KarstoRAT malware gives attackers webcam, audio, and remote-control access on Windows PCs

KarstoRAT is a newly observed Windows remote access trojan that gives attackers deep control over infected systems. It can capture webcam images, record audio, log keystrokes, take screenshots, steal tokens, collect system details, and download more payloads.
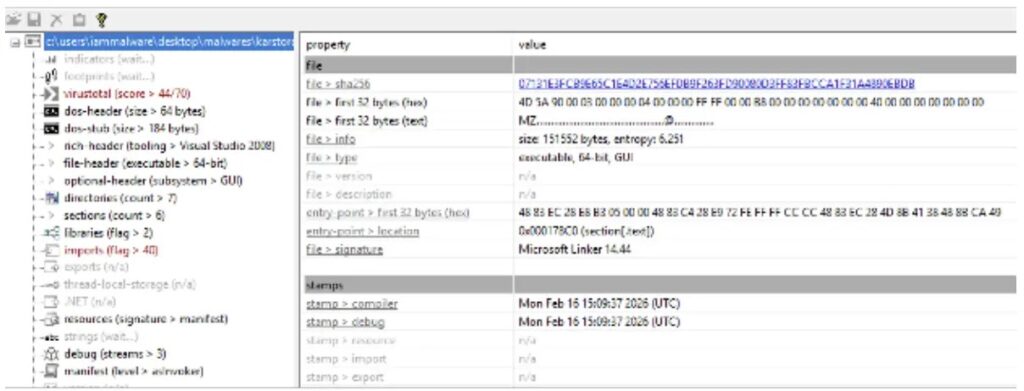
Security researchers observed the malware in early 2026 and described it as a stealthy RAT with surveillance and post-compromise capabilities. Unlike many widely sold malware tools, KarstoRAT appears to have limited public exposure, which may point to a more private or controlled operation.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The malware targets Windows machines and communicates with attacker-controlled infrastructure through HTTP. Its traffic uses the user agent SecurityNotifier, a name that can make malicious activity look less suspicious during a quick network review.
KarstoRAT focuses on spying and remote control
KarstoRAT gives attackers more than basic access to a compromised PC. Once it starts running, it can collect system information, monitor the user, capture sensitive activity, and keep checking for new commands from its command-and-control server.
LevelBlue SpiderLabs said KarstoRAT can perform system reconnaissance, webcam monitoring, audio monitoring, screenshot capture, keylogging, token theft, and remote payload execution. These features make it useful for both surveillance and follow-on attacks.
The malware also keeps a persistent connection pattern by entering a repeating two-second loop. This lets the operator maintain contact with the infected system and trigger different modules when needed.
How KarstoRAT reaches victims
Researchers found that KarstoRAT used gaming-related lures to trick users into downloading the malware. One lure used a fake Blox Fruits virtual marketplace, while another used a game cheat download panel.
This distribution style matters because it targets users who may already expect to download unofficial files. Roblox players, FPS modders, and GTA cheat seekers can become easy targets when fake tools promise free items, trading features, or premium cheats.
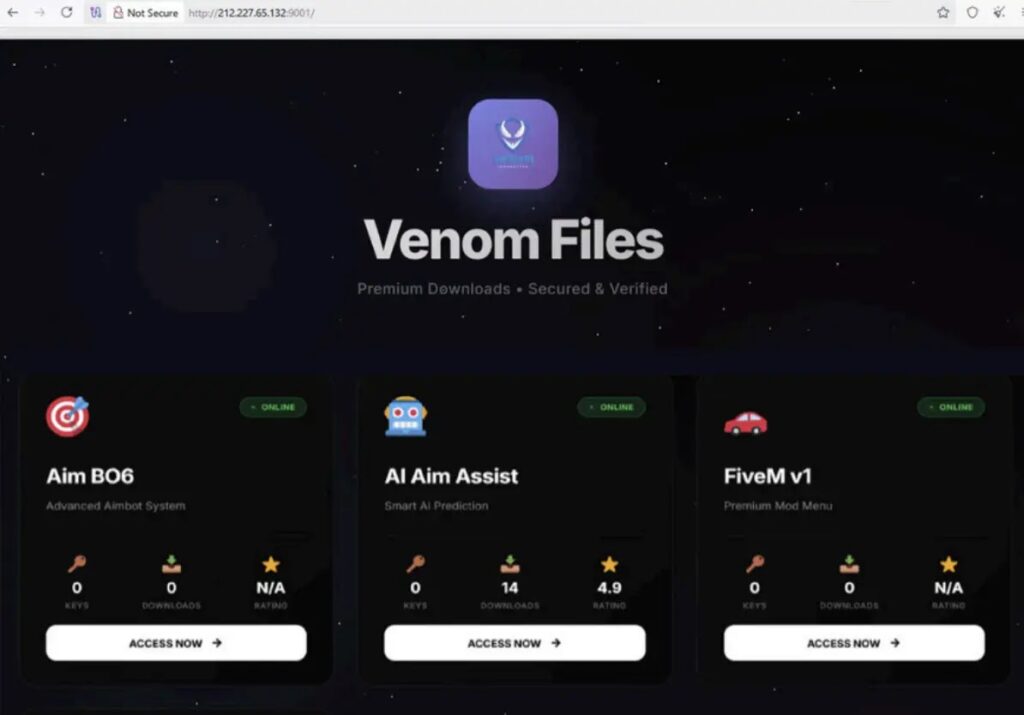
Attackers often use gaming lures because victims may ignore browser warnings, antivirus alerts, or file reputation prompts. Once the file runs, KarstoRAT can begin collecting information and waiting for remote commands.
At a glance
| Item | Details |
|---|---|
| Threat name | KarstoRAT |
| Malware type | Windows remote access trojan |
| Observed activity | Early 2026 |
| Main risk | Remote spying, data theft, persistence, and payload execution |
| Known user agent | SecurityNotifier |
| Known lure style | Fake Roblox trading pages and game cheat downloads |
What KarstoRAT can do on an infected PC
The malware can collect the computer name, username, operating system version, CPU details, memory information, disk information, and a list of running processes. This helps the attacker understand the system before choosing the next action.
Its surveillance modules make the threat more serious. KarstoRAT can capture screenshots, access the webcam, record audio, log keystrokes, and exfiltrate stolen data through dedicated upload endpoints.
The RAT can also download and run additional payloads. That means an initial KarstoRAT infection could lead to more malware, credential theft tools, data theft, or deeper network compromise.
Main capabilities
- Captures screenshots from the infected machine
- Monitors webcam activity
- Records audio from the microphone
- Logs keystrokes across applications
- Steals tokens and other sensitive information
- Collects system and process details
- Downloads and executes additional payloads
- Maintains persistence after login
- Can remove itself to reduce forensic traces
The malware uses persistence and disruption features
KarstoRAT includes persistence functions that allow it to relaunch after a user logs in. Researchers also noted STARTUP_ON and STARTUP_OFF capabilities, which control whether it starts automatically.
The malware includes unusual disruption features as well. It can make the system speak attacker-controlled text through the speakers, change the desktop background, flip the display upside down, and swap mouse button functions.
These functions may look less valuable than credential theft, but they can still help attackers harass users, distract victims, test control over a machine, or create confusion during an intrusion.
Why defenders should pay attention
KarstoRAT shows how modern RATs combine spying, persistence, payload delivery, and social engineering in one package. A single infection can expose private communications, stored credentials, browser sessions, local files, and corporate access tokens.
The use of gaming lures also widens the risk. A personal PC infected through a cheat download can still expose work accounts, cloud sessions, password managers, and files if the same machine handles both personal and professional activity.
Security teams should treat suspicious SecurityNotifier traffic, unknown startup entries, unusual outbound connections, and unexpected webcam or microphone access as warning signs. They should also review endpoint telemetry for new scheduled tasks, suspicious Run key changes, and unexpected payload downloads.
Recommended actions
- Block known malicious infrastructure linked to KarstoRAT where confirmed by threat intelligence.
- Hunt for the SecurityNotifier user agent in proxy, firewall, and EDR logs.
- Review startup folders, Run keys, and scheduled tasks for unknown entries.
- Check for unexplained webcam, microphone, screenshot, or keylogging activity.
- Remove unauthorized game cheats, trading tools, and unofficial launchers from managed systems.
- Rotate passwords and tokens from any system suspected of infection.
- Run a full endpoint scan and isolate confirmed infected machines before cleanup.
- Educate users not to install game cheats or trading tools from untrusted sites.
What users should do
Users should avoid downloading game cheats, Roblox trading tools, cracked software, or mod menus from unknown websites. These files often use the same language as legitimate tools, but they can install malware in the background.
If a Windows PC starts behaving strangely after installing a gaming tool, the user should disconnect it from the internet and run a full security scan. Signs can include high resource usage, unknown startup items, unusual network traffic, or unexpected security alerts.
Anyone who used passwords, work accounts, crypto wallets, or email accounts on an infected device should change those credentials from a clean machine. Token theft and keylogging mean the attacker may already have access to active sessions.
Summary
- KarstoRAT is a new Windows RAT observed in early 2026.
- It can spy through webcams and microphones, capture screenshots, log keys, and steal tokens.
- Researchers linked its distribution to fake gaming and cheat-related lures.
- The malware communicates with attacker infrastructure and uses the SecurityNotifier user agent.
- Users and admins should block known indicators, hunt for persistence, and avoid untrusted downloads.
FAQ
KarstoRAT is a Windows remote access trojan that allows attackers to monitor, control, and steal data from infected machines.
It combines webcam capture, audio recording, keylogging, screenshot theft, token theft, persistence, and remote payload execution.
Researchers found gaming-related lures, including fake Roblox trading content and cheat download pages, used to trick users into running the malware.
Companies should monitor for SecurityNotifier traffic, unusual startup entries, unknown scheduled tasks, suspicious outbound requests, and unexpected webcam or microphone access.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages