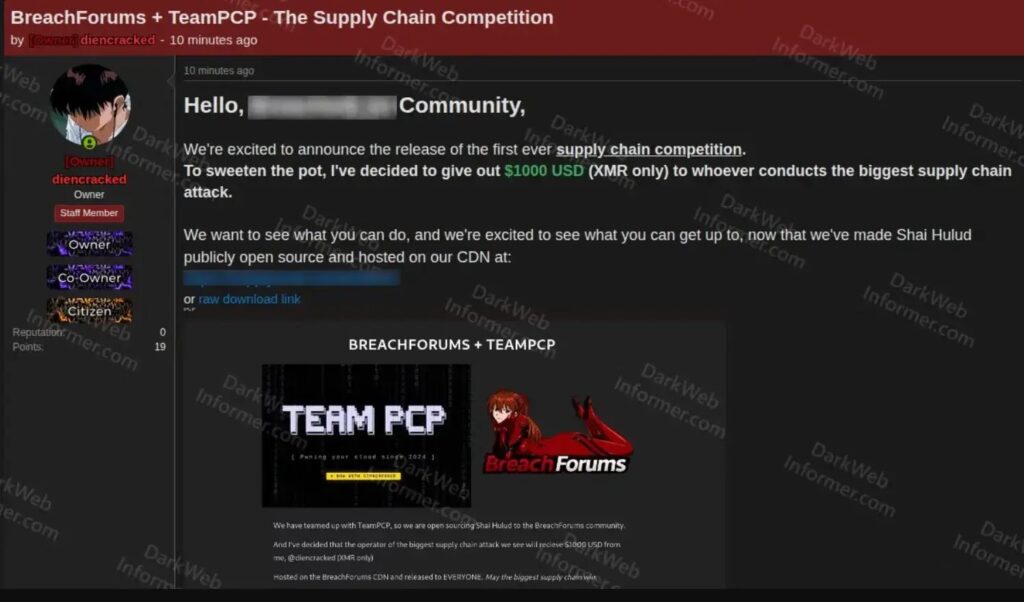
TeamPCP And BreachForums Promote $1,000 Contest For Supply Chain Attacks

TeamPCP and BreachForums are promoting a supply chain attack contest that offers $1,000 in Monero for the biggest open-source package compromise, according to new research from Socket.
The contest reportedly requires participants to use Shai-Hulud, a supply chain attack tool linked to recent npm and PyPI compromises. Attackers must submit a forum handle or BreachForums profile and provide proof of access to qualify.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The scoring system makes the campaign especially risky for the open-source ecosystem. Winners are reportedly judged by the weekly and monthly download counts of compromised packages, which rewards attacks against popular dependencies and also encourages broad compromise of smaller packages.
How the supply chain contest works
Socket says the contest was announced on BreachForums by an account identified as the forum’s owner, in collaboration with TeamPCP. The post offers a $1,000 Monero prize, along with reputation and status inside the cybercrime forum.
Participants must use Shai-Hulud in their attacks and provide what the forum describes as reasonable proof of access. The score comes from package reach, which turns download volume into a public leaderboard.
That structure creates a dangerous incentive. A single high-download package can score well, but multiple smaller package compromises can also be combined, giving low-level actors a reason to spread attacks across the ecosystem.
| Contest detail | Reported information |
|---|---|
| Groups involved | TeamPCP and BreachForums |
| Prize | $1,000 in Monero |
| Required tool | Shai-Hulud |
| Target | Open-source packages |
| Scoring method | Weekly and monthly download counts of compromised packages |
| Main risk | Copycat supply chain attacks against npm, PyPI, CI/CD systems, and developer tooling |
Why a small prize still creates a major risk
The $1,000 reward looks small compared with the value of a successful supply chain compromise. Access to CI/CD secrets, cloud credentials, maintainer tokens, source code, and enterprise developer systems can be worth far more to skilled criminals.
That is why the contest looks less like a serious payout and more like a recruitment and reputation campaign. It gives lower-tier actors a public challenge, a known tool name, and a way to gain status by burning stolen access.
SOCRadar described the trend as the gamification of cybercrime. Instead of isolated attacks, underground forums can turn intrusions into public competitions where participants copy methods, compare results, and chase recognition.
Shai-Hulud has already hit major developer ecosystems
The contest appears after several waves of Shai-Hulud activity targeting software supply chains. Recent campaigns have hit npm packages, PyPI packages, GitHub Actions workflows, Docker images, OpenVSX extensions, and developer infrastructure.
StepSecurity recently reported that TeamPCP’s Mini Shai-Hulud worm compromised legitimate npm packages by stealing CI/CD secrets and publishing malicious versions through trusted release pipelines. The same research said compromised packages carried valid SLSA Build Level 3 provenance attestations, which made the malicious packages harder to distinguish through provenance checks alone.
Snyk also reported that the May 2026 TanStack compromise involved 84 malicious npm artifacts across 42 packages in the @tanstack namespace. The malicious versions later spread to other maintainers, including Mistral AI, UiPath, and others.
| Risk area | Why defenders should care |
|---|---|
| npm and PyPI packages | Malicious versions can reach developers and automated builds quickly |
| CI/CD workflows | Attackers can steal tokens and publish packages from trusted pipelines |
| Provenance checks | Valid build attestations do not guarantee that the built code is safe |
| Developer machines | Local installs can expose SSH keys, cloud credentials, and environment secrets |
| Open-source maintainers | Compromised maintainer access can turn trusted projects into malware distribution channels |
Open-source malware makes copycat attacks easier
The Register reported that TeamPCP appeared to open-source the Shai-Hulud worm through repositories that circulated on GitHub. Ox Security reportedly observed code patterns similar to earlier Shai-Hulud campaigns, including credential theft and GitHub-based dead-drop behavior.
Even if some copies are incomplete or modified, the public circulation of attack logic can lower the barrier for other criminals. Less experienced actors can reuse code, change infrastructure, and test variants against open-source projects.
This is the bigger concern for defenders. The campaign does not need to attract elite operators to create damage. It only needs enough copycats to generate more suspicious package updates, more compromised maintainers, and more pressure on enterprise security teams.
- Open-source attack code can help copycats build variants faster.
- Forum contests can turn stolen access into public reputation.
- Download-based scoring can encourage attacks against both large and small packages.
- Compromised release pipelines can make malicious packages look trusted.
- Enterprise teams may face more alerts from package updates and CI/CD anomalies.
What TeamPCP has targeted before
Security researchers have linked TeamPCP to campaigns against security tools, cloud development workflows, and trusted package release systems. Socket says it has tracked the group across GitHub Actions, Docker images, OpenVSX extensions, npm, PyPI, and Packagist.
Unit 42 has also tracked an escalation in npm supply chain attacks since the original Shai-Hulud wave. Researchers say attackers increasingly focus on wormable propagation, CI/CD persistence, and multi-stage payloads that can harvest credentials from developer environments.
This pattern shows why security teams should treat the contest as more than forum noise. Even a small number of participants can create real operational work if they target packages with large dependency chains or trusted enterprise use.
How organizations can reduce exposure
Organizations should assume that more copycat attempts may follow. The safest response is to tighten package intake, slow risky dependency updates, and watch CI/CD workflows for unusual publishing activity.
Teams should not rely on package popularity or provenance alone. A known package name, a legitimate maintainer account, or a valid build attestation does not always prove that the current version is safe.
Developers and security teams should review dependencies, restrict publishing permissions, and audit workflows that can access registry tokens, GitHub OIDC identities, cloud secrets, and production deployment credentials.
- Enable dependency review before package updates reach production builds.
- Use package lockfiles and avoid automatic upgrades for high-risk environments.
- Apply release-age cooldowns to reduce exposure to freshly published malicious versions.
- Audit GitHub Actions workflows that use pull_request_target or privileged tokens.
- Limit npm, PyPI, and GitHub publishing permissions to the smallest required scope.
- Rotate secrets after any confirmed install of a malicious package.
- Rebuild CI/CD runners from clean images after suspected compromise.
- Monitor for unusual repositories, suspicious branches, and unexpected package version bumps.
- Block known malicious infrastructure when indicators become available.
- Train developers to treat unexpected package updates as a security event.
Why this contest matters for open-source security
The contest shows how cybercrime groups now borrow tactics from normal software communities. They use branding, public challenges, shared tooling, and reputation systems to attract participants and scale attacks.
For open-source maintainers, this adds another burden. A project does not need to be a household name to become useful to attackers. Smaller packages can still hold publishing rights, build tokens, and downstream trust.
For enterprises, the lesson is clear. Supply chain security now depends on watching the full path from source code to release pipeline to dependency update. Attackers are not only trying to steal credentials. They are trying to turn trusted software delivery into their distribution network.
FAQ
It is a reported cybercrime contest promoted by TeamPCP and BreachForums that offers $1,000 in Monero for the biggest open-source package compromise using Shai-Hulud tooling.
The contest reportedly scores attackers by package download counts, which can encourage attacks against popular dependencies and broad compromise of smaller packages across the open-source ecosystem.
TeamPCP is a threat group linked by security researchers to supply chain attacks against developer tools, CI/CD workflows, package registries, Docker images, GitHub Actions, and open-source infrastructure.
Developers should review dependency updates, avoid automatic upgrades in sensitive environments, audit CI/CD workflows, restrict publishing permissions, rebuild compromised runners, and rotate secrets after any confirmed exposure.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages