DragonForce Ransomware Expands Cartel-Style Operations, Targets 363 Companies Since 2023
The DragonForce ransomware group has targeted 363 organizations between December 2023 and January 2026, according to multiple threat intelligence reports. Researchers say the group has evolved into a cartel-style Ransomware-as-a-Service operation, aggressively recruiting affiliates and expanding its technical capabilities. Attack volume has increased steadily, with 35 victims publicly listed in December 2025 alone, marking the group’s highest single-month activity to date.
DragonForce first emerged in late 2023 and has since built a reputation for structured operations, branding, and affiliate management. Security analysts describe it as more organized than many mid-tier ransomware groups. Its operators promote tools, infrastructure, and coordinated harassment tactics designed to increase payment pressure on victims.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This data highlights the group’s growing operational capacity and their intent to scale attacks against a broader range of industries.
What Security Researchers Say About DragonForce
“DragonForce, a Ransomware-as-a-Service group first observed in 2023, rose to greater prominence in 2025 after a series of notable attacks.” TrendMicro said.
Acronis described its evolution as follows: “DragonForce rebranded as a ransomware cartel, allowing affiliates to white-label payloads and create variants.”
LevelBlue researchers stated: “The Cybereason Threat Intelligence Team conducted an analysis of DragonForce, a ransomware group that emerged in late 2023 as a significant cyber threat actor.”
These official reports confirm DragonForce’s shift from a standard ransomware operation to a structured affiliate network with centralized coordination.
These official reports confirm DragonForce’s shift from a standard ransomware operation to a structured affiliate network with centralized coordination.
| Metric | Reported Figure |
|---|---|
| First observed | December 2023 |
| Total companies targeted (Dec 2023–Jan 2026) | 363 |
| Highest monthly victim count | 35 (December 2025) |
| Operational model | Ransomware-as-a-Service |
| Affiliate branding approach | Cartel-style ecosystem |
The upward trajectory suggests consistent affiliate onboarding and operational scaling.
How DragonForce’s Cartel Model Works
DragonForce promotes itself as a coordinated ransomware ecosystem rather than a single threat group. Its structure includes:
- Affiliate recruitment on dark web forums
- Custom payload builders
- White-label encryption options
- Centralized leak site operations
- Coordinated victim negotiation tactics
GBHackers reported that the group’s affiliate panel and “RansomBay” builder allow customized payload generation and automation of encryption routines.
The cartel approach enables affiliates to operate semi-independently while still leveraging shared infrastructure and branding.
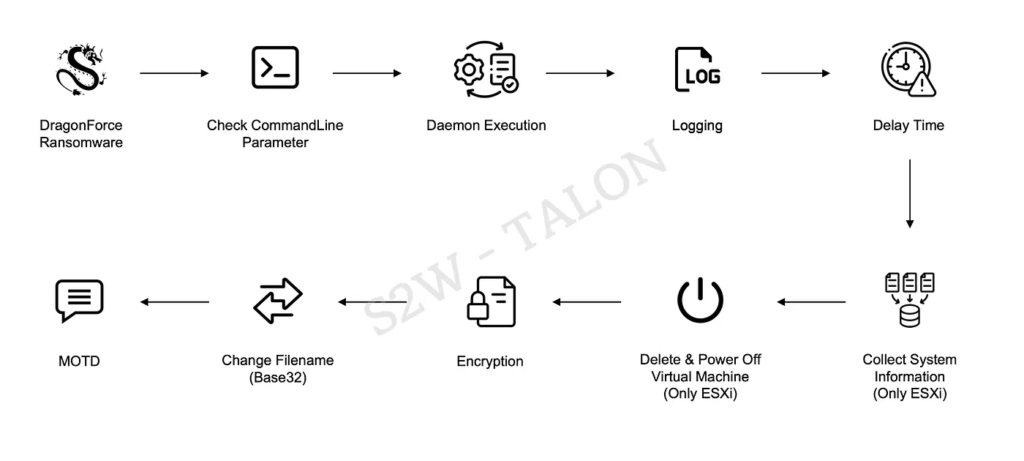
Technical Capabilities: Windows Binary Analysis
Recent research highlights several updates in DragonForce’s Windows ransomware builds.
Confirmed Technical Traits
- Use of Bring Your Own Vulnerable Driver (BYOVD) to disable security processes
- ChaCha-based configuration decryption prior to execution
- Adjustable encryption ratios
- Selective encryption modes based on file size
- Metadata expansion to 537 bytes in newer builds
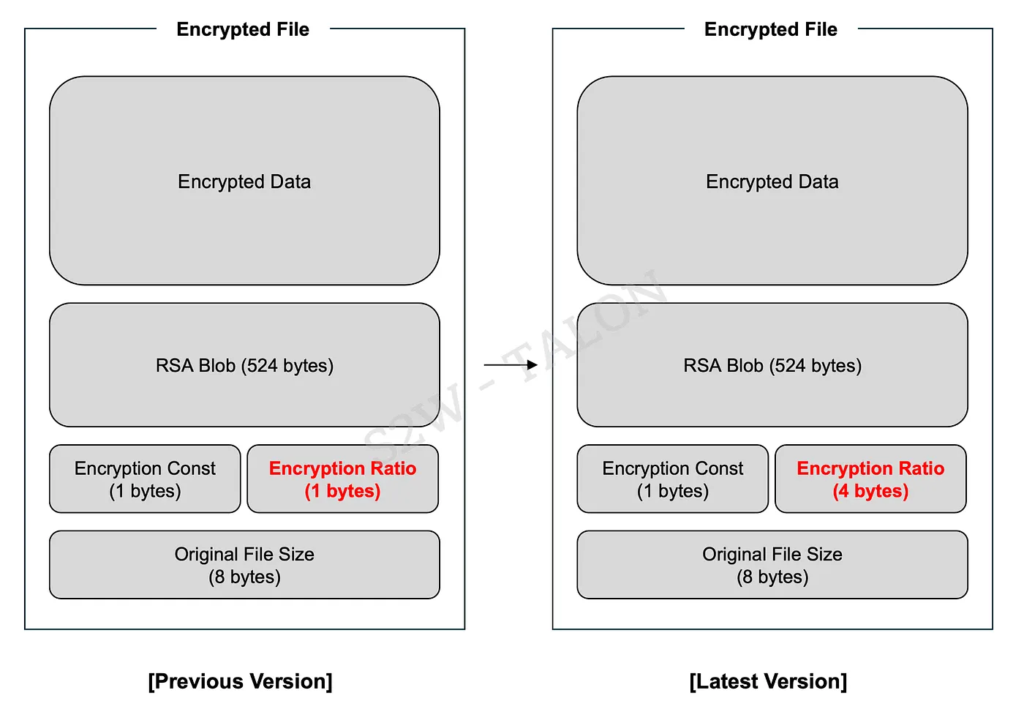
Security researchers note that the Encryption Ratio field expanded from one byte to four bytes, giving operators more granular control over file encryption strategies.
This allows attackers to balance encryption speed and impact depending on victim environment size.
Encryption Modes and Control Logic
DragonForce operators can choose between:
- Full encryption
- Partial encryption
- Header-only encryption
If no custom rule is defined, the malware automatically selects the encryption method based on file size thresholds.
This adaptive control model improves operational efficiency and reduces detection windows during active attacks.
Ecosystem Strategy and Rivalries
DragonForce has also engaged in adversarial relationships with competing ransomware groups. Analysts report:
- Infrastructure attacks against rivals
- Attempts to absorb affiliates from other RaaS programs
- Branding campaigns promoting dominance in the RaaS market
Cyble notes that DragonForce’s growth reflects a broader consolidation trend in ransomware ecosystems.
This behavior aligns with cartel-style expansion strategies seen in other organized cybercrime operations.
Why DragonForce Matters in 2026
DragonForce represents a mature RaaS ecosystem rather than a single malware strain. Its model includes:
- Structured affiliate governance
- Technical customization
- Psychological pressure tactics
- Centralized branding
- Cross-forum recruitment
The 363 confirmed targets in just over two years show sustained operational momentum rather than short-term spikes.
Defensive Recommendations
Organizations should prioritize:
- Strict driver monitoring to detect BYOVD abuse
- Endpoint detection capable of spotting partial encryption patterns
- Monitoring for unusual file metadata appended during encryption
- Network segmentation to limit lateral movement
- Proactive dark web monitoring for leak site listings
Continuous monitoring and patch discipline remain critical.
FAQ
DragonForce is a Ransomware-as-a-Service group first observed in December 2023 that operates through a cartel-style affiliate model.
Reports indicate 363 organizations between December 2023 and January 2026, with 35 victims published in December 2025 alone.
Its cartel branding, white-label encryption builder, BYOVD usage, and expanded encryption control options distinguish it from smaller RaaS operations.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages