Fake ChatGPT Android test invites are stealing Facebook logins through Google’s Firebase service

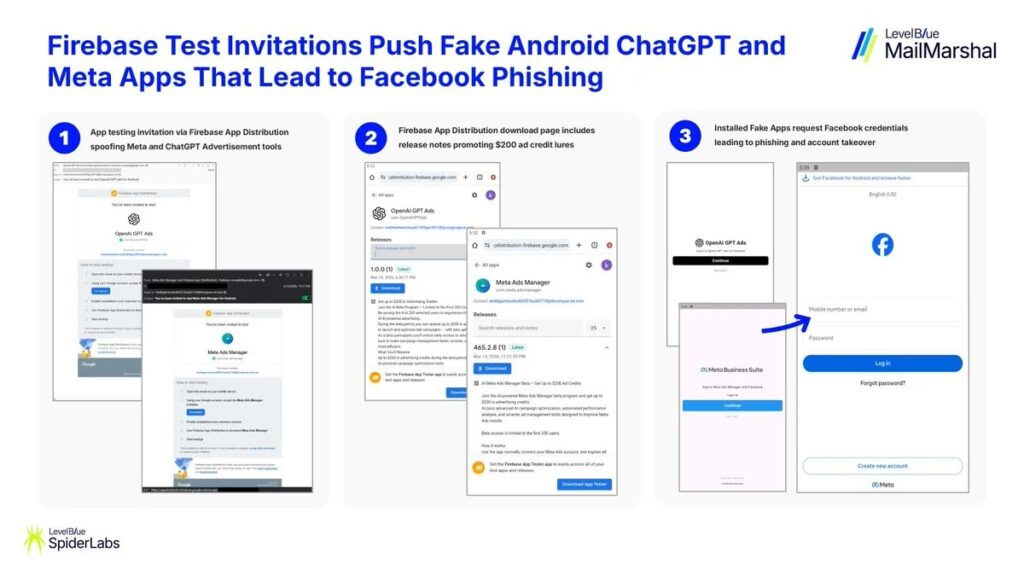
Android users are getting fake beta invitations for ChatGPT and Meta advertising apps, and some of those invites lead to malicious APKs that steal Facebook credentials. The campaign abuses Firebase App Distribution, a real Google service that developers use to send pre-release builds to testers, which gives the emails and download flow a layer of legitimacy.
The result is a phishing operation that looks more convincing than a normal fake app scam. Instead of sending victims to a random download page, the attackers use Firebase’s testing workflow, where invited users can receive build notifications and install Android APKs outside Google Play. Google’s own documentation confirms that Firebase App Distribution lets developers upload APKs and email testers directly.
According to SpiderLabs, the Android campaign uses invitations for fake ChatGPT and Meta ad-related apps and pushes victims toward malware delivered through Firebase App Distribution. Reporting on the campaign says the malicious apps use names such as com.OpenAIGPTAds, com.opengpt.ads, and com.meta.adsmanager, then present a Facebook login screen to capture credentials for account takeover.
Why this campaign works so well
The main trick is trust. Firebase App Distribution is a legitimate Google product for app testing, and Google’s documentation says testers receive invitation emails and can install pre-release Android builds from that workflow. That means a victim may see a genuine Google-related sender flow and a real Firebase landing page, even though the app behind it is malicious.
That also helps attackers avoid one of the biggest warning signs in mobile phishing. Many users know to distrust sketchy download sites. Fewer people expect abuse inside a real app testing system. If the victim already works with beta apps, the invitation can look routine.
The operation also follows a pattern security teams have watched for months. SpiderLabs said this Android wave came after a related iOS campaign that used fake AI-branded apps. The broader goal appears to stay the same across both platforms: steal Facebook credentials, grab access to business assets, and abuse trusted brands to improve click-through and install rates.
How the attack unfolds
Victims receive an invitation email that looks like a normal testing request.
They click through to a Firebase-hosted testing page.
They install an Android APK outside the Play Store.
The app opens what looks like a Facebook login page.
The victim enters credentials, and the attacker captures them.
In reported cases, the fake apps posed as ChatGPT or Meta ad-related tools rather than delivering any real AI or marketing features.
What makes Firebase part of the story
This incident does not mean Firebase itself is malware. It means attackers appear to be abusing a legitimate distribution channel the way criminals abuse cloud storage, trusted email platforms, and ad networks.
Google describes Firebase App Distribution as a way to distribute pre-release apps to trusted testers, either individually or through groups. Developers can upload APKs, invite testers by email, and make builds available for installation before public release. That design is useful for software teams, but it also creates room for social engineering if an attacker controls the project and the invite list.
Reported indicators tied to the campaign
Reporting on the campaign linked it to several suspicious domains and app identifiers. These reported indicators include the following:
| Type | Reported indicators |
|---|---|
| Package names | com.OpenAIGPTAds, com.opengpt.ads, com.meta.adsmanager |
| Domains | thcsmyxa-nd[.]com, moitasec[.]com, tourmini[.]site, ocngongiare[.]com, disanviet[.]homes, itrekker[.]space |
These details come from reporting that cited SpiderLabs’ findings. I could confirm SpiderLabs’ public warning about the Android Firebase campaign, but I could not independently verify every domain from a primary public LevelBlue research page that was accessible through web search.
What Android users should do now
Anyone who receives an unexpected app-testing invite for ChatGPT, Meta Ads, or similar tools should stop and verify it through a separate channel.
Security teams and users should take these steps:
- Avoid installing APKs from unsolicited testing invites
- Download ChatGPT and Meta apps only from official stores or verified enterprise channels
- Treat Firebase-based beta invites with caution if you did not expect them
- Never enter Facebook credentials into a newly installed test app
- Turn on two-factor authentication for Facebook and Meta business accounts
- Review recent logins and ad account activity for anything unusual
- Block reported malicious domains and investigate devices that installed unknown APKs
These steps line up with the campaign’s reported goal of stealing Facebook credentials and hijacking business or advertising accounts.
Why this matters beyond one fake ChatGPT lure
This campaign shows how attackers keep moving closer to legitimate software delivery channels. Old phishing kits relied on fake sender names and crude landing pages. Newer operations abuse real infrastructure, real brands, and real user habits.
For defenders, that means the old advice still matters, but it no longer covers enough ground on its own. A message can come through a real service and still lead to malware. A testing flow can look authentic and still end in credential theft. In mobile security, trusted delivery has become part of the attack surface.
FAQ
The campaign reportedly uses Firebase App Distribution, which is a real Google service for sending pre-release app builds to testers. That is what makes the invitation flow look more legitimate.
No evidence in the sources I reviewed shows that OpenAI’s official Android app was compromised. The campaign uses fake ChatGPT branding to trick users into installing malicious APKs.
The reported goal is Facebook credential theft and account takeover, especially for users tied to business and advertising accounts.
Firebase App Distribution is meant for pre-release testing and allows APK distribution outside the Play Store review path. Google documents that developers can upload APKs and invite testers directly.
Do not install the APK. Verify the sender through a separate trusted channel, and change your Facebook password immediately if you already entered it into one of these apps.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages