Hackers abuse Google Cloud Storage to slip past email filters and deliver Remcos RAT

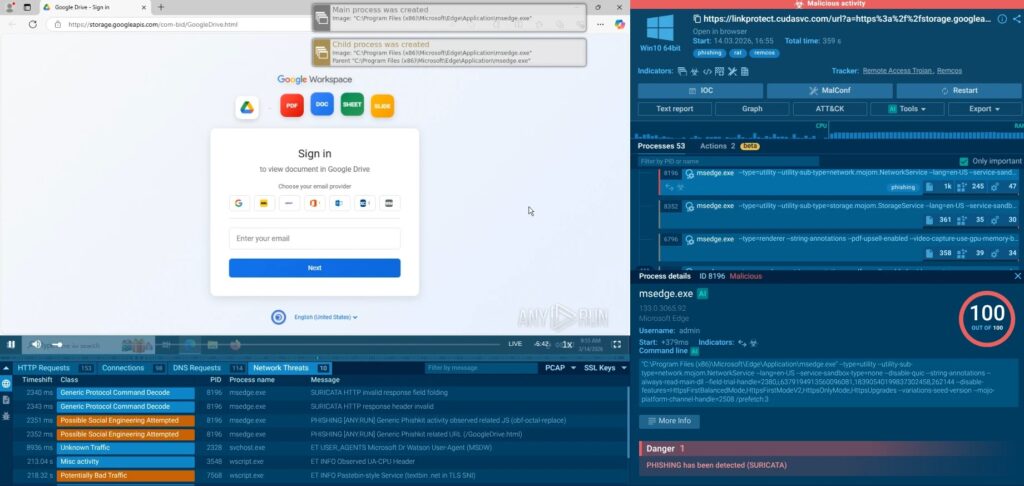
Threat actors are using Google Cloud Storage URLs to host fake Google Drive pages, steal login details, and then deliver Remcos RAT to Windows systems. Researchers at ANY.RUN said the campaign uses storage.googleapis.com pages to make phishing links look trustworthy enough to dodge some reputation-based checks in email and web security tools.
The trick works because the link points to real Google infrastructure, not to a freshly registered scam domain. Google’s own Cloud Storage documentation shows that the service stores and serves objects over Google-hosted infrastructure, which helps explain why attackers see value in abusing it for phishing delivery.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
ANY.RUN says the phishing pages imitate Google Drive document prompts and ask victims to sign in to view a file. After that fake login step, the victim gets pushed to download a malicious JavaScript file that starts the malware chain.
How the campaign gets past trust-based defenses
ANY.RUN identified the campaign in April 2026 and said the fake pages were hosted on storage.googleapis.com paths tied to names such as pa-bids, com-bid, contract-bid-0, in-bids, and out-bid. The pages copied Google branding and document icons to make the lure feel routine, especially for business users who open shared files every day.
Researchers said the pages did more than steal usernames and passwords. They also tried to capture one-time passcodes, which means a successful victim could hand over both account access and a foothold for a malware infection in the same flow.
That double outcome matters. ANY.RUN’s 2025 malware trends report says phishing stayed a major initial access and credential-harvesting method, with 541,225 phishing-related detections in its sandbox data, while stealers and RATs remained among the most common threat categories.
| Key detail | What researchers said |
|---|---|
| Hosting platform | Fake pages were hosted on Google Cloud Storage URLs |
| Lure theme | Google Drive document viewer and sign-in prompt |
| Data targeted | Email address, password, and one-time passcode |
| Initial file | Bid-Packet-INV-Document.js |
| Final payload | Remcos RAT |
What happens after the victim clicks
ANY.RUN says the infection starts when the victim runs a JavaScript file through Windows Script Host. That script uses time-delay evasion, then launches Visual Basic Script stages, drops files into %APPDATA%\WindowsUpdate, and sets startup persistence so the malware survives a reboot.
The chain then moves into PowerShell. Researchers said a script named DYHVQ.ps1 loads an obfuscated executable stored as ZIFDG.tmp, while another obfuscated .NET loader comes from Textbin and gets loaded directly into memory through Assembly.Load. That helps the attackers leave less for traditional file-based scanners to inspect on disk.
From there, the loader abuses RegSvcs.exe for process hollowing to run the Remcos payload inside a signed Microsoft binary. Microsoft documents RegSvcs.exe as the .NET Services Installation Tool, and MITRE describes Remcos as a closed-source remote control and surveillance tool that threat actors have repeatedly used in malware campaigns.
Reported attack chain
- Phishing email links to a Google Cloud Storage page
- Victim sees a fake Google Drive login screen
- Credentials and one-time passcode get captured
- JavaScript file downloads and runs
- VBS and PowerShell stages deploy the loader
RegSvcs.exegets abused for process hollowing- Remcos RAT establishes persistence and command-and-control access
Why Remcos RAT makes this more dangerous
ANY.RUN says the final payload gives attackers full and persistent control over the infected endpoint. Its Remcos overview says the malware is an actively maintained remote administration and surveillance tool, and MITRE notes that it has appeared in multiple real-world campaigns.
In this campaign, researchers said Remcos can log keystrokes, steal credentials, capture screenshots, transfer files, and maintain persistence through the Windows Registry under HKEY_CURRENT_USER\Software\Remcos-{ID}. That turns one phishing click into both immediate account theft and long-term device compromise.
This also raises the risk for business networks. ANY.RUN said the malware chain uses trusted hosting, heavy obfuscation, in-memory loading, and a signed Windows binary, which makes purely reputation-based or signature-based defenses less reliable.
What security teams should do
- Treat
storage.googleapis.comlinks with the same caution as any unexpected shared-file link - Block or review script downloads such as
.js,.vbs, and unusual PowerShell activity from user endpoints - Monitor for suspicious use of
wscript.exe,powershell.exe, andRegSvcs.exe - Hunt for persistence under
HKCU\Software\Remcos-* - Use behavioral analysis and sandboxing for suspicious files and URLs, not just reputation scores
Why this campaign matters now
This campaign shows how phishing keeps changing. Instead of forcing defenders to trust a fake site, attackers now borrow trust from familiar platforms and make the malicious step look like normal business activity.
That makes finance, procurement, legal, and executive users especially attractive targets because they often receive bids, contracts, invoices, and shared documents from outside the company. A fake Google Drive page tied to a bid document can look normal enough to earn a click. This is an inference based on the campaign lure style and the business-document theme described by researchers.
The larger lesson is simple. Trust in a known platform name does not make the content safe. Security teams need post-click visibility, because attackers increasingly hide the real danger after the user lands on a page that looks harmless at first glance.
FAQ
Attackers host phishing pages on Google Cloud Storage so the link points to trusted Google infrastructure instead of an obvious scam domain.
Researchers said the final payload is Remcos RAT, a remote control and surveillance tool widely used in malicious campaigns.
The phishing page sits on a legitimate Google-hosted domain, which can weaken simple reputation-based filtering. The malware chain also uses scripts, in-memory loading, and a signed Microsoft binary.
Watch for suspicious storage.googleapis.com lures, downloaded script files, unusual wscript.exe and PowerShell behavior, and suspicious use of RegSvcs.exe on endpoints.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages