Google: “Coruna” iPhone exploit kit used 23 exploits across five chains in 2025

Google’s Threat Intelligence Group (GTIG) says it uncovered a powerful iOS exploit kit called Coruna that attackers used to compromise iPhones running iOS 13.0 through iOS 17.2.1 during 2025. GTIG says Coruna includes five full exploit chains and 23 exploits, and it can infect a device when a user visits a website that serves the malicious framework.
GTIG tracked Coruna moving through three different threat ecosystems in 2025. Google first saw it in February 2025 in activity linked to a customer of a surveillance company, then in summer 2025 in watering-hole attacks against Ukrainian users tied to a suspected Russian espionage cluster Google tracks as UNC6353, and later in 2025 in broad campaigns linked to a China-based financially motivated cluster Google tracks as UNC6691.
Apple has already patched the underlying vulnerabilities over time, and GTIG says Coruna does not work against the latest iOS version. Google says users should update iPhones immediately and use Lockdown Mode if they cannot update.
What makes Coruna different from typical iPhone malware
Coruna is not a single exploit or a single spyware implant. GTIG describes a modular kit with a delivery framework that fingerprints the device, picks the right chain for the exact iPhone model and iOS version, then runs WebKit code execution plus post-exploit payloads.
The kit also includes operational safeguards that you usually see in higher-end exploitation. Google says Coruna stops if it detects Lockdown Mode or Private Browsing, and it uses encrypted blobs and custom resource addressing to hide stages of the chain.
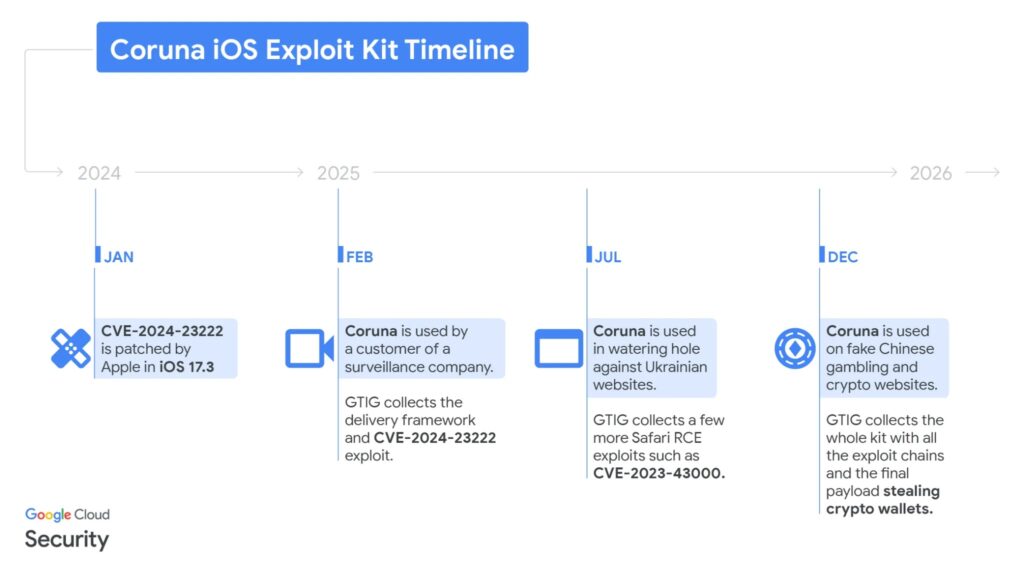
Timeline GTIG published for Coruna’s spread in 2025
| Period | GTIG summary | What changed |
|---|---|---|
| February 2025 | Partial chain used by a customer of a surveillance company | First capture of the JavaScript framework and WebKit exploit delivery |
| Summer 2025 | Watering-hole activity on compromised Ukrainian sites attributed to UNC6353 | Same framework hosted on cdn.uacounter[.]com and delivered by hidden iframes to selected geolocations |
| Late 2025 | Broad campaigns on fake Chinese finance and crypto sites attributed to UNC6691 | Delivery expanded and did not rely on geolocation targeting |
What GTIG says the exploit chains include
GTIG’s table lists multiple WebKit remote-code-execution and memory corruption exploits, PAC bypass components, sandbox escapes, privilege escalation, and PPL bypass pieces. Google also cautions that the investigation remains ongoing and some CVE associations may change as analysis continues.
Here are some of the CVEs GTIG highlights in its published table and narrative:
| Exploit type | Codename | Targeted iOS versions | CVE |
|---|---|---|---|
| WebContent R/W | buffout | 13 → 15.1.1 | CVE-2021-30952 |
| WebContent R/W | jacurutu | 15.2 → 15.5 | CVE-2022-48503 |
| WebContent R/W | terrorbird | 16.2 → 16.5.1 | CVE-2023-43000 |
| WebContent R/W | cassowary | 16.6 → 17.2.1 | CVE-2024-23222 |
| WebContent sandbox escape | IronLoader | 16.0 → 16.3.1 and 16.4.0 (≤ A12) | CVE-2023-32409 |
GTIG says it first recovered the WebKit exploit for CVE-2024-23222 on iOS 17.2 and notes Apple addressed it in iOS 17.3 on January 22, 2024.
iVerify: evidence suggests mass exploitation by criminals
Mobile security firm iVerify says it independently analyzed the same framework and describes it as the first observed mass exploitation of mobile phones, including iOS, by a criminal group using tools likely built by a nation-state. iVerify says its analysis corroborates and extends Google’s reporting, and it observed infections on multiple iOS versions and devices using watering-hole style delivery without one-time links.
iVerify also says it could reinfect test devices multiple times by revisiting the malicious sites, which fits Google’s warning that the exploit kit can be delivered through compromised or fake websites.
Who built Coruna
Google does not publicly name the developer of the kit, and it does not claim a specific government built it. GTIG says it first saw the chain used by a customer of a surveillance company, then later saw it reused by different actor clusters, which points to proliferation and resale.
iVerify says it has some evidence suggesting the framework resembles tooling previously attributed to U.S.-affiliated threat actors, but it frames that as an assessment rather than a confirmed attribution.
Kaspersky researchers pushed back on strong U.S. attribution narratives, arguing that shared vulnerabilities do not prove code reuse and that skilled teams can build their own exploits once details become public.
What iPhone users and security teams should do now
- Update iPhones to the latest iOS available. Google says Coruna does not work against the latest iOS version.
- Turn on Lockdown Mode if you cannot update and you face elevated risk. Apple says Lockdown Mode reduces attack surface against rare, sophisticated threats.
- Avoid unverified finance, crypto, and gambling sites, especially on older iOS devices. GTIG says it recovered full chains from large sets of fake finance websites that pushed iOS users to visit.
- For defenders, hunt for web-based delivery patterns, including hidden iframes and suspicious resource fetching that matches GTIG’s described framework behavior.
FAQ
GTIG says Coruna targeted iPhones running iOS 13.0 up to 17.2.1, spanning releases from September 2019 through December 2023.
GTIG says infection could happen when a user visited a website that delivered a hidden iframe and the exploit framework, including watering-hole style delivery on compromised sites and large networks of fake finance sites.
GTIG says Coruna is not effective against the latest version of iOS and urges users to update.
Apple says Lockdown Mode provides extreme protections designed for a small set of users at risk from highly sophisticated attacks, and GTIG says Coruna stops when it detects Lockdown Mode.
No. GTIG describes how the kit spread across multiple threat actor ecosystems but does not publicly name the original developer.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages