HungerRush breach used to mass-email extortion messages to restaurant customers

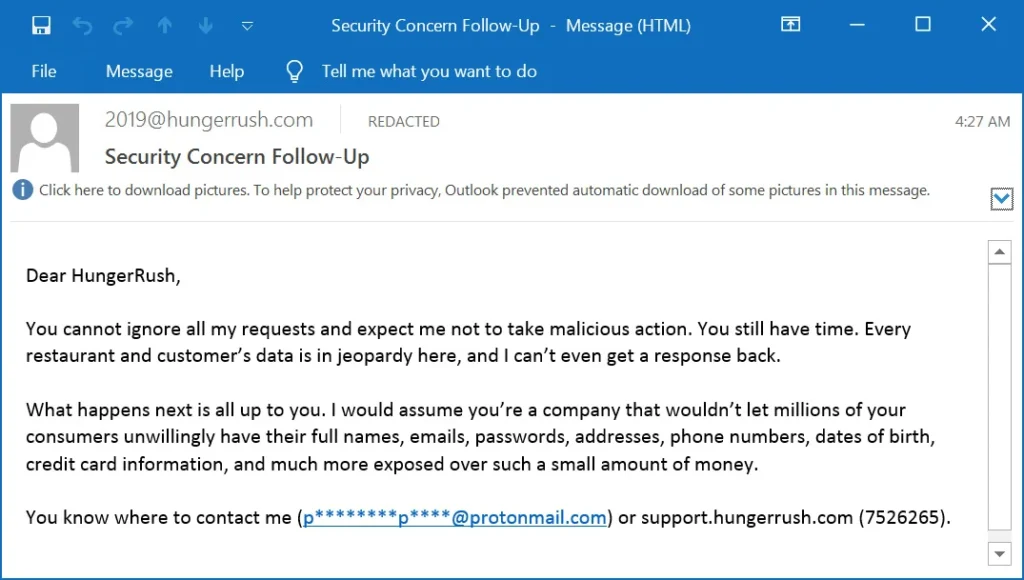
Customers of restaurants that use HungerRush started receiving extortion emails this week after attackers gained access to one of the company’s email-related systems. HungerRush later told BleepingComputer that the incident stemmed from a third-party vendor’s compromised credentials, which attackers used to breach the company’s email marketing service account.
That matters because the attacker did not just email HungerRush directly. The messages went out to restaurant patrons, which sharply increased pressure on the company and raised concern across restaurants that rely on HungerRush for point-of-sale, ordering, delivery, and payment workflows. HungerRush says it works with more than 16,000 restaurants, while its official site describes the company as a provider of POS, online ordering, and restaurant management tools.
According to BleepingComputer, the first messages appeared early Wednesday and warned that restaurant and customer data would be put at risk if HungerRush kept ignoring the attacker’s demands. A later email escalated the threat and claimed access to millions of customer records, including names, email addresses, passwords, mailing addresses, phone numbers, dates of birth, and credit card details. HungerRush disputes those broader claims.
The company said the exposed data was limited to certain customer contact information, specifically names, email addresses, mailing addresses, and phone numbers. HungerRush also said there is no evidence that passwords, dates of birth, Social Security numbers, or payment card data were exposed, and it added that credit card data is not stored in its systems.
What HungerRush says happened
| Item | Current status |
|---|---|
| Security incident | Confirmed by HungerRush via statement reported by BleepingComputer |
| Initial access route | HungerRush says attackers used a third-party vendor’s compromised credentials to access its email marketing service account |
| Data used in the email campaign | HungerRush says customer contact information, including names, email addresses, mailing addresses, and phone numbers, was accessed and used |
| Financial data exposed | HungerRush says no evidence shows exposure of payment card information and says it does not store credit card data |
| Other systems breached | HungerRush says it has no evidence that any other systems were compromised |
One important detail in the reporting concerns how the emails got delivered. BleepingComputer said email header analysis showed the messages were sent through Twilio SendGrid infrastructure and that the messages passed SPF, DKIM, and DMARC checks for the hungerrush.com domain. That would make the emails look more legitimate to recipients and mail systems because they came through an authorized channel rather than a simple spoof.
BleepingComputer also reported that the messages came from o10.e.hungerrush.com, which resolved to infrastructure operated by Twilio SendGrid. Customers told the publication that HungerRush had previously used the same service to send legitimate restaurant receipts, which likely made the messages feel even more credible.
Why this incident stands out
Most extortion attempts target the victim company directly. This one spilled into the customer base, which gave the attacker a much larger audience and created immediate reputational pressure. That tactic can work even without proving every claim in the email, because the public fear alone can drive support tickets, social posts, and calls from worried restaurant customers. The reporting reviewed shows exactly that pattern, with multiple recipients sharing the emails and online discussion spreading quickly.
It also shows how a breach in a marketing or communications system can still create serious downstream damage. Even if core payment systems remain untouched, access to a trusted outbound email platform gives attackers a way to reach customers directly under the company’s own brand.
What restaurants and customers should watch for now
- Treat any new HungerRush-themed email or text message with caution until the incident review ends.
- Be careful with follow-up phishing attempts that mention recent orders, restaurant receipts, refunds, or account issues.
- Do not click password reset links or attachments in unexpected messages that appear tied to this incident.
- Contact the restaurant directly through its official website or phone number if a message asks you to take urgent action.
- Monitor payment statements anyway, even though HungerRush says it does not store card data.
What HungerRush has done so far
HungerRush told BleepingComputer that it is aware of the incident, is actively investigating, and has involved the appropriate authorities. The company also said it disabled access to the affected email service as a precaution to prevent additional unauthorized messages while the investigation continues.
The company also pushed back on one early theory about the cause. After Hudson Rock CTO Alon Gal linked the event to infostealer logs from an alleged October 2025 employee compromise, HungerRush said that prior infostealer infection was not connected to this breach. Instead, it attributed the incident to a third-party vendor credential compromise tied to the email marketing account.
FAQ
Attackers sent extortion emails to restaurant patrons using HungerRush-linked email infrastructure after gaining access to the company’s email marketing service account, according to HungerRush’s statement to BleepingComputer.
HungerRush says there is no evidence that payment card data was exposed and says credit card data is not stored in its systems.
The company said certain customer contact information was accessed and used, including names, email addresses, mailing addresses, and phone numbers.
BleepingComputer reported that the emails were delivered through Twilio SendGrid and passed SPF, DKIM, and DMARC checks for the hungerrush.com domain.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages