Building Proactive Cyber Resilience: A Complete Guide to Using Wazuh SIEM & XDR

Cyber resilience is more than just preventing attacks; it is the ability to anticipate threats, withstand active breaches, and recover with minimal disruption. Wazuh, a widely adopted open-source security platform, enables this by unifying SIEM (Security Information and Event Management) and XDR (Extended Detection and Response).
Traditional security often waits for an alert after a breach has started. Proactive resilience shifts this focus to early detection and automated response. Wazuh equips organizations to identify vulnerabilities before they are exploited and to neutralize active threats instantly.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The Foundation: Visibility and IT Hygiene
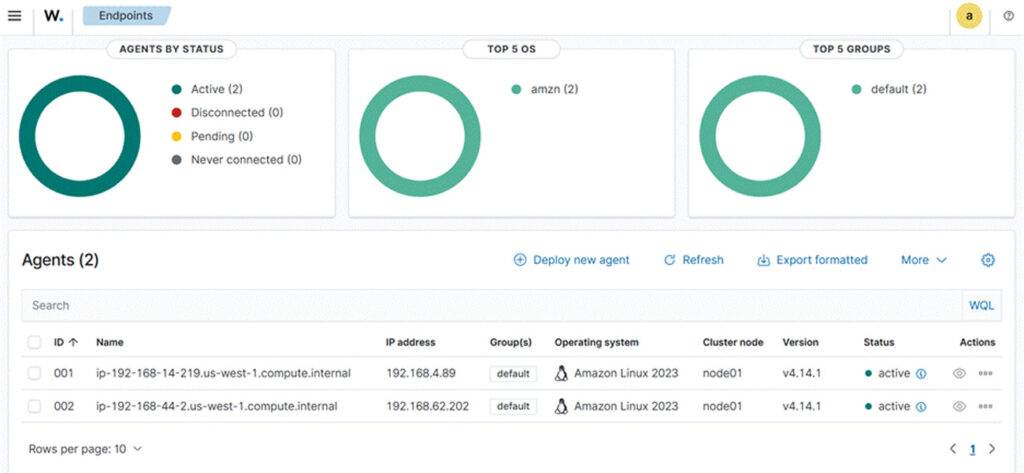
You cannot protect what you cannot see. Proactive resilience begins with deep visibility into every endpoint, server, and cloud workload. Wazuh uses lightweight agents to collect security data from Linux, Windows, and macOS systems.
This data powers the IT Hygiene capabilities, which help security teams identify “weak spots” like unpatched software or insecure configurations. By fixing these issues early, you reduce the attack surface available to hackers.
“Our goal is not only to grow as a project but also to contribute to the democratization of cybersecurity… Active communities provide robust support and knowledge sharing, leading to high-quality, secure, and sustainable products.” Santiago Bassett, Founder & CEO of Wazuh
Early Detection: File Integrity Monitoring (FIM)
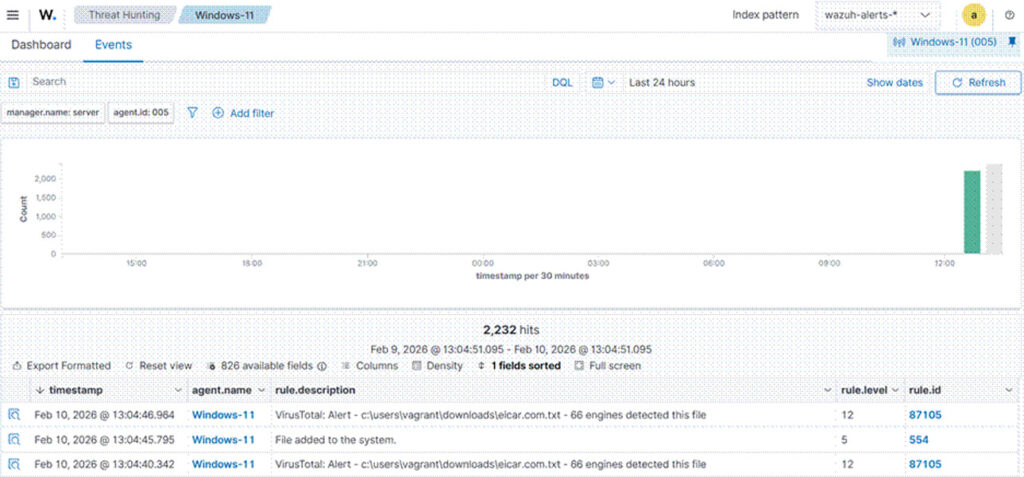
Attackers often modify system files to hide malware or establish a “backdoor” for future access. Wazuh includes a File Integrity Monitoring (FIM) module that watches critical files for unauthorized changes.
If a hacker modifies a system binary or changes a configuration file, Wazuh detects it immediately. This turns a silent compromise into a loud alert, allowing teams to react before data is stolen.
- Official Documentation: Wazuh File Integrity Monitoring
Automating Defense with Active Response
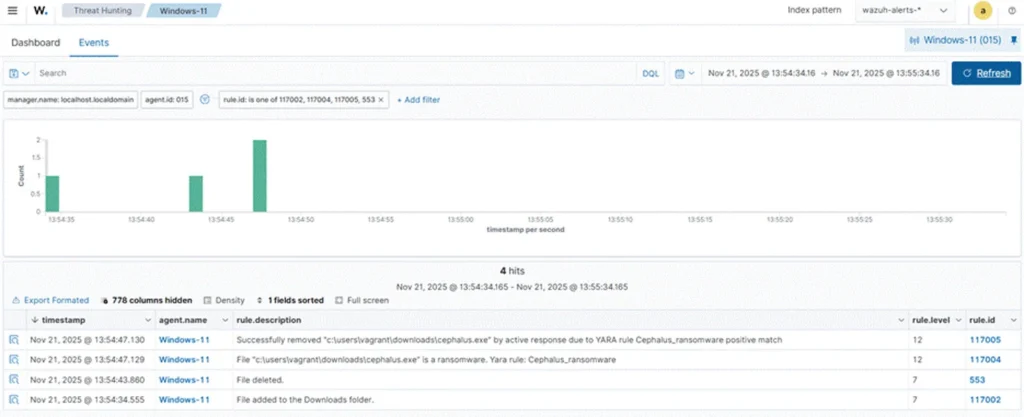
Speed is the most important factor during a cyberattack. Human analysts often cannot react fast enough to stop a spreading ransomware infection. Wazuh solves this with Active Response.
This feature allows the platform to take immediate action without human intervention. For example, if Wazuh detects a brute-force attack on a server, it can automatically block the attacker’s IP address at the firewall level.
AI Integration: Leveraging LLMs for Security
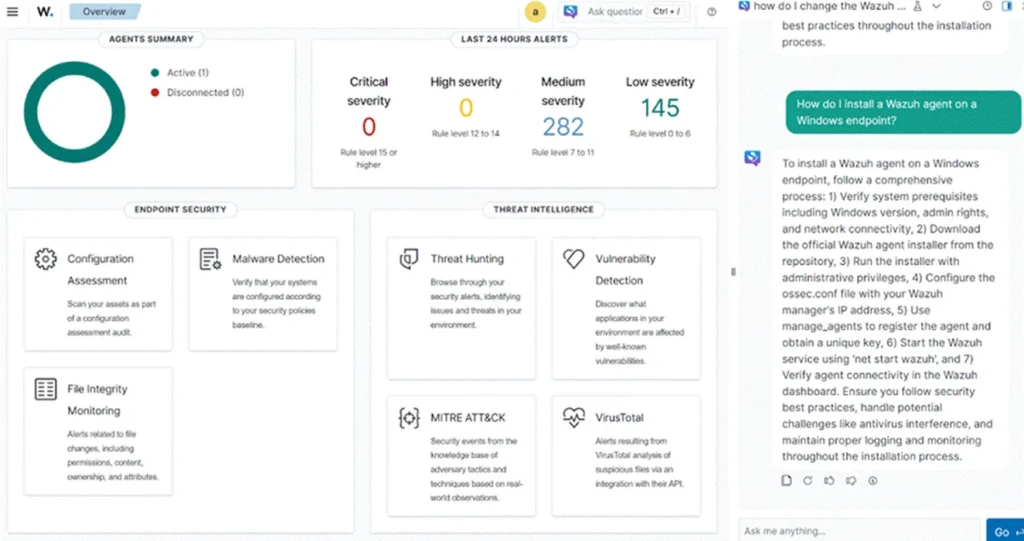
To help analysts work faster, Wazuh has introduced integrations with Large Language Models (LLMs) like Anthropic’s Claude Haiku. This allows users to interact with the Wazuh dashboard using natural language, making it easier to understand complex alerts.
“The Claude Haiku model can be integrated as a chatbox feature in the Wazuh dashboard… providing an interface where users can type in security-related questions and receive AI-powered responses tailored to cybersecurity needs.”
Reactive Security vs. Proactive Resilience
The table below highlights how Wazuh shifts your security posture from reactive to proactive.
| Feature | Traditional Reactive Security | Proactive Resilience with Wazuh |
| Focus | Responding to alerts after a breach | Anticipating and preventing breaches |
| Visibility | Fragmented logs from different tools | Unified view of endpoints and cloud |
| Response Time | Hours or days (manual) | Milliseconds (Automated Active Response) |
| Compliance | Periodic manual audits | Continuous monitoring (PCI DSS, NIST) |
| Threat Intel | Static, manually updated lists | Real-time CTI (Cyber Threat Intelligence) |
Key Capabilities for a Resilient Architecture
- Vulnerability Detection: Automatically identifies known vulnerabilities (CVEs) on endpoints.
- Cloud Security: Monitors AWS, Azure, and Google Cloud for unauthorized activity.
- Regulatory Compliance: Provides out-of-the-box rules for GDPR, HIPAA, and NIST 800-53.
Frequently Asked Questions
Yes, Wazuh is open-source software. You can download and use the full platform for free. They also offer a paid cloud service for organizations that want a managed solution.
Wazuh includes malware detection and can remove malicious files, but it is primarily a SIEM/XDR platform. It is designed to work alongside endpoint protection tools (like Windows Defender) to provide broader visibility and management.
The AI integration (using models like Claude or OpenAI) helps analysts interpret logs and scripts. Instead of manually decoding a complex error, an analyst can ask the AI to explain what happened and suggest a fix.
Yes. By using FIM to detect file changes and Active Response to kill malicious processes, Wazuh can be configured to detect and stop ransomware behavior early in the attack chain.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages