AstraZeneca breach claim surfaces as LAPSUS$ resurfaces, but confirmation is still missing
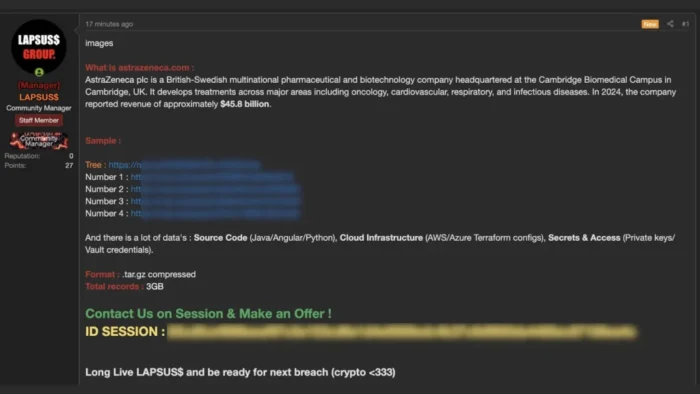
AstraZeneca has not publicly confirmed a breach as of March 23, 2026. What exists right now is a claim from actors identifying themselves as LAPSUS$, who say they stole about 3GB of internal AstraZeneca data and are trying to sell it rather than dump it publicly.
That distinction matters. A threat actor post, even one backed by screenshots or file listings, does not prove the full scope of an intrusion on its own. So the strongest version of this story is not that AstraZeneca was definitively breached, but that AstraZeneca is the subject of a serious and highly sensitive breach claim that has not yet received public confirmation from the company.
Reports circulating over the past few days say the alleged archive contains source code, cloud infrastructure files, credentials, and internal project material. Several outlets reviewing the forum post say the samples appear to reference Java, Angular, Python, Terraform, Ansible, GitHub, Jenkins, and internal supply-chain related repositories.
If the material is genuine, the risk goes beyond embarrassment. Exposed credentials, private keys, and CI/CD tokens can give attackers a path into cloud systems, development pipelines, and internal business applications. In a pharmaceutical company, that could create operational risk even if no clinical systems or patient-facing services were touched.
What the attackers are claiming
The posts attributed to LAPSUS$ describe a compressed archive of roughly 3GB. Reporting on those claims says the dataset allegedly includes internal code, infrastructure configuration, and secrets tied to development and automation environments.
The threat actors also appear to be using a sale model instead of an immediate public leak. According to published reports, they shared teasers, screenshots, and redacted samples, then directed interested buyers to negotiate privately through Session.
That approach fits a broader shift seen across cybercrime, where some groups try to monetize access quietly before they trigger a larger incident response or public fallout. In practical terms, that means defenders may face a period of uncertainty where the data is claimed, partially shown, but not yet fully released. This is often the hardest phase to assess from the outside.
| Alleged category | Reported examples |
|---|---|
| Source code | Java Spring Boot apps, Angular components, Python scripts |
| Cloud and automation | Terraform files, AWS and Azure references, Ansible roles |
| Secrets and access | Private keys, Vault material, GitHub and Jenkins-related credentials |
| Internal business data | Repository structures and supply-chain portal references |
Source: claims described by multiple cybersecurity reports.
Why this claim has drawn so much attention
LAPSUS$ carries a strong reputation because of its earlier attacks on major technology companies. That history makes any new claim involving the group more likely to attract scrutiny, even before a victim confirms anything publicly.
The AstraZeneca angle also raises the stakes because the company operates in a heavily regulated industry where intellectual property, supply chains, and internal research and business systems matter enormously. AstraZeneca’s own public materials acknowledge cybersecurity as a material business risk, which is standard language for a company of this size, but it underlines how seriously incidents like this are taken.
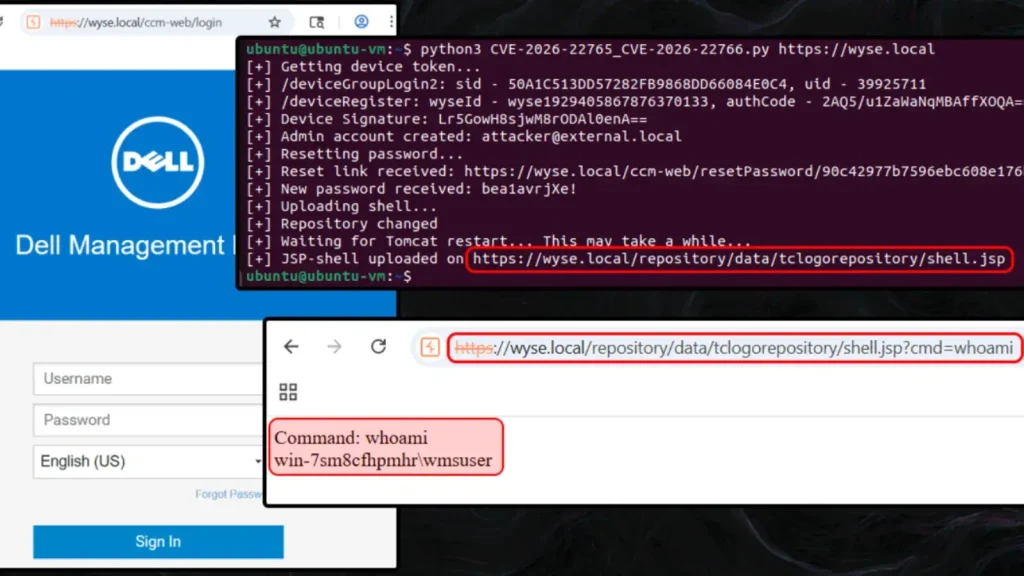
Another reason this story is moving fast is the nature of the alleged data. Source code and infrastructure files often give attackers more than raw documents do. They can reveal how environments are built, what services exist, how access works, and where the next weakness may be. Even a relatively small archive can become a roadmap for follow-on attacks if it includes secrets or deployment details.
What remains unconfirmed
No public AstraZeneca press release or newsroom update currently addresses the alleged breach. Searches of the company’s media center and investor pages do not show a March 2026 public statement about this incident at the time of writing.
That does not prove the claim is false. Companies often investigate first and speak later, especially when they still need to verify scope, attribution, or notification obligations. But it does mean readers should avoid treating every detail in the forum posts as settled fact.
The most responsible reading right now is simple: there is a credible-looking criminal claim, there are published samples described by cybersecurity outlets, but there is still no public confirmation from AstraZeneca and no independently published forensic report that fully validates the breach.
What AstraZeneca and defenders will likely focus on next
If the company is investigating, the first priority will likely be validating the samples and determining whether the exposed material is current, internal, and unauthorized. From there, teams would usually focus on token revocation, key rotation, repository access reviews, CI/CD audit trails, and cloud account monitoring. That is especially important when alleged leaked material includes secrets or automation credentials. This is an inference based on the reported data types and standard incident response practice.
Security teams outside AstraZeneca can also take a lesson from this case. Even when a breach is not yet confirmed, leaked infrastructure clues or code samples can become useful intelligence for copycat attackers. That is why these incidents often trigger urgent internal reviews long before a company says anything publicly.
Key takeaways
- AstraZeneca has not publicly confirmed a breach as of March 23, 2026.
- Actors identifying as LAPSUS$ claim they stole about 3GB of internal data.
- Reported samples allegedly include source code, cloud configuration files, and credentials.
- The data appears to be offered for private sale, not yet dumped publicly in full.
- The biggest risk would come from any valid secrets, keys, or CI/CD access tokens inside the archive.
FAQ
No public confirmation appears on AstraZeneca’s press release or investor pages as of March 23, 2026.
Reports say the group claims to hold source code, infrastructure files, and sensitive credentials from internal AstraZeneca environments.
Public reporting says no. The actors appear to be teasing samples and trying to sell access privately.
Because alleged leaked keys, tokens, and automation secrets can create immediate downstream risk if they are real and still active.
Potentially yes, if the reported credentials and cloud or CI/CD files are authentic. That could expose more than a single repository or server.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages