Fake TradingView Premium posts on Reddit spread Vidar and AMOS stealers
A live malware campaign is using fake Reddit posts that promise free TradingView Premium access to infect victims with Vidar on Windows and Atomic macOS Stealer, also known as AMOS, on Macs. The campaign targets traders, crypto users, and anyone looking for cracked premium software.
According to the research cited in current coverage, the attackers used Reddit posts and aged accounts to make the scam look legitimate, then pushed victims to download malicious files from unrelated external sites. The Windows payload delivered Vidar, while the macOS version delivered AMOS, a well-known infostealer that targets browser data, credentials, cookies, and wallet-related information.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign matters because it combines a familiar lure with cross-platform malware delivery. It also shows how attackers continue to abuse trusted communities and popular software brands to steal credentials, session tokens, and crypto wallet data.
How the Reddit lure works
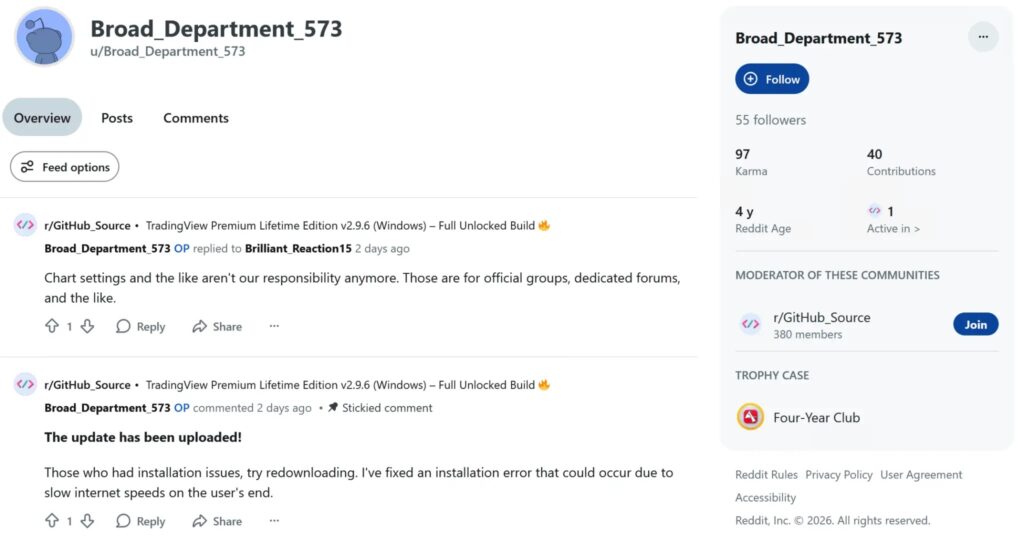
The scam offers a simple pitch: download a “cracked” version of TradingView Premium for free. Current reporting says the posts appeared across multiple subreddits and used older Reddit accounts to create a false sense of trust.
Researchers said the operation showed clear discipline. When domains got flagged, the actor swapped them out quickly, while warning comments from real users were reportedly removed just as fast. That suggests an active campaign, not an abandoned one-off post.
The lures also separated downloads by platform, including distinct options for Windows and macOS. That kind of targeting increases the chance that victims will run the file instead of abandoning the install halfway through.
Campaign snapshot
| Item | Details |
|---|---|
| Main lure | Fake free TradingView Premium downloads |
| Distribution channel | Reddit posts and subreddit activity |
| Windows payload | Vidar infostealer |
| macOS payload | AMOS, also called Atomic macOS Stealer |
| Main targets | Traders, crypto users, retail investors |
| Main goal | Steal credentials, cookies, session data, and wallet files |
What happens on Windows and macOS
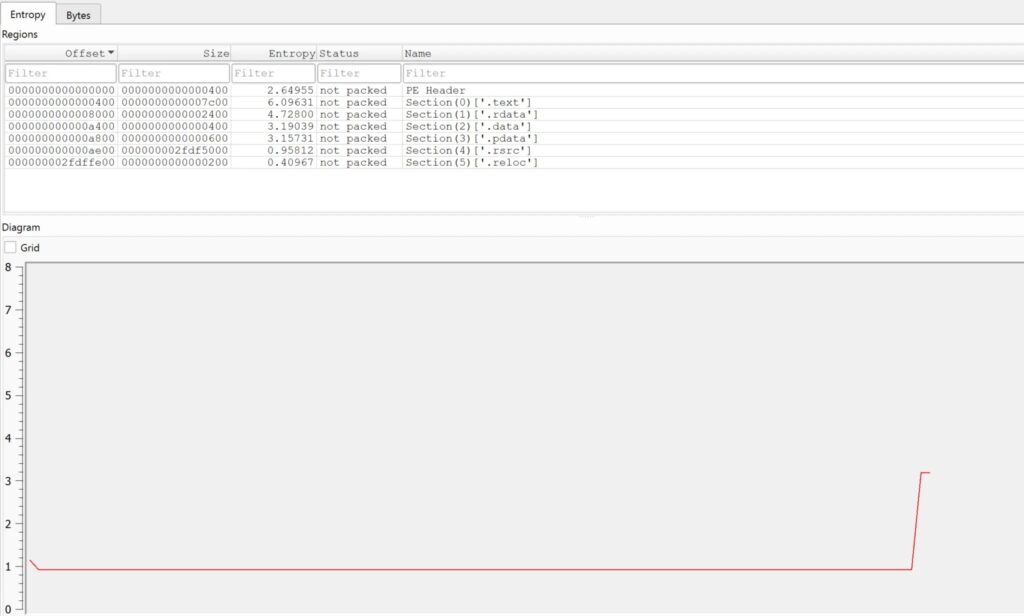
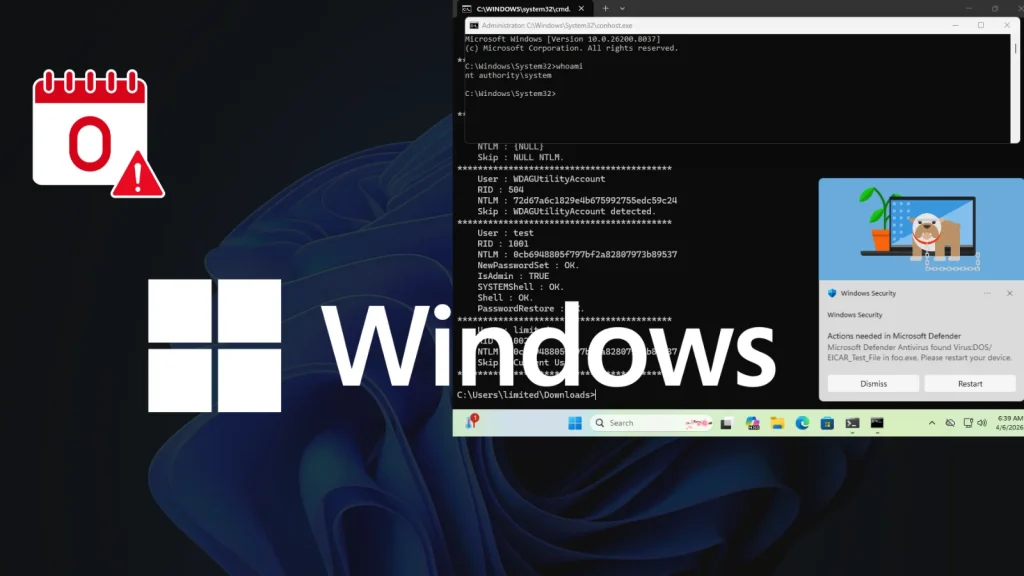
On Windows, the downloaded file reportedly used heavy padding to grow far beyond normal size, which can help malware avoid some scanning workflows. Current coverage says the real payload sat inside a smaller self-extracting archive that rebuilt Vidar through an obfuscated script.
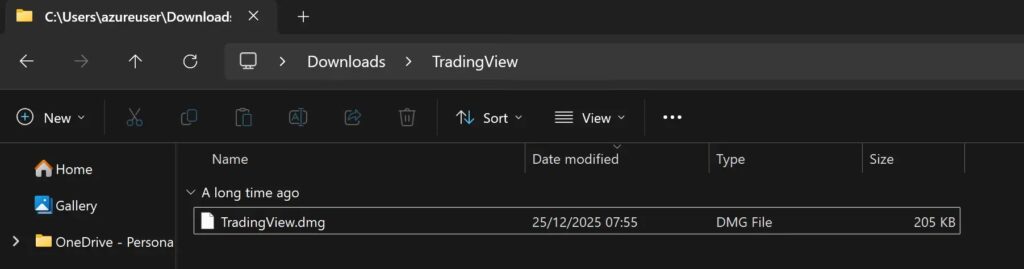
On macOS, the lure arrived as a disk image that looked like a branded TradingView installer. Reporting says the payload decrypted and launched AMOS at runtime, then harvested data from browsers and crypto wallet software.
Microsoft’s recent guidance on macOS infostealers matches that pattern closely. The company says modern stealers target browser data, cookies, saved credentials, keychains, and developer or wallet-related secrets, often by abusing trusted-looking delivery channels and native utilities.
Why this campaign is dangerous
This is not just about one fake download. Infostealers often turn a single careless install into account theft across email, trading platforms, cloud tools, browsers, and crypto wallets. Microsoft also notes that stolen credentials and session data can fuel later account takeovers and broader attacks.
The macOS side also matters more than many users assume. Apple says Gatekeeper checks downloaded software for known malware and certificate issues, but attackers still try to work around that protection by using convincing branding and social engineering to get users to run risky apps.
Cracked software remains one of the easiest ways for criminals to reach victims because the victim often disables their own caution. Once that happens, the attacker no longer needs a browser exploit or a phishing login page. The victim installs the malware for them. This last sentence is an inference based on the campaign design and Microsoft’s explanation of trojan behavior.
Main warning signs
- Reddit posts offering free premium software or cracked tools should be treated as high risk.
- Large ZIP files or installers downloaded from unrelated domains deserve immediate suspicion.
- Branded macOS disk images do not prove that an app is safe or signed. Apple says Gatekeeper still checks whether software is signed and notarized.
- Infostealers often go after browser credentials, cookies, and wallet data first.
What users and organizations should do now
Anyone who downloaded one of these fake TradingView builds should assume compromise until proven otherwise. That means changing passwords, rotating saved credentials, signing out of active sessions, and moving crypto assets to clean wallets if wallet files or seed material may have been exposed. This recommendation follows directly from the reported stealer behavior and official infostealer guidance.
Organizations should block the known distribution domains, review proxy and DNS logs, and hunt for suspicious sequences such as Reddit browsing followed by large downloads from unrelated sites. On endpoints, defenders should also watch for unusual child processes, unsigned apps, and signs of credential dumping or browser data theft.
Apple recommends opening apps only from trusted sources, and Microsoft advises defenders to watch for malware that masquerades as legitimate software to trick users into installation. Those basic rules still matter because this campaign relies on trust and curiosity more than technical novelty.
Response checklist
| Priority | Action | Why it matters |
|---|---|---|
| High | Stop using the downloaded file immediately | Prevents further execution or reinfection |
| High | Change passwords and revoke active sessions | Stealers often grab credentials and cookies |
| High | Move sensitive crypto assets from exposed wallets | Wallet files may have been copied |
| Medium | Scan the device and review browser-stored secrets | Helps scope the damage |
| Medium | Block related domains and inspect DNS or proxy logs | Can reveal more victims |
| Medium | Reinstall from clean sources if compromise is confirmed | Reduces the chance of persistence |
Bottom line
This Reddit campaign worked because it used a believable lure, familiar branding, and platform-specific malware. Victims thought they were getting premium charting software for free, but they were really handing over credentials, cookies, and wallet data.
The broader lesson is simple. If a download promises paid software for nothing, especially through Reddit or another community post, you should assume the real product is malware until proven otherwise. That conclusion fits both the reported campaign and Microsoft’s official description of trojans that pretend to be harmless software.
For traders, crypto users, and teams that manage financial accounts, this kind of infostealer campaign can lead to immediate losses. A single install can expose browser sessions, passwords, and wallet data within seconds.
FAQ
Current reporting says the Windows payload delivered Vidar, while the macOS version delivered AMOS, also called Atomic macOS Stealer.
The campaign mainly targeted retail traders, crypto users, and people looking for free or cracked TradingView Premium downloads on Reddit.
No. Apple says Gatekeeper checks downloaded software for known malware and signing or notarization status, but users can still face risk from convincing lures and unsafe app-opening choices.
Treat the device as compromised, change passwords, revoke sessions, scan the machine, and move sensitive financial or wallet assets to clean environments. This is based on the reported stealer behavior and official infostealer guidance.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages