Google tracked 90 exploited zero-days in 2025, with enterprise targets rising fast

Google says 90 zero-day vulnerabilities were exploited in real-world attacks during 2025, and nearly half of them hit enterprise software and appliances. That matters because these products often sit deep inside company networks and can give attackers privileged access if breached.
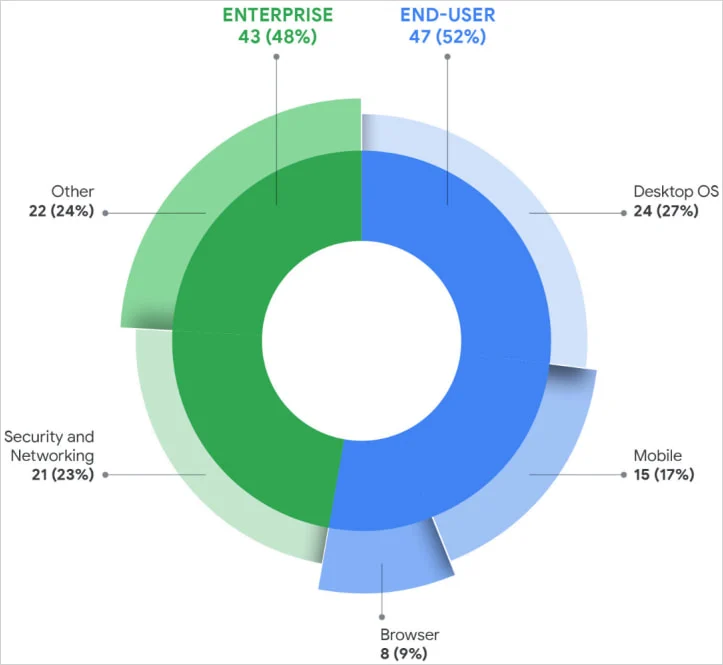
The big shift is not only the total number. Google says enterprise targeting reached a new high, with 43 of the 90 tracked zero-days affecting enterprise software and appliances, while 47 hit end-user platforms and products. In other words, attackers kept going after phones, desktops, and browsers, but they also pushed harder into security tools, networking gear, edge devices, and other business-critical systems.
Google’s latest report also adds an important caveat that many summaries leave out. The company says zero-day tracking changes over time as older incidents come to light, so the numbers reflect its best current view rather than a final universal count. That helps explain why Google’s new 2025 report compares 2025’s 90 zero-days against 78 in 2024, while Google’s own 2024 review had earlier put that 2024 total at 75.
What Google found
| Metric | Google’s 2025 finding |
|---|---|
| Total exploited zero-days tracked in 2025 | 90 |
| End-user platforms/products | 47 |
| Enterprise software/appliances | 43 |
| Enterprise share of total | 48% |
| Total OS-related zero-days | 39 |
| Mobile zero-days | 15 |
| Financially motivated zero-days attributed | 9 |
| China-linked state espionage zero-days attributed | At least 10 |
Google says 2025 stayed within the elevated 60 to 100 annual range it has seen in recent years. So while the total did not break the 2023 peak of 100, the company sees no sign that the zero-day problem is fading away.
Why enterprise systems drew so much attention
Google says 48% of 2025’s exploited zero-days targeted enterprise-grade technology, which set a new high. The report points to security and networking products as a major weak point because they sit at the edge of the network, hold high privileges, and often lack endpoint detection and response coverage.
That pattern fits what defenders have warned about for years. If attackers compromise a VPN gateway, firewall, router, hypervisor, or other edge-facing system, they can often move quietly and stay inside the environment longer. Google specifically notes that security and networking vulnerabilities made up about half of all enterprise-related zero-days it tracked in 2025.
CISA has pushed the same broader message through its Known Exploited Vulnerabilities program. The agency says organizations should use the KEV catalog to prioritize remediation, and its directive on known exploited bugs focuses on reducing the risk from flaws already under active attack.
Browsers cooled off, but operating systems did not
One of the clearest changes in Google’s data involves browsers. The company says browser exploitation fell below 10% of tracked 2025 zero-days, a sharp drop from the browser-heavy years of 2021 and 2022. Google believes browser hardening helped, although it also says stronger attacker operational security may make some abuse harder to spot.
At the same time, operating systems became the biggest target category. Google says OS-related flaws accounted for 39 of the 90 tracked zero-days in 2025, including 15 in mobile platforms. That reflects how much value attackers still get from compromising the software layer that controls the whole device.
Memory corruption remained a major issue too. Google says memory safety bugs, especially use-after-free and out-of-bounds write flaws, accounted for roughly 35% of the vulnerabilities in its 2025 dataset.
Who drove the attacks
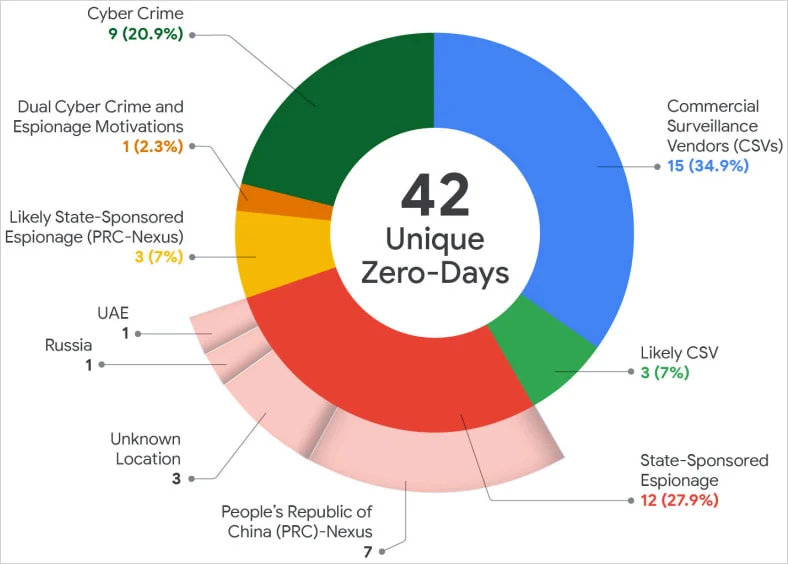
A major headline from Google’s report is that commercial surveillance vendors, or CSVs, overtook traditional state-sponsored espionage groups in attributed zero-day exploitation for the first time in Google’s tracking. Google says that marks a wider spread of advanced exploit access through private vendors and their customers.
State-backed activity still mattered. Google says China-linked espionage groups remained the most prolific state users of zero-days in 2025, with at least 10 attributed cases. The company says these actors kept focusing on edge and networking devices that are hard to monitor and useful for maintaining long-term access.
Financially motivated attackers also stayed active. Google attributed nine exploited zero-days in 2025 to likely or confirmed financially motivated groups, including campaigns that led to ransomware deployment.
Why 2026 could get worse
Google expects AI to speed up both vulnerability discovery and exploit development in 2026. The company says attackers will likely use AI to automate reconnaissance, find weaknesses faster, and shorten the path from bug discovery to live exploitation.
Microsoft has already documented how zero-days can turn into hands-on attacks that lead to privilege escalation and ransomware activity. In one 2025 case, Microsoft said attackers exploited a CLFS zero-day, CVE-2025-29824, before the flaw was fixed.
That combination of broader enterprise targeting, faster exploit development, and persistent abuse of high-value infrastructure explains why defenders should not treat 2025 as an outlier. The volume stayed high, and the attack surface kept expanding.
What security teams should do now
- Prioritize patches for internet-facing and edge systems first.
- Review CISA’s KEV catalog regularly and map it to your patch queue.
- Cut unnecessary privileges on security appliances, VPNs, routers, and hypervisors.
- Increase monitoring on systems that usually lack strong EDR visibility.
- Treat browser improvements as progress, not a reason to relax endpoint defenses.
- Assume AI will shrink attacker timelines and tighten response processes accordingly.
Quick takeaways
- Google tracked 90 exploited zero-days in 2025.
- Enterprise targeting hit a record share at 48%.
- Operating systems drew more attacks, while browser zero-days fell.
- Commercial spyware and surveillance vendors played a bigger role than before.
- Google expects AI to accelerate exploit development in 2026.
FAQ
Google defines a zero-day as a vulnerability that attackers exploited in the wild before a patch became publicly available.
Google Threat Intelligence Group says it tracked 90 zero-day vulnerabilities disclosed in 2025 that were exploited as zero-days.
The split was close, but enterprise exposure rose sharply. Google tracked 43 zero-days in enterprise software and appliances and 47 in end-user platforms and products.
Google says security and networking devices often provide privileged access and may lack strong endpoint visibility, which makes them high-value targets for initial access and persistence.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages