JokerOTP seller arrested — what this means for enterprise risk and MFA security
Dutch police have arrested a 21-year-old man from Dordrecht in connection with the JokerOTP phishing-as-a-service (PhaaS) operation. Law enforcement says this individual sold access to an automated tool that intercepts one-time passcodes and other sensitive data, enabling large-scale account takeover and payment fraud. This arrest is the latest move in a multi-year, multi-country investigation that already led to earlier arrests and a takedown of JokerOTP infrastructure in 2025.
Dutch police have arrested a 21-year-old man from Dordrecht in connection with the JokerOTP phishing-as-a-service (PhaaS) operation. Law enforcement says this individual sold access to an automated tool that intercepts one-time passcodes and other sensitive data, enabling large-scale account takeover and payment fraud. This arrest is the latest move in a multi-year, multi-country investigation that already led to earlier arrests and a takedown of JokerOTP infrastructure in 2025.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Quick summary — what happened
- Dutch police arrested a 21-year-old man from Dordrecht on suspicion of selling the JokerOTP bot. This is described as the third arrest linked to the PhaaS operation.
- JokerOTP was the subject of a coordinated takedown in April 2025. That operation involved UK and Dutch authorities and resulted in earlier arrests.
- Law enforcement estimates JokerOTP powered tens of thousands of attacks and caused millions in losses. Cleveland Police reported JokerOTP-linked activity as part of that April 2025 action.
“Victims were automatically called by the bot and informed that criminals were attempting to gain access to their account. The bot then asked them to enter the one-time password. Victims, therefore believe they are protecting themselves by cooperating and providing information.” Anouk Bonekamp, Team leader, Cybercrime Oost-Brabant.
“Authorities in the United Kingdom and the Netherlands dismantled JokerOTP, a phishing-as-a-service platform, following a three-year investigation.” Bitdefender summary of the joint investigation and takedown.
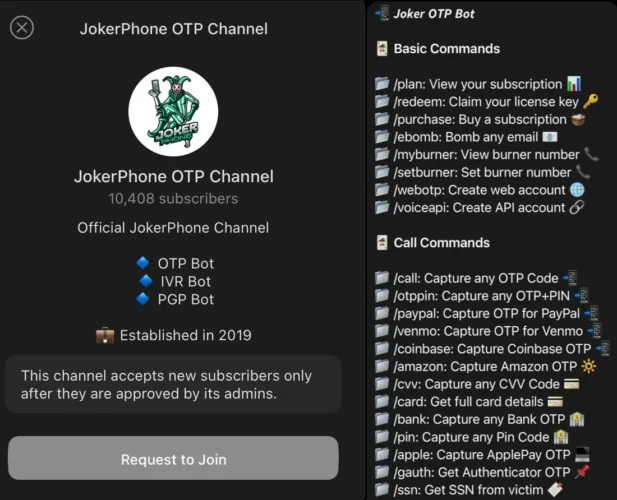
How JokerOTP works : technical outline
- Delivery: Attackers buy or rent JokerOTP access via Telegram or other criminal channels.
- Call automation: JokerOTP automates phone calls that coincide with OTP delivery, impersonating a bank or service.
- User deception: The call urges the recipient to read out the one-time code. Because the call is synchronous with an authentication attempt, victims often comply.
- Exfiltration and reuse: Captured codes, credentials, and sometimes card data are collected and used immediately to complete logins or fraud.
- Scaling: As a PhaaS, JokerOTP enabled many customers to run high volumes of attacks with minimal technical skill.
Enterprise risk analysis: what this means for organizations
- MFA that relies on OTPs sent to SMS or voice is brittle
JokerOTP demonstrates that OTPs delivered by SMS or voice can be socially engineered away. Organizations that treat SMS OTP as a strong second factor should re-evaluate that assumption. - Credential stuffing plus OTP interception creates high success rate
Attacks frequently combine leaked/stolen credentials with JokerOTP to bypass MFA in real time, converting passive breaches into full account takeovers. - Fraud escalation and supply-chain impact
Compromised accounts may enable payment fraud, invoice manipulation, payroll fraud, and access to third-party SaaS. The downstream financial and reputational impact can be substantial. - Insider and reseller risk
PhaaS models mean a single exposed tool can be rented by many criminals. Even after takedown, service clones or forks can re-emerge quickly. - Regulatory and customer trust exposure
Repeated account takeover incidents attract regulatory scrutiny and can damage customer trust at scale.
Recommended mitigations (operational and technical)
Short term (hours to days)
- Block SMS/voice MFA for high-risk operations where possible. Move HR, finance, and admin reauthentication to stronger methods.
- Force reauthentication and rotate credentials for high-value accounts suspected of exposure.
- Require phishing reporting and quick remediation workflows for users who report suspicious calls.
Medium term (days to weeks)
- Migrate to phishing-resistant MFA for staff with access to sensitive systems. Options include security keys (FIDO2/WebAuthn) and certificate-based authentication.
- Enforce conditional access policies based on device posture, geolocation and risk signals.
- Add voice-spam / robocall detection and blocking at telephony provider level for corporate phone numbers.
Long term (weeks to months)
- Implement continuous monitoring for anomalous logins, lateral movement and unusual transaction patterns.
- Integrate signals from fraud teams, telephony providers, and identity providers into a central detection platform.
- Conduct tabletop exercises simulating OTP interception and account takeover to test detection and response playbooks
Quick technical checklist for SOC & fraud teams
- Enforce FIDO2/WebAuthn for privileged roles.
- Disable SMS and voice OTP for admin and financial functions.
- Review MFA exemptions and emergency access procedures.
- Monitor for concurrent authentication attempts and rapid session creation.
- Add checks for new device enrollments originating from atypical geographies.
- Use out-of-band verification via a vetted channel (not the one used in the request) for high-value transactions.
Indicators & detection tactics
| Indicator | Detection tactic |
|---|---|
| Multiple OTP requests within short window | Alert on repeated MFA requests from same account/IP |
| Rapid reuse of OTPs | Correlate OTP challenge/response with login timestamps |
| Outgoing calls to fraud-related numbers | Monitor corporate telephony and block suspicious destinations |
| Credential reuse across services | Feed breached-credential lists into risk scoring |
| Abnormal device or browser fingerprint after MFA | Trigger step-up authentication or lockdown |
FAQ
Authorities reported JokerOTP was used in more than 28,000 attacks during the period studied in 2023–2025.
Some reports estimate losses of several million dollars. For example, reporting around the takedown cited impacts in the low millions to tens of millions across victims and jurisdictions.
Voice OTPs remain convenient but are vulnerable to social engineering. Phishing-resistant MFA such as hardware security keys is strongly preferred for high value targets.
Change passwords, enable phishing-resistant MFA if available, check Have I Been Pwned, and report the incident to the organization and police. The public resource Have I Been Pwned can help check whether an email or password was exposed.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages