Fake Claude Code download pages push MSHTA infostealer at developers, researchers warn

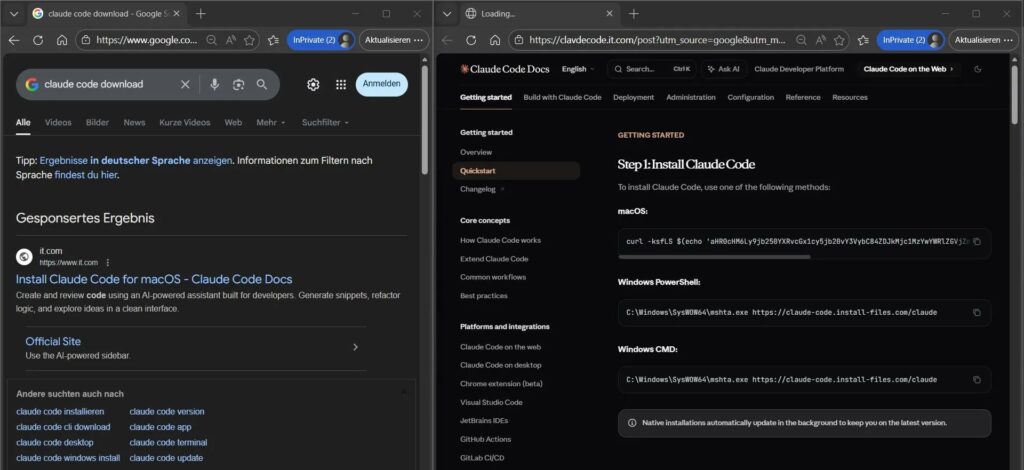
Threat actors have started abusing fake “Claude Code” download pages to infect developers and IT professionals with an infostealer. The sites imitate legitimate Anthropic branding and install guidance, then lead victims into launching Windows mshta.exe to execute a remotely hosted HTA payload that steals credentials, browser data, and session tokens.
Researchers describe this as a “living off the land” style attack because it relies on a trusted Windows binary instead of a conventional installer. MITRE tracks this abuse pattern under System Binary Proxy Execution: Mshta (T1218.005).
Security analyst Maurice Fielenbach documented one chain where victims reached lookalike domains that served “Claude Code” themed download prompts and ended with mshta.exe fetching malicious content from a remote URL. He also notes that similar lure patterns have targeted users of popular AI tools in recent months.
How the fake download scam works
Attackers set up convincing landing pages that resemble real software portals, often using wording and layout that look familiar to developers. Victims click a download button or follow “install” instructions, then the page nudges them into running a Windows-native command or opening a file that triggers mshta.exe.
Once mshta.exe runs, it can execute script content hosted on an external site, which helps the attacker avoid dropping a traditional executable to disk. That makes triage harder and can reduce detections in environments that do not monitor mshta.exe closely.
Quick comparison: real Claude Code sources vs common impostor signals
| Check | What a legitimate source looks like | What scam pages often do |
|---|---|---|
| Domain | Official Anthropic properties and docs | Lookalike domains with extra words, odd subdomains, or typos |
| Install method | Clear guidance in official docs and product pages | “Copy this command” style prompts hosted on unrelated domains |
| Execution flow | Normal installers or documented CLI flows | Pushes mshta.exe to pull remote script content |
Why defenders care about mshta.exe in this campaign
Mshta.exe exists on Windows by default and can run HTML Application content outside the browser security context. Attackers like it because it can proxy execution of scripts in ways that blend into normal system activity unless logging and controls catch it.
MITRE’s technique entry for T1218.005 highlights that mshta.exe can bypass some application control approaches when defenders do not account for it. That lines up with the “fileless” behavior researchers describe in these Claude Code themed lures.
What to do if your team might have clicked or run it
- Disconnect the affected device from the network (Wi-Fi and Ethernet).
- Collect basic evidence fast (URL, downloaded filename, timestamp, and any observed prompts).
- Check endpoint telemetry for mshta.exe spawning with an external URL in its arguments, then treat it as high priority.
- Reset passwords and rotate tokens from a known-clean device, especially developer and cloud credentials.
- Review active sessions for developer tools and identity providers, then revoke unknown sessions where possible.
Hardening steps that reduce risk quickly
- Turn on Attack Surface Reduction (ASR) rules in audit first, then block where safe, since Microsoft designed ASR to prevent malware from abusing apps and scripts for execution.
- Add detections for mshta.exe with network-based arguments and remotely hosted HTA execution, since MITRE publishes detection guidance for suspicious mshta invocation patterns.
- Train developers to treat “copy this command to install” prompts as suspicious unless they come from official vendor documentation pages.
FAQ
Claude Code is Anthropic’s coding assistant that integrates with developer workflows, including terminal and IDE usage, according to Anthropic’s product and documentation pages.
Infostealers can capture browser credentials, session tokens, and access to developer services, which can open paths into source code, CI/CD, and cloud environments. Researchers warn that this creates organization-wide risk when a single workstation gets compromised.
Mshta.exe runs Microsoft HTML Application files and can execute script content, which attackers can abuse to run code fetched from a remote server. MITRE tracks this abuse as technique T1218.005.
Many teams start by monitoring and alerting, then apply controls such as Microsoft Defender ASR rules in audit mode first to understand impact before enforcing block.
Use Anthropic’s official download page and official Claude Code documentation, and avoid third-party download portals or sponsored lookalike results when you can.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages