Hacked Prayer App Delivers Surrender Messages to Iranians Amid US-Israel Strikes
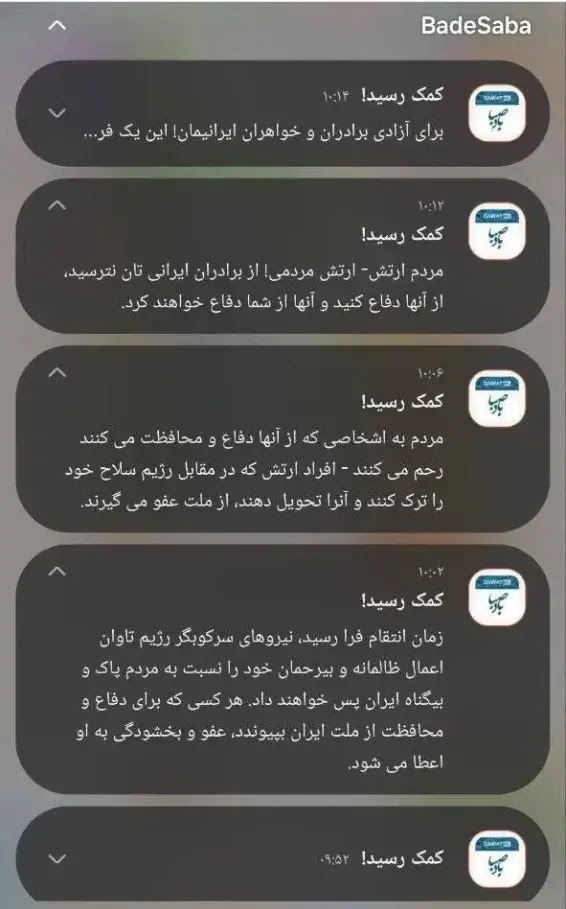
A popular Iranian prayer app called BadeSaba Calendar sent unauthorized push notifications to millions of users. These messages urged military personnel to surrender during joint US-Israel airstrikes on Tehran on March 1, 2026. The cyber operation mixed digital attacks with physical military action.
The app has over 5 million downloads on Google Play. It normally provides prayer times and religious reminders. Hackers took control of its notification system right after airstrikes began at 9:52 AM local time.
Users received alerts titled “Help is on the way.” The messages promised amnesty for those who abandoned posts. Later notifications warned of punishment for “repressive forces” and called for joining a “free Iran.”
Attack Timeline
- 9:52 AM: First wave of notifications hits users, saying “Help is on the way” with surrender calls.
- 10:02 AM: Alert claims “repressive forces will pay for their cruel actions.”
- 10:14 AM: Message pushes for “liberation” and laying down weapons.
Cybersecurity experts call this a nation-state operation. Attackers likely breached the app’s backend servers days earlier. They timed the payloads to match the strikes for maximum chaos.
Technical Details
| Aspect | Description |
|---|---|
| App Name | BadeSaba Calendar |
| Platform | Google Play Store (5M+ downloads) |
| Vector | Compromised push notification system |
| Scale | Millions of Iranian users affected |
| Method | Backend server breach, timed payloads |
| Attribution | Suspected Israeli intelligence or Iranian hacktivists; unconfirmed |
No malware details are public yet. Experts from Beyond Trust note the planning needed for such precision. This goes beyond typical cyberattacks.
Internet Blackout Impact
Iran faced a near-total internet shutdown during the strikes. Network traffic dropped to 4% of normal levels, per NetBlocks data. Major data centers lost global links, as reported by ArvanCloud.
State news sites like IRNA and ISNA went offline. This tactic blocks information flow during crises. It amplified the prayer app’s psychological effect.
Expert Statements
Morey Haber, Chief Security Advisor at BeyondTrust, said the attack shows advanced coordination. “This required pre-staged access to trigger at the exact moment of strikes.”
Narges Keshavarznia from Miaan Group added that attribution is unclear. It could be foreign states or local dissidents. No group has claimed responsibility.
FAQ
BadeSaba Calendar, a prayer timing app with millions of users in Iran.
At 9:52 AM local time on March 1, 2026, during US-Israel airstrikes.
They urged troops to surrender for amnesty and join a “free Iran.”
Unconfirmed; possibly Israeli intelligence or anti-government hacktivists.
Yes, traffic fell to 4% normal, with news sites offline.
Likely via backend servers, with notifications timed to airstrikes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages