BADIIS malware hijacks IIS servers in a global SEO-poisoning campaign

Security researchers say a malicious IIS module called BADIIS has been found on more than 1,800 Windows servers. The module silently alters responses for search engine crawlers so attacker sites rise in search results while normal visitors see the original pages. This lets criminals monetize compromised infrastructure by pushing users to gambling and cryptocurrency scam sites.
The discovery and analysis come from multiple labs. Elastic Security Labs published a deep dive after investigating a November 2025 intrusion. Their work ties the implant to a broader pattern of SEO abuse described earlier by other teams.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What to know first
BADIIS is a malicious IIS module that:
- injects SEO content only when it detects search engine crawlers, and
- serves clean content to regular users, hiding the compromise from human reviewers.
More than 1,800 servers were observed infected across regions, with a notable concentration in Asia-Pacific.
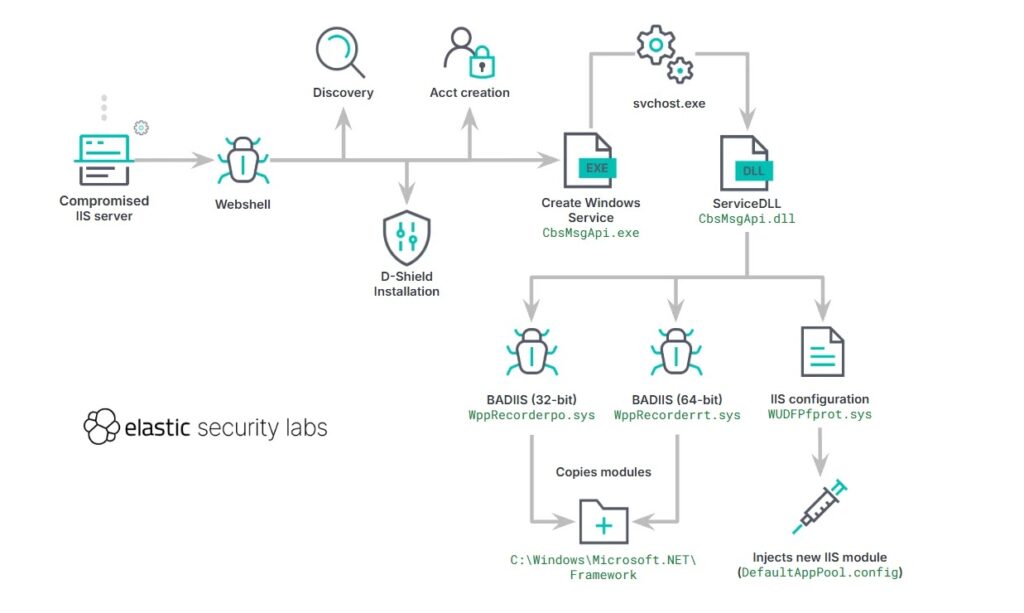
How the campaign works
- An attacker gains access to an IIS server, often by exploiting weak upload settings or a web shell.
- The actor installs BADIIS as a native IIS module so it runs inside the web server process.
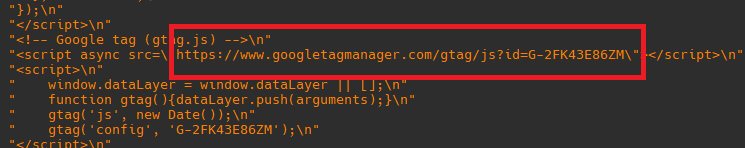
- The module inspects incoming requests. If it identifies a crawler such as Googlebot, it injects keyword-heavy pages or redirects the crawler to attacker sites. If not, it serves the original site.
- The attacker profits from higher search rankings and redirected traffic to scam destinations.
Who researchers link to the activity
Researchers attribute the activity to a Chinese-speaking actor cluster tracked by defenders as UAT-8099. UAT-8099 This group has previously targeted IIS servers for SEO fraud and credential theft. Cisco Talos and other teams have documented related tooling and tradecraft.
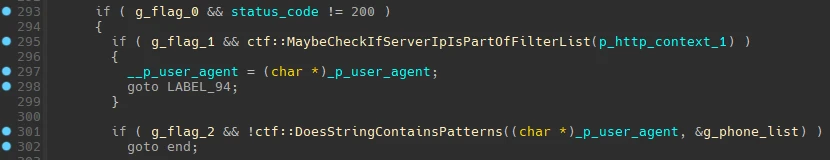
Why BADIIS is hard to spot
- It runs inside the legitimate IIS worker process, so endpoint agents that watch external processes may miss it.
- It shows different content to crawlers and to people, so basic site checks and manual reviews often fail to reveal the compromise.
- The module can intercept and modify HTTP responses in real time, enabling precise, contextual injection without disrupting normal traffic.
Indicators and defensive signals to watch
| Category | What to look for |
|---|---|
| IIS modules | Unexpected or unsigned native modules loaded into w3wp.exe |
| File changes | New DLLs or module files in C:\inetpub or module folders |
| HTTP behavior | Pages that differ when fetched with crawler user-agents vs normal user agents |
| Network | Outbound connections or redirects to new domains after crawler visits |
| Logs | Unexplained VM or host memory loads tied to IIS processes |
Practical mitigation checklist
- Audit installed IIS modules and remove any modules that are not signed or that you do not recognize.
- Harden file upload handlers and validate any user-supplied file paths on web servers.
- Monitor responses with crawler user agents (Googlebot, Bingbot) and compare them to responses for normal browsers. Alert on differences.
- Restrict administrative and file system write permissions for IIS service accounts.
- Patch servers and remove known web shells. Run a file integrity check against known good baselines.
- Use web application firewalls or reverse proxies that can detect injection and abnormal HTML modifications.
Real-world impact and scale
Elastic’s analysis and multiple industry reports place the number of affected servers in the low thousands, with one consolidated count above 1,800 infected hosts. The campaign targets high-visibility sites so that their ranking boost looks organic to search engines. That makes the abuse scalable and hard to attribute only by looking at search results.
Short glossary
- SEO poisoning : Manipulating search engine results to promote malicious sites.
- IIS module : A component loaded into Microsoft IIS that can inspect and change HTTP traffic. BADIIS uses this capability for covert injection.
- Crawler-aware delivery : Serving different content when the request looks like it came from a search engine crawler.
FAQ
A: Usually no. The malware serves the normal site to regular users. The main risk is that search results are poisoned and users are redirected after following search engine listings.
A: Reports show a mix that includes government, education, finance, and commercial sites. The Asia-Pacific region appears heavily targeted.
A: A web shell gives remote command execution. BADIIS is a native module that permanently modifies response behavior inside IIS, making detection different and often harder. Both can appear together in real campaigns.
A: Search engines have signals to detect cloaking and poisoning, and they take action when abuse is found. But cloaking that targets crawlers specifically is designed to evade casual detection and may persist until found and reported.
A: See the Elastic Security Labs writeup and related coverage by other vendors.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages