Hackers are using Telegram to sell access to corporate VPN, RDP, and cloud accounts

Telegram has become a serious concern for enterprise defenders. Recent threat research shows that cybercriminals now use Telegram channels and bots to advertise stolen credentials, sell access to corporate environments, and support ransomware and stealer operations with much less friction than older dark web forums. CYFIRMA said in a February 2026 report that underground markets and Telegram-based initial access broker channels showed a sustained rise in listings tied to infostealer logs, including access to corporate VPNs, Microsoft 365 tenants, and domain-level credentials.
That does not mean every Telegram post offering “corporate access” is real. Many listings come from criminal channels, so some claims are exaggerated, recycled, or fraudulent. But the broader pattern is well established. Kaspersky said cybercriminal activity on Telegram surged by 53% in 2024, while Reuters, citing a UNODC report, said underground data markets have been moving to Telegram, where stolen data, malware, and illicit services are traded openly at scale.
For defenders, the real issue is speed. Telegram reduces the time between stolen credentials appearing online and an attacker using them. CYFIRMA says modern ransomware operations increasingly rely on credentials harvested by infostealers and then sold through underground markets and Telegram channels, sometimes leading to ransomware deployment in less than 48 hours after the credentials hit the market.
Why Telegram now matters in the access-broker economy
Traditional dark web forums still matter, but Telegram gives criminals a faster and more flexible operating layer. Telegram channels can broadcast access listings instantly, private groups can handle negotiation, and bots can automate delivery, payments, and validation. Kaspersky said Telegram’s bot framework makes it a low-effort ecosystem for illegal trade because a single bot can handle requests, payments, and delivery of stolen data or attack services with little human work.
That makes Telegram especially useful for initial access brokers, or IABs. Recorded Future says IABs specialize in obtaining and selling remote access methods that ransomware affiliates later use for lateral movement, malware deployment, or data theft. The most common access types it sees for sale include corporate VPNs, RDP services, Citrix gateways, web applications, and business email systems.
CYFIRMA’s February 2026 report adds cloud environments to that picture. It said Telegram-based IAB channels increasingly advertise access derived from infostealer logs, with listings that reference Microsoft 365, domain credentials, and corporate VPN entry points.
What attackers are reportedly selling
| Access type | Why attackers want it | Source support |
|---|---|---|
| Corporate VPN accounts | Gives a foothold that looks like normal remote access | Recorded Future says VPN access is among the most common IAB offerings. |
| RDP access | Useful for hands-on keyboard activity and later movement | Recorded Future lists RDP among common access methods; CISA also warns that exposed RDP raises risk. |
| Microsoft 365 / cloud accounts | Can expose email, files, identity systems, and admin controls | CYFIRMA says Telegram-based IAB listings increasingly reference Microsoft 365 tenants and domain credentials. |
| Okta / MFA-linked identities | Helps attackers hold access longer if they can register devices or abuse weak MFA flows | CISA says threat actors have modified MFA registrations after account compromise. |
| Stealer-derived browser sessions and cookies | Lets buyers bypass some login friction and move quickly | CYFIRMA says many listings explicitly reference infostealer logs, browser sessions, or cookie-based access. |
How this access gets into Telegram channels
The access usually starts before Telegram enters the picture. CYFIRMA says infostealers harvested an estimated 1.8 billion credentials in the first half of 2025, and it links those stolen credentials to a wider access-broker pipeline that feeds ransomware operations. Once the data is stolen, it can be sorted, priced, and pushed into underground markets, including Telegram channels.
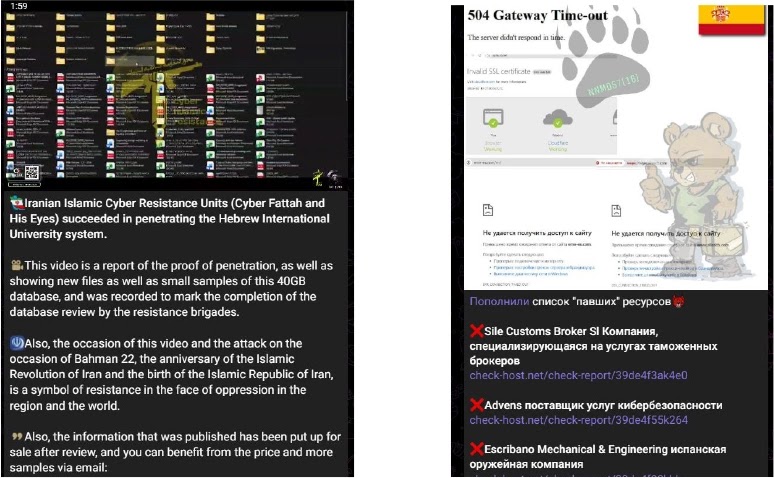
CISA has described similar real-world tradecraft in official advisories. In a joint advisory from October 2024, CISA and partners said Iranian actors used brute force, password spraying, and MFA fatigue to gain access to Microsoft 365, Azure, Okta-linked identities, and Citrix environments, then gathered credentials and network information that could be sold to other criminals. The agencies explicitly assessed that the information was likely sold on cybercriminal forums to enable additional malicious activity.
That is an important point. Even when Telegram is the storefront, the underlying compromise often comes from older, familiar methods:
- infostealer infections
- phishing and AiTM credential theft
- password spraying and credential stuffing
- MFA fatigue and weak enrollment controls
- exposed remote services such as RDP or Citrix
Why this is dangerous for businesses
Telegram speeds up the criminal supply chain. A stealer operator steals credentials, an IAB validates them, a buyer acquires access, and a ransomware affiliate moves in. That division of labor is one reason modern ransomware crews can move so fast once they get a foothold. CYFIRMA says this convergence has reduced attacker dwell time and increased the chance of rapid extortion chains.
The listings themselves also make targeting easier. Recorded Future says IAB offerings often tell buyers exactly what kind of environment they are getting, such as VPN, RDP, Citrix, or webmail access. CYFIRMA says access listings are increasingly categorized by organization size, geographic region, and privilege level. That gives ransomware affiliates a simple way to shop for the kinds of victims they want.
What defenders should do right now
| Priority action | Why it matters |
|---|---|
| Enforce phishing-resistant MFA for remote and cloud access | CISA says phishing-resistant MFA is the strongest widely available option and should protect remote access and high-risk accounts. |
| Stop exposing RDP directly to the internet where possible | CISA’s performance goals say public internet assets should expose no exploitable services such as RDP unless strong compensating controls are in place. |
| Monitor for impossible travel, one IP across many accounts, and suspicious MFA registration | CISA says those patterns can reveal stolen credentials and device registration abuse. |
| Audit dormant accounts, legacy auth, and cloud app permissions | CISA’s cloud baselines call for blocking legacy auth and tightening app registration and consent. |
| Track stealer exposure and Telegram-linked listings as part of threat intelligence | CYFIRMA says infostealer logs and Telegram-based IAB channels now form a direct bridge into ransomware operations. |
Practical warning signs
Security teams should pay attention when they see remote access activity that does not match normal employee behavior. CISA says defenders should look for impossible travel, suspicious IP changes, repeated failed logins across many accounts, and new MFA device registrations that do not line up with a user’s normal device history.
They should also treat stolen browser cookies and session tokens as a major risk, not just passwords. CYFIRMA says many modern access listings now reference browser sessions and cookie-based access directly, which can reduce the attacker’s need to log in the traditional way.
FAQ
Not completely, but it is taking a much bigger role. CYFIRMA, Kaspersky, and Reuters reporting tied to the UNODC all show that Telegram now supports a large share of cybercriminal activity, including stolen data sales, malware promotion, and access brokerage.
Yes, current research supports that. Recorded Future says IABs commonly sell VPN and RDP access, while CYFIRMA says Telegram-based IAB channels increasingly advertise corporate VPN access, Microsoft 365 tenants, and domain credentials.
Not usually. Telegram is often the distribution and coordination platform, not the original intrusion point. The initial compromise usually comes from phishing, infostealers, brute force, or abuse of weak MFA and exposed remote services.
Require phishing-resistant MFA, remove exposed RDP where possible, block legacy authentication, and watch for unusual sign-ins and unauthorized MFA registration. Those steps line up directly with CISA guidance.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages