Hackers target old TP-Link routers in Mirai malware campaign tied to CVE-2023-33538

Hackers are actively trying to compromise several older TP-Link routers through CVE-2023-33538, a command injection flaw that affects end-of-life models. The risk is real because CISA has already listed the bug in its Known Exploited Vulnerabilities catalog, and Palo Alto Networks Unit 42 says it has observed exploitation attempts in the wild.
The affected devices include TP-Link TL-WR940N v2 and v4, TL-WR740N v1 and v2, and TL-WR841N v8 and v10. These routers no longer receive regular vendor support, which leaves many owners without an official security fix.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Researchers say the attackers are trying to turn vulnerable routers into part of a Mirai-based botnet. In simple terms, that means a compromised home or small-office router could get pulled into a network of hijacked devices used for follow-on attacks such as distributed denial-of-service activity.
How the attacks work
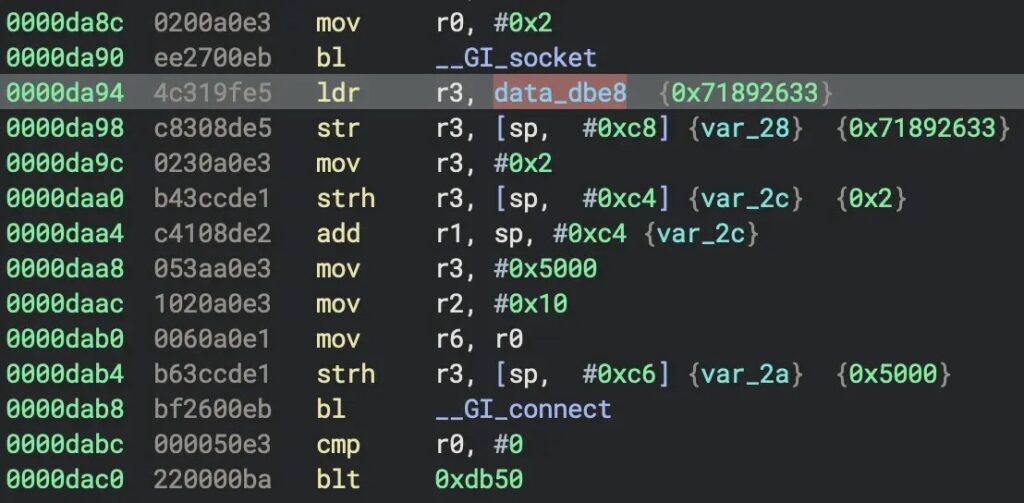
According to Unit 42, the flaw sits in the router’s web management interface at /userRpm/WlanNetworkRpm. The vulnerability allows command injection, which means a crafted request can make the device run commands it should reject.
The observed attack traffic attempted to fetch a malware file named arm7 from a remote server, mark it as executable, and run it on the router. Unit 42 linked that file to a Mirai-based Condi botnet variant that communicates with a command-and-control server after infection.
There is one important detail here. The exploitation attempts seen by researchers were active, but not fully correct. Unit 42 said the attackers used the ssid parameter instead of the vulnerable ssid1 parameter, and the payload also relied on wget, which is not present in the BusyBox environment on these devices. That means the exploit attempts they observed would fail as written, even though the underlying bug remains exploitable.
Why this still matters
This is not a case where defenders can relax because one attacker made mistakes. Unit 42 made clear that a more accurate exploit using the correct parameter could still succeed against exposed and vulnerable routers.
That warning carries extra weight because CISA added CVE-2023-33538 to the KEV catalog in June 2025, which means the agency treats it as exploited in the wild. When a flaw reaches KEV status, security teams usually treat it as a priority because attackers have already moved beyond theory.
The bigger problem is the hardware lifecycle. TP-Link’s end-of-life documentation shows these older products have aged out of support, and public vulnerability records note that impacted products should be discontinued. For users still running them, replacement is the safest path.
What researchers found inside the malware
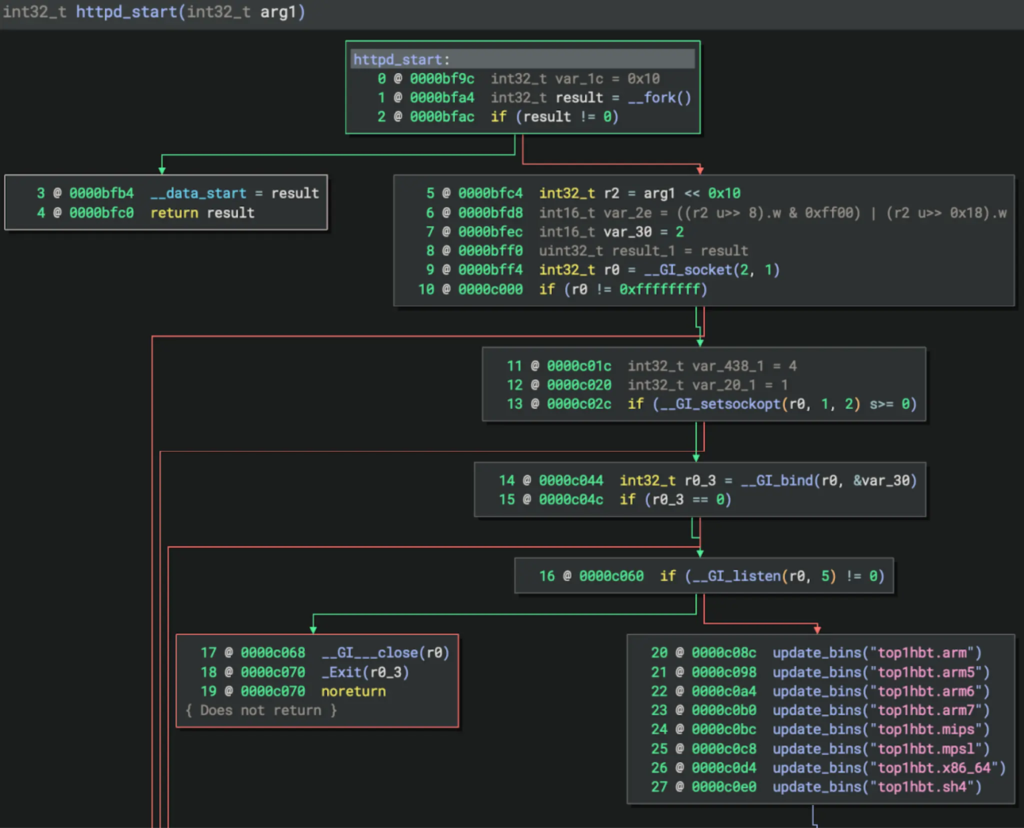
Unit 42 said the arm7 sample includes functions for heartbeats, self-updates, and internal HTTP server activity. The malware also tries to pull fresh copies of itself for multiple CPU architectures, which helps the campaign spread to more kinds of devices.
Researchers also said the binary can start an HTTP server on a random port between 1024 and 65535. Once that happens, an infected device can serve malware to other systems and help grow the botnet further.
The campaign appears to focus on old routers that attackers may expect owners to forget about. That pattern is common in IoT threats because unmaintained network gear often remains online for years, even after official support ends.
Key details at a glance
| Item | Details |
|---|---|
| Vulnerability | CVE-2023-33538 |
| Type | Command injection |
| Affected endpoint | /userRpm/WlanNetworkRpm |
| Affected models | TL-WR940N v2/v4, TL-WR740N v1/v2, TL-WR841N v8/v10 |
| Exploitation status | Active attempts observed |
| Malware | Mirai-based Condi variant |
| Patch status | No normal vendor patch path for these end-of-life models |
| Best response | Replace affected routers |
Sources for the table above:
What users and admins should do now
- Check the exact router model and hardware version, not just the product family name. Some versions are affected while others are not.
- Replace any affected end-of-life router instead of waiting for a future fix. TP-Link’s public end-of-life guidance makes clear that these products are no longer in normal support.
- Change default admin credentials immediately if the device is still online. Unit 42 said exploitation requires authenticated access to the web interface.
- Restrict remote management and monitor outbound traffic for suspicious connections tied to known malicious infrastructure.
FAQ
Yes. CISA added CVE-2023-33538 to the Known Exploited Vulnerabilities catalog, and Unit 42 reported seeing exploitation attempts in the wild.
Public records identify TL-WR940N v2 and v4, TL-WR740N v1 and v2, and TL-WR841N v8 and v10 as affected models.
For these end-of-life models, normal patch support is no longer the safe assumption. Replacement is the recommended option.
Unit 42 said exploitation requires authenticated access to the router’s web management interface, which makes default or weak admin credentials especially risky.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages