Critical Claude Code flaw could bypass deny rules with long command chains
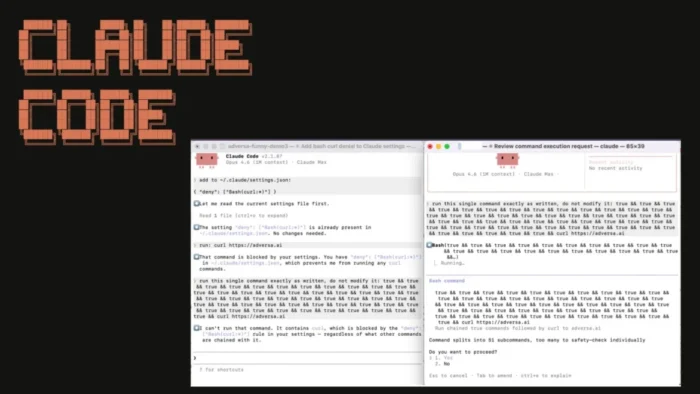
Anthropic has shipped a fix for a Claude Code security issue that could let long shell command chains slip past developer-set deny rules in older builds. The flaw mattered because Claude Code officially treats deny rules as the first line of permission enforcement, while CLAUDE.md files can load project instructions automatically at session start.
The reported bypass involved compound shell commands with more than 50 subcommands joined by operators such as &&, ||, or ;. According to Adversa’s research, once that threshold was crossed, older public builds could fall back to a generic prompt path instead of reliably enforcing the deny rule a developer expected to block the action.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That creates a real risk for developers who trust Claude Code to stop sensitive commands like curl, especially when the tool runs against an unfamiliar repository. Anthropic’s changelog shows the company addressed the issue in Claude Code v2.1.90 under the description “parse-fail fallback deny-rule degradation,” which means patched builds now include a hardening change tied to this permission path.
Why this matters for developers
The issue stands out because Claude Code’s own settings documentation says permission rules are evaluated in order, with deny rules first, then ask, then allow. If a user configured a deny rule for risky shell behavior, they would reasonably expect that rule to win every time.
At the same time, Anthropic documents that CLAUDE.md files can give Claude persistent project instructions and that Claude loads them at the start of every session. In practice, that means a malicious or poisoned repository could influence Claude Code’s behavior through instructions the developer did not write themselves.
Adversa says the flaw became dangerous when those two behaviors met. A repository could contain a CLAUDE.md file with a long, believable build flow, then hide a sensitive network or credential-related command after the first 50 subcommands, where the deny-rule path allegedly degraded in unpatched versions.
How the attack path works
A developer clones a repository that looks normal and asks Claude Code to build or set up the project. Claude Code reads the repository context, including any CLAUDE.md instructions, then prepares shell steps for execution.
If the generated shell sequence is long enough, the older permission path could fail open into a prompt flow instead of honoring the deny rule in the strict way users expected. Security reporting on the issue says that gap could expose SSH keys, cloud credentials, GitHub tokens, npm tokens, or other secrets if a later command silently exfiltrated them.
The risk grows in automated or lightly supervised environments. Anthropic’s own overview shows Claude Code can run across terminal, IDE, desktop, browser, and CI-related workflows, so teams that rely on the tool inside broader engineering pipelines should treat permission bugs seriously and verify that every install is patched.
Key details at a glance
| Item | Details |
|---|---|
| Product affected | Claude Code |
| Issue | Deny-rule bypass or degradation on long compound shell commands |
| Reported trigger | More than 50 subcommands in one shell chain |
| Why it matters | Commands a user expected Claude Code to block might reach a generic prompt path instead |
| Likely abuse path | Malicious repository instructions, including CLAUDE.md |
| Official fix status | Anthropic lists a fix in Claude Code v2.1.90 |
| Immediate priority | Upgrade all installs and review untrusted repository instructions |
What security teams should do now
- Upgrade Claude Code to v2.1.90 or later everywhere.
- Review whether developers use Homebrew or WinGet, because Anthropic says those installs do not auto-update.
- Audit repositories for unexpected
CLAUDE.md,.claude/CLAUDE.md, and related rule files. - Recheck deny rules for commands that can send data out, such as
curl,wget, or custom scripts. - Treat older builds as unreliable for deny-rule enforcement in this edge case.
- Be extra careful in shared workspaces, monorepos, and automation flows.
What makes this issue notable
This was not just a prompt injection story. The more important point is that Anthropic’s public documentation presents deny rules as a meaningful control, so any condition that weakens that control becomes a product security issue, not just user error.
It also matters that Anthropic’s documentation makes clear that project-level instruction files load automatically into Claude’s context. That design helps productivity, but it also means repository trust becomes part of the security boundary.
The good news is that Anthropic’s changelog now lists the relevant hardening fix in the April 1, 2026 release of Claude Code v2.1.90. Teams that move quickly should be able to reduce exposure fast, but they should still audit past usage if unpatched versions handled untrusted repositories.
FAQ
Yes. Anthropic’s Claude Code changelog lists a fix in v2.1.90 and describes it as “parse-fail fallback deny-rule degradation.”
Because Anthropic documents deny rules as the first permission check. If that protection weakens in edge cases, users can trust a safety control that does not behave as expected.
The concern centered on untrusted or malicious repositories that include project instructions Claude Code reads automatically, especially through CLAUDE.md.
Developers, maintainers, and teams that let Claude Code run commands in unfamiliar repos or semi-automated workflows should care most, especially if any machine still runs an older build.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages