AI-assisted Lazarus campaign lures developers with fake coding tests that trigger malware on open
A North Korea-linked hacking operation is targeting software developers with fake job interviews and booby-trapped coding assignments, and the campaign shows how generative AI can help attackers scale faster. Expel says the group, which it tracks as HexagonalRodent, targets Web3 developers in particular and has already exfiltrated cryptocurrency wallets worth up to $12 million over a three-month period.
The social engineering is simple and effective. Attackers pose as recruiters on platforms like LinkedIn or publish fake openings, then send a take-home coding challenge that looks legitimate. The trap sits inside the project files, where malicious configuration and source code execute once the victim opens the folder in VS Code or runs the project normally.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes this campaign stand out is not just the malware. Expel says the operators used tools such as ChatGPT and Cursor to help write malware, build fake company websites, and support the broader deception chain. Expel also published statements from Cursor and OpenAI confirming they reviewed or restricted abuse tied to the activity.
How the fake coding test infects developers
The main lure is a coding assessment delivered as part of a fake hiring process. Expel says the project includes a malicious tasks.json file that abuses a built-in VS Code feature. When configured with runOn: "folderOpen", the task can run the moment a developer opens the folder in VS Code, even before any visible app behavior looks suspicious.
The attackers also add malicious logic to the source code itself. That gives them a second infection path for developers who are not using VS Code, or for cases where automatic task execution has been disabled. Expel says the two delivery methods together raise the odds of compromise across different workflows.
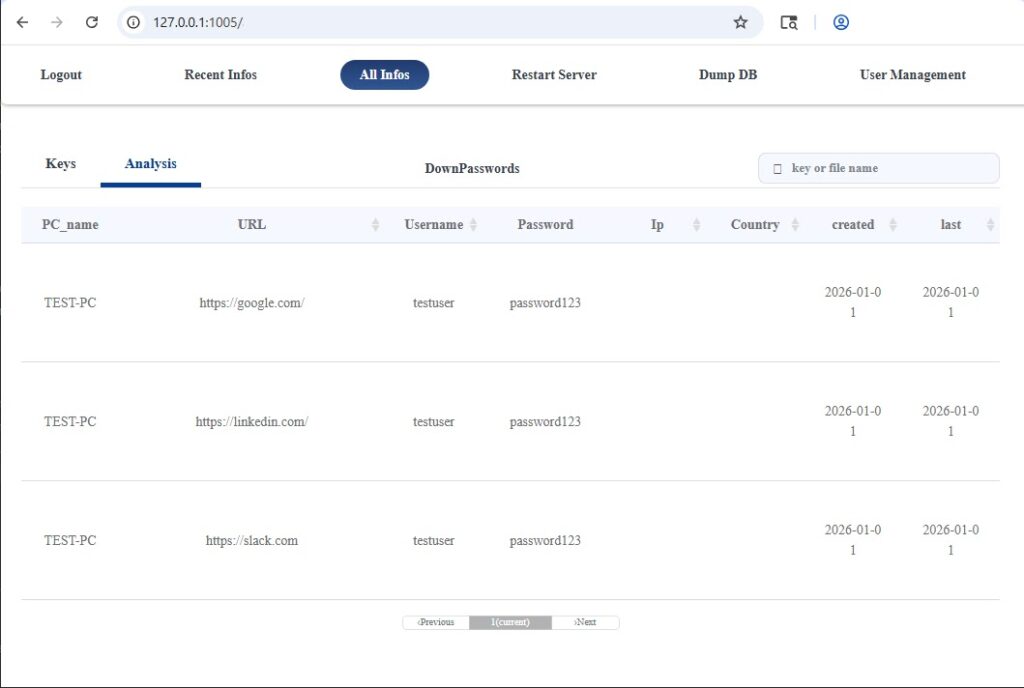
Once inside the system, the malware chain expands. Expel says BeaverTail steals credentials from browsers, password managers, the macOS Keychain, and Linux Keyring, while OtterCookie and InvisibleFerret provide reverse-shell style remote access. The malware families are written in NodeJS and Python, which helps them blend in on developer machines that already use those runtimes every day.
Why this campaign matters
Expel says HexagonalRodent differs from some better-known DPRK groups that focus on large crypto exchanges. Instead, this operation goes after individual developers and smaller Web3 projects, where valuable wallets and credentials may exist without enterprise-grade defenses. That opportunistic model appears to be working. Expel says the group stole data from 2,726 infected systems and exposed public keys for wallets worth up to $12 million over three months.
The AI angle matters because it lowered the effort needed to run the campaign at scale. Expel says the operators used ChatGPT and Cursor, and WIRED reported that Anima was also abused to help build fake sites and infrastructure. Cursor told Expel it blocked the user and IP addresses involved, while OpenAI said it saw limited use tied to dual-use cyber topics and that its systems refused or redirected more overtly malicious requests.
Expel also tied the group to a supply chain incident involving the compromised fast-draft VSX extension, which it says distributed OtterCookie in March 2026. The company says this was the first time it had seen this group pull off a supply chain attack, a sign that the operators may be expanding beyond recruiter lures into wider distribution methods.
What security teams and developers should watch for
| Indicator | Why it matters |
|---|---|
| Unexpected coding challenge from a recruiter | Main social engineering lure in the campaign |
tasks.json with runOn: "folderOpen" | Can trigger execution just by opening a folder in VS Code |
| NodeJS or Python processes with odd outbound traffic | Matches the malware families Expel tracked |
| Fake company sites and recruiter identities | Used to make the job offer look real |
| BeaverTail, OtterCookie, InvisibleFerret activity | Malware families linked to credential theft and persistence |
| fast-draft extension compromise | Shows the group also used a supply chain route |
The indicators above come from Expel’s April 22 report on HexagonalRodent and the campaign’s infection chain.
What developers should do now
- Never run a take-home assessment from an unknown or unverified recruiter without reviewing every file first, including hidden configuration files.
- Disable or tightly control automatic task execution in VS Code so opening a folder does not silently trigger commands.
- Treat unexpected NodeJS and Python processes with persistent outbound connections as suspicious on developer systems.
- Use hardware security keys or hardware wallets for crypto assets. Expel says hardware-backed protection made wallet theft harder for the attackers.
- Verify recruiters and employers through official channels before opening any project files or assessment packages.
FAQ
Expel says it assesses with high confidence that HexagonalRodent is North Korean state-sponsored. It also says the group is likely a subgroup or spin-off within the broader DPRK ecosystem, with medium-high confidence that it is a subset of what CrowdStrike calls Famous Chollima.
The project includes a malicious tasks.json file configured to run on folder open. That means the malware can execute when the victim simply opens the project in VS Code.
Expel says BeaverTail can steal credentials from browsers, password managers, macOS Keychain, and Linux Keyring, while OtterCookie and InvisibleFerret provide remote access.
OpenAI said it did not identify novel capabilities in the interactions it could see. The value, based on public reporting and Expel’s findings, appears to be speed, scale, and easier infrastructure building rather than a brand-new offensive technique.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages