AI-Powered Attacks Hit FortiGate VPNs Using DeepSeek and Claude Automation

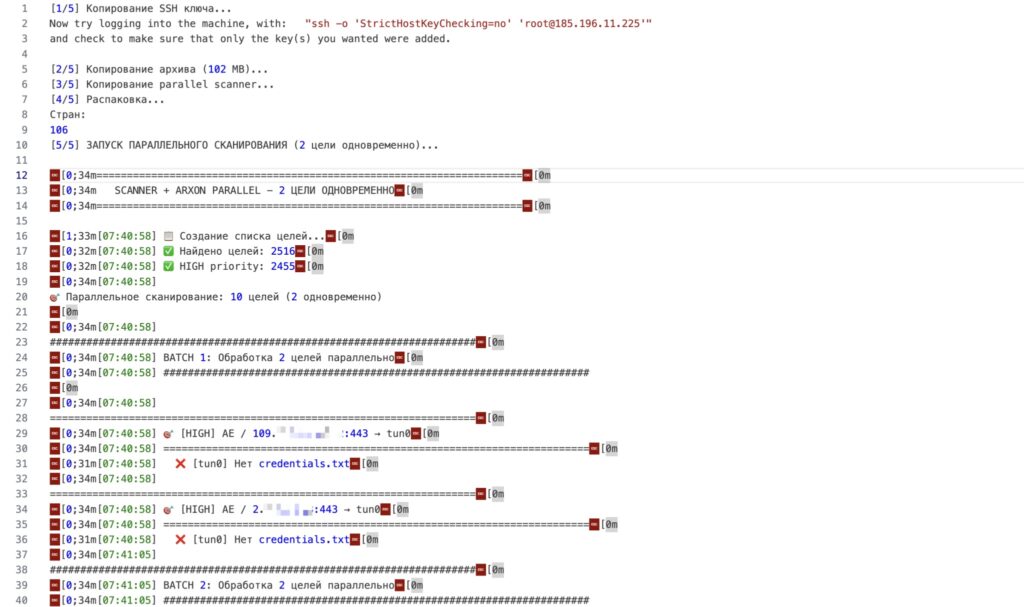
Threat actors deployed DeepSeek and Claude LLMs to breach 2,500+ FortiGate SSL VPN devices across 106 countries. Custom ARXON MCP server and CHECKER2 Docker orchestrator automate mass scanning, vuln assessment, and exploitation. Misconfigured attack server exposed full pipeline in early February 2026.
Stolen FortiGate credentials fed into DeepSeek generate strategic attack plans. Claude executes coding tasks running Impacket and Metasploit autonomously post-access. Low-skill operators manage thousands of targets simultaneously.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Exposed server revealed parallel batch processing logs. Telecom, finance, and government edge devices hit worldwide. Automation scales beyond human capacity dramatically.
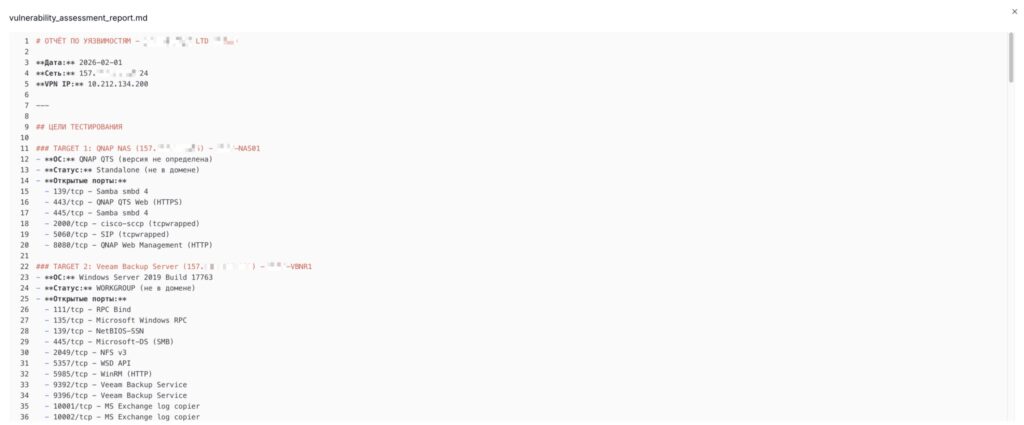
CHECKER2 scans VPN endpoints at scale through Docker containers. ARXON bridges network recon data into LLM prompts producing actionable exploits. Vulnerability reports auto-prioritize privilege escalation paths.
Traditional defenses fail against AI-orchestrated speed. Manual SOC response cannot match parallel automation across continents.
Attack Infrastructure Table
| Component | Function | LLM Role |
|---|---|---|
| CHECKER2 | Docker VPN scanner | Target discovery |
| ARXON | MCP server | Data-to-exploit bridge |
| DeepSeek | Strategy generation | Recon → attack plans |
| Claude | Code execution | Impacket/Metasploit runs |
Telecom perimeters breached systematically. Exposed deploy_output.log showed global target diversity. Single operator controls thousands via AI pipeline.
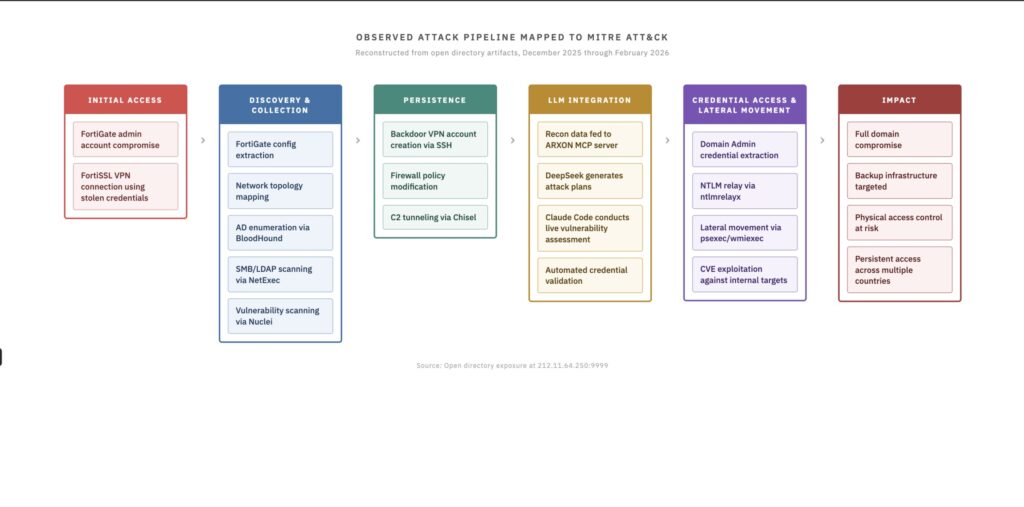
Kill Chain Automation
Recon phase: CHECKER2 maps FortiGate endpoints globally
Planning phase: DeepSeek analyzes stolen configs for attack paths
Execution phase: Claude writes/runs Impacket, Metasploit exploits
Privilege phase: Auto-generated escalation recommendations
Lateral phase: Network mapping for critical asset discovery
Custom MCP protocol feeds structured network data into LLMs. Output formats exploit chains directly without human parsing.
Exposed vuln assessment snippets show model reasoning. Prioritized next steps include Kerberoasting, LSASS dumping, unquoted service paths.
Immediate Defense Actions
- Patch all FortiGate firmware to latest stable immediately
- Audit VPN accounts for anomalous creations weekly
- Monitor SSH sessions from unexpected sources
- Deploy network baselines against config drift
- Block ARXON MCP traffic patterns at perimeter
- Hunt Impacket execution through EDR logging
AI kill chain represents cybercrime evolution. Human oversight drops to strategic direction only. Scale defeats traditional capacity-based defenses completely.
Exfiltration targets crown jewels post-access. Credential harvesting precedes ransomware or data theft systematically.
FAQ
FortiGate SSL VPN appliances using stolen configuration data.
DeepSeek for planning, Claude for code execution and vuln assessment.
2,500+ devices across 106 countries in parallel batches.
CHECKER2 Docker scanner + ARXON Model Context Protocol server.
Telecom, finance, government edge infrastructure worldwide.
Audit VPN accounts, monitor SSH, baseline configs, hunt Impacket.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages