other services need keys for full functionality.
The score combines CVSS severity, EPSS exploitation probability, CISA KEV status, and proof-of-concept availability. It also applies boost multipliers for higher-risk combinations.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages