JanaWare ransomware targets Turkish users through a customized Adwind RAT chain
A new ransomware operation called JanaWare is targeting users in Turkey through a tailored version of the Adwind remote access trojan. Acronis Threat Research Unit says the campaign uses a customized Java-based Adwind variant with polymorphic behavior to deliver the ransomware, and its analysis suggests the activity is likely focused on Turkish users.
The campaign does not look like a broad global spray-and-pray operation. Acronis says the malware checks both system locale and external IP geolocation before it continues, which likely limits execution to systems located in Turkey. That makes the targeting more deliberate than the sample article suggested.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This attack also appears to aim at smaller victims. The Record, citing the Acronis research, says the operators target Turkish home users and small businesses, and the ransom demands are relatively low, around $200 to $400, which points to a low-value, high-volume model rather than big-game enterprise extortion.
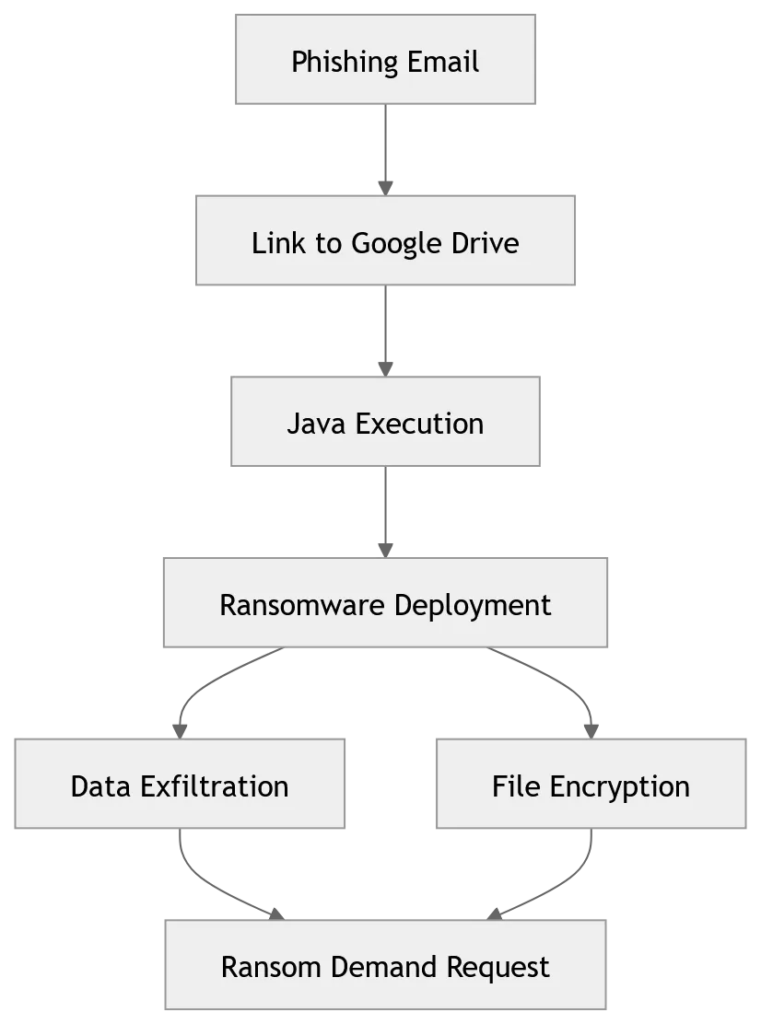
How the JanaWare attack chain works
Acronis says the infection starts with phishing emails that carry malicious Java archive files. Once opened, the chain moves to javaw.exe, which loads the customized Adwind RAT and later deploys the JanaWare ransomware component. The use of Java matters because Adwind has long been known as a cross-platform RAT, which gives attackers flexibility across different environments.
The customized Adwind strain does more than provide remote access. Acronis says it includes polymorphic characteristics and checks in with command-and-control infrastructure to receive configuration data and instructions on whether to deploy the ransomware. That means the RAT acts as both an access tool and a delivery platform for the final payload.
Acronis also says the infrastructure uses Tor for command-and-control, which helps hide the operators and makes network-based tracking harder. SOC Prime’s summary of the same research says the campaign relies on obfuscated Java JAR files, Tor-based C2, and a ransom note written in Turkish.
| Stage | What researchers reported | Why it matters |
|---|---|---|
| Initial lure | Phishing emails with malicious Java archives | Gives the attackers a simple first step |
| Loader execution | javaw.exe launches the tailored Adwind RAT | Helps the malware blend into expected Java activity |
| Victim filtering | Locale and IP checks limit execution to Turkey | Shows deliberate regional targeting |
| Post-compromise | RAT gathers system data and waits for instructions | Lets the attackers decide when to deploy encryption |
| Final impact | JanaWare encrypts files and drops a Turkish ransom note | Turns access into direct extortion |
What makes this campaign different
The strongest detail in the Acronis research is not just the ransomware itself. It is the way the attackers use Adwind as a selective delivery tool. Rather than encrypting every machine right away, the RAT can profile the system first and only deploy JanaWare when the victim meets the operator’s criteria.
This creates a more flexible attack chain. Acronis says the malware collects system information such as hostname, OS version, installed software, and user files and folders, then sends that inventory back to the attacker. Based on that profile, the operator can decide whether to move forward with ransomware.
Dark Reading notes that the overall campaign may have roots going back to 2020, which suggests the operators built a mature toolchain even though the ransom amounts are small. That combination matters because smaller ransomware campaigns often get less attention, but they can still use evasion, obfuscation, and modular delivery in ways that frustrate defenders.
Notable traits defenders should watch
- Malicious Java archive attachments in phishing emails
javaw.exespawning suspicious child processes or network activity- Locale and IP-based execution checks tied to Turkish systems
- Tor-based command-and-control traffic
- Ransom notes and instructions written in Turkish
What users and organizations in Turkey should do now
Email filtering and attachment controls should come first. Acronis says the campaign depends on phishing emails carrying malicious Java archives, so blocking or flagging risky archive types and unusual Java execution on endpoints can break the attack early.
Security teams should also watch remote-access behavior, not just ransomware activity. Since Adwind runs before JanaWare, defenders have a chance to stop the intrusion before files get encrypted. Endpoint tools that catch RAT behavior, suspicious command-and-control traffic, or sudden use of Java in unexpected business contexts can make a big difference.
Backups still matter, especially for the victims this campaign appears to prefer. The Record says the operation leans toward low ransom demands aimed at home users and small businesses. Those targets often have weaker security, fewer layered controls, and less mature recovery planning, which makes offline backups and tested restore paths especially important.
Practical response steps
- Block or heavily restrict suspicious Java archive attachments in email
- Investigate unusual
javaw.exeexecution on user systems - Monitor for outbound Tor-related or anonymized traffic patterns
- Hunt for Adwind-like remote-access behavior before encryption begins
- Maintain regular offline backups and test restoration procedures
- Train users to treat Turkish-language business lures and unexpected attachments with caution
FAQ
JanaWare is a ransomware strain that Acronis says is being delivered through a customized version of the Adwind Java RAT in attacks focused on Turkish users.
The campaign appears to focus on users in Turkey, especially home users and small businesses. The malware reportedly checks system locale and external IP location before it proceeds.
The Record says the demands are relatively small, around $200 to $400, which suggests a lower-value but broader-volume approach.
Adwind gives the attackers remote access and a flexible staging layer before the ransomware runs. Acronis says the tailored variant gathers system information, receives instructions from command-and-control infrastructure, and then helps deliver JanaWare.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages