AuraStealer Infostealer Emerges: 48 C2 Domains Fuel Active Campaigns Since Mid-2025

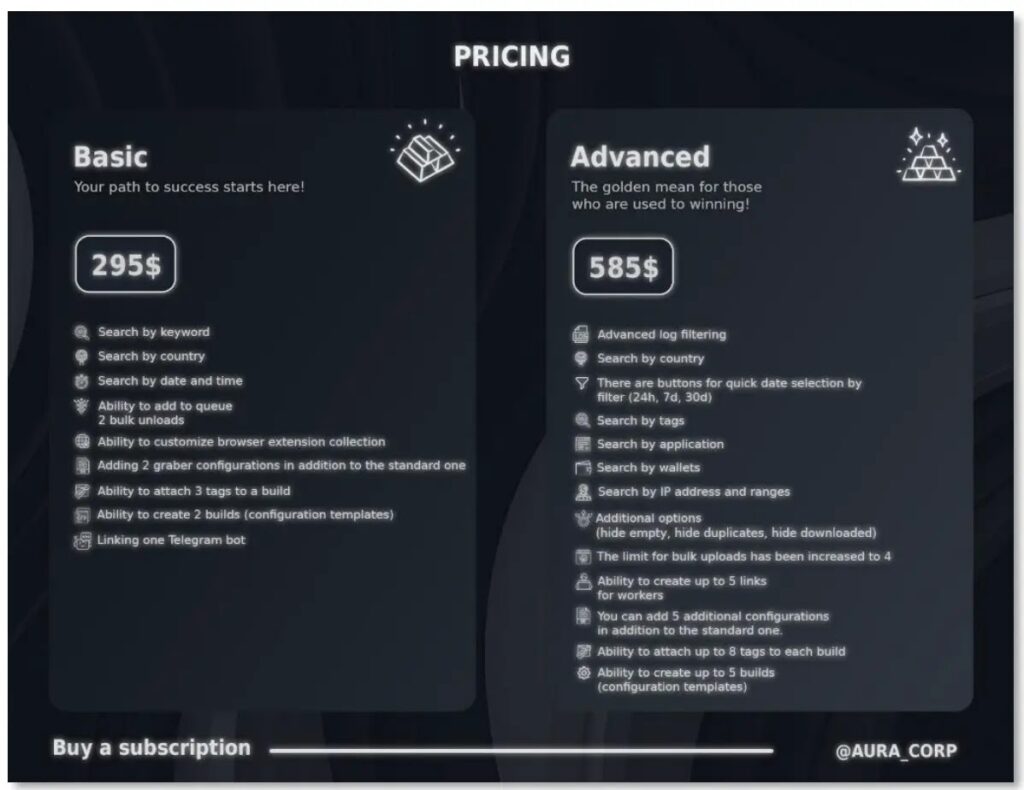
Threat actors unleashed AuraStealer, a potent new infostealer, starting in July 2025. Russian-speaking developers promote it on forums like XSS, Exploit, and others as a LummaC2 rival. It grabs data from 110+ browsers, 70+ apps, and 250+ extensions. Subscriptions run $295/month basic or $585/month advanced.
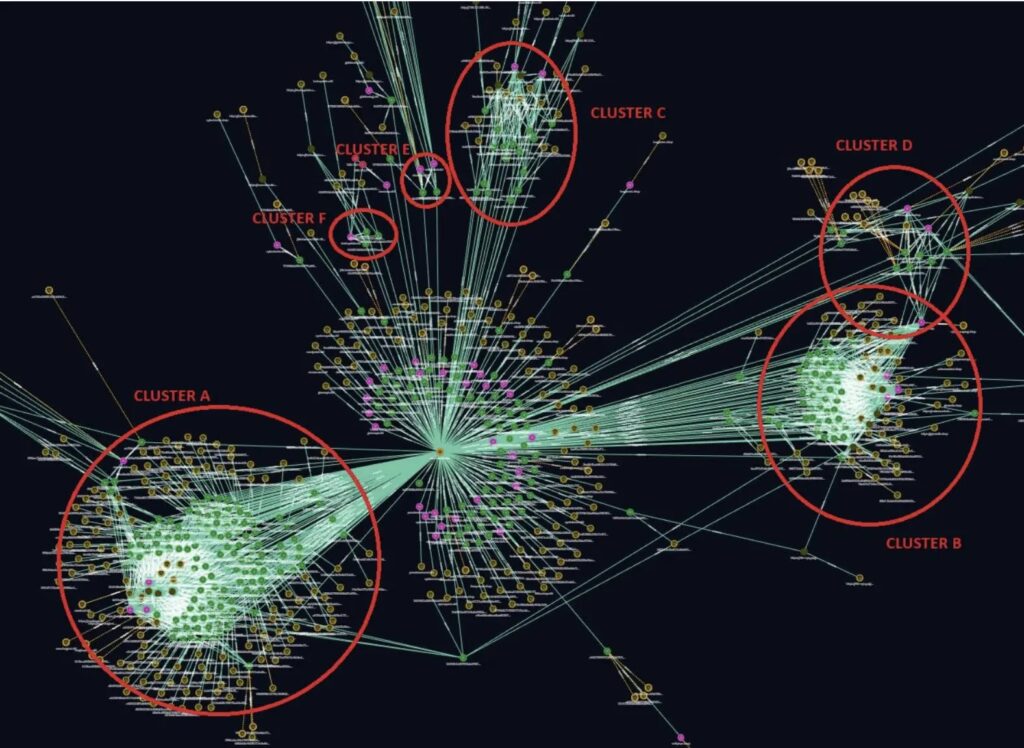
Intrinsec analysts tracked over 200 VirusTotal samples to 48 C2 domains. Most use cheap .SHOP and .CFD TLDs behind Cloudflare proxies. Recent builds shift to .CFD, showing quick evolution. Panels offer build generators, geo-dashboards, log filters, and Telegram bots.
ClickFix campaigns hit hard in October 2025 via fake TikTok tutorials. Videos push PowerShell one-liners for “free” Windows or Adobe keys. These fetch and run AuraStealer silently. Loaders like Soulbind, Donut shellcode, and DLL side-loading spread it too, often into legit processes like regasm.exe.
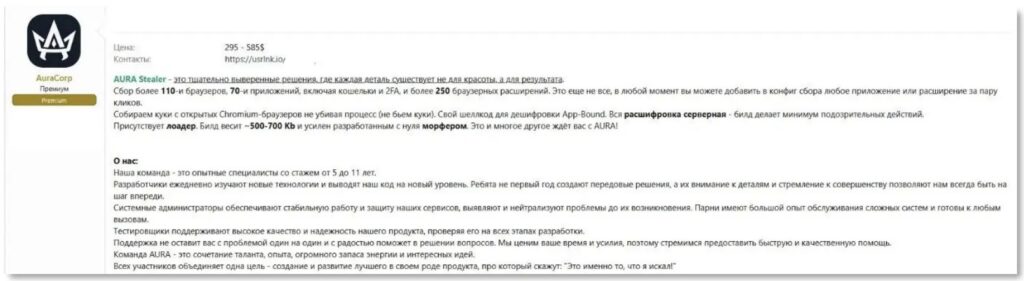
Stolen data includes creds, crypto wallets, 2FA tokens, Discord/Steam cookies, VPN configs, KeePass vaults, clipboard, and screenshots. Forum posts brag of switchers from Vidar and Rhadamanthys. Active users grow fast.
Intrinsec Statement: “AuraStealer uses 48 C2s across 200+ samples. Block .SHOP/.CFD domains immediately.”
Microsoft Advisory: “Monitor PowerShell abuse in ClickFix campaigns. Enable AMSI for script blocks.”
Malware Capabilities
| Feature | Targets |
|---|---|
| Browsers | 110+ (Chrome, Firefox, Edge, Safari) |
| Applications | 70+ (VPNs, password managers, messengers) |
| Extensions | 250+ (wallets, 2FA tools) |
| Exfiltration | Telegram bot, web panel |
| Pricing | Basic $295/mo, Advanced $585/mo |
Delivery chains mix social engineering with loaders. TikTok fakes lure admin PowerShell runs. No alerts show. Injections hit SndVol.exe or use fake Gcleaner tools.
Indicators of Compromise
- 48 C2 domains (.SHOP/.CFD via Cloudflare).
- Powershell downloads from video-linked sites.
- Process hollowing in regasm.exe, SndVol.exe.
- Soulbind loader network calls.
Block all known C2s at firewalls. Train staff on ClickFix video tricks. Limit PowerShell to signed scripts. Use app whitelisting.
Active Campaigns
- TikTok ClickFix for software cracks (Oct 2025).
- Loader chains with .NET DLLs.
- Forum sales to ex-Lumma users.
Endpoint tools must flag anomalous PowerShell and injections. Network blocks stop C2 chatter early.
FAQ
Infostealer hitting browsers, apps, and extensions with Telegram exfil.
ClickFix via TikTok, loaders like Soulbind, DLL side-loading.
Russian group “AuraCorp” selling since July 2025.
Creds, wallets, 2FA, cookies, screenshots.
48 identified, shifting .SHOP to .CFD.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages