LexisNexis breach claim raises fresh questions, but key details remain unverified
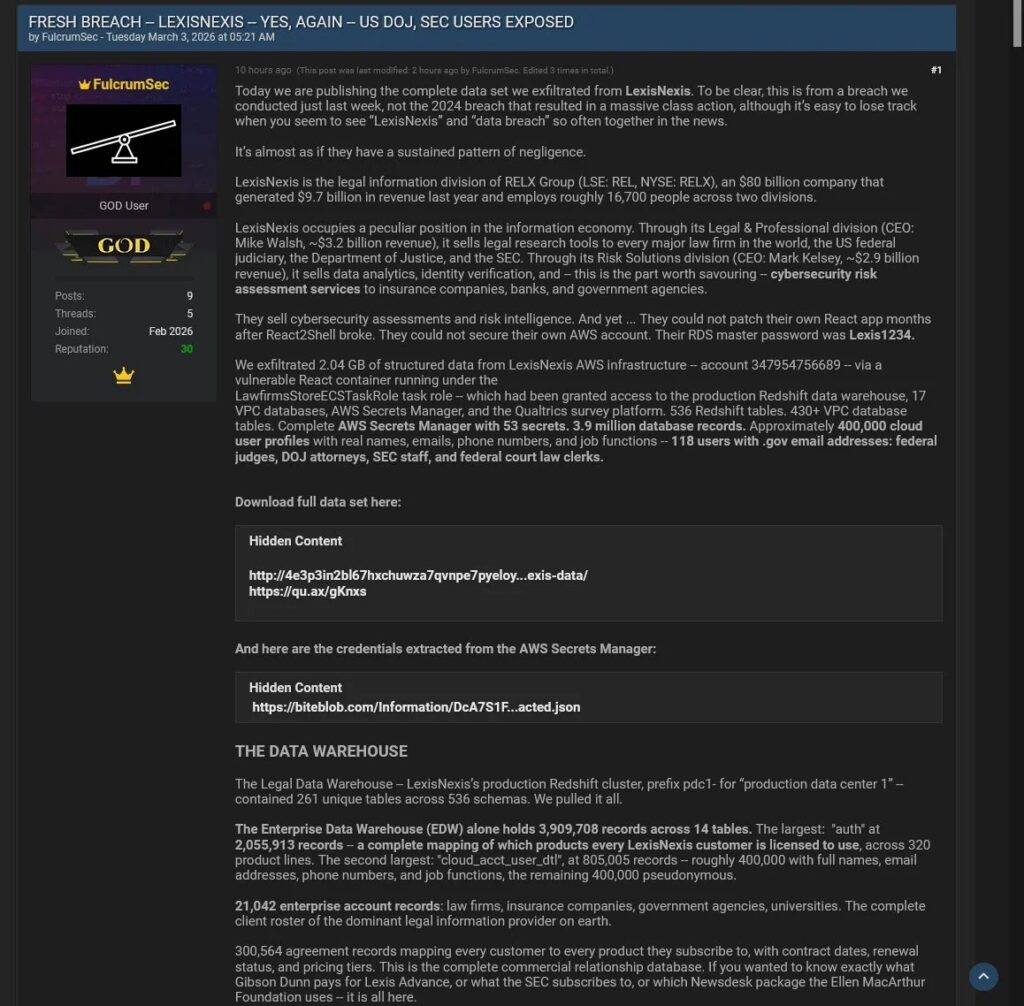
A threat actor calling itself FulcrumSec has claimed it stole 2.04 GB of data from LexisNexis Legal & Professional, allegedly after exploiting React2Shell, a critical React Server Components flaw disclosed in late 2025. As of March 4, I could not find any public breach notice from RELX or LexisNexis Legal & Professional confirming this new incident, so the most accurate framing right now is that this is an unverified breach claim, not a confirmed disclosure.
That distinction matters. The sample you shared states the actor “gained access” and “exfiltrated” data as fact. Publicly available evidence does not support saying that with confidence yet. What is confirmed is that React2Shell, tracked as CVE-2025-55182, is a real critical vulnerability that AWS said China-nexus threat groups began exploiting rapidly after disclosure in December 2025.
It is also true that LexisNexis has recent breach history. In May 2025, LexisNexis Risk Solutions disclosed a separate breach affecting more than 364,000 people, tied to a compromised GitHub account and a third-party development platform. That older incident did not involve LexisNexis’s own networks or systems, according to the company’s statement reported by TechCrunch.
So the strongest version of this story is not “LexisNexis breached again.” It is this: a threat actor has made a serious and detailed claim about a new LexisNexis Legal & Professional breach, but there is no public company confirmation yet, and several technical assertions remain unverified.
What is confirmed, and what is still only alleged
| Claim | Status | What the evidence shows |
|---|---|---|
| FulcrumSec claims 2.04 GB was stolen from LexisNexis Legal & Professional | Alleged | I found references to the claim, but no public company breach notice or SEC-style filing confirming it yet. |
| React2Shell is a real critical flaw | Confirmed | AWS says CVE-2025-55182 is a critical unsafe deserialization issue in React Server Components and that threat groups moved quickly to exploit it. |
| React2Shell can lead to remote code execution | Confirmed | AWS described it as unauthenticated remote code execution affecting React and Next.js environments using React Server Components. |
| LexisNexis had a separate breach disclosed in 2025 | Confirmed | LexisNexis Risk Solutions disclosed a breach tied to GitHub data exposure affecting more than 364,000 people. |
| This new alleged incident exposed federal judges, DOJ lawyers, and SEC staff | Unverified | I found no official confirmation or independent public evidence validating those specific victim categories. |
| Weak AWS secret management and a password like “Lexis1234” were involved | Unverified | These details appear to come from the threat actor’s claims, not from an official or independently verified source. |
Why the React2Shell angle is plausible
If the claim is real, the React2Shell part is not the weakest link in the story. AWS published a detailed security blog in December 2025 saying the flaw affected React 19.x and Next.js 15.x and 16.x with App Router, and warned that exploitation could happen even if an organization did not explicitly expose server functions. AWS also said it observed rapid exploitation by China-nexus threat groups and urged immediate patching.
That means a company running an exposed and unpatched React or Next.js deployment could, in principle, face serious risk. It does not prove FulcrumSec breached LexisNexis. It only means the alleged entry point is technically credible.
What makes this claim harder to verify
There are at least three reasons to stay cautious.
First, there is no public breach confirmation from RELX or LexisNexis Legal & Professional that I could find. The official LexisNexis and RELX pages I found include legal terms, privacy notices, and general security language, but nothing confirming a March 2026 breach affecting the Legal & Professional division.
Second, the breach details are unusually specific. The claim names an ECS task role, Redshift access, VPC databases, Secrets Manager exposure, and even a supposed master password. Highly detailed claims can be real, but they can also be crafted to look more credible. Without supporting screenshots, forensic confirmation, or a company statement, those details should remain labeled as allegations.
Third, the earlier confirmed LexisNexis breach in 2025 already makes the brand a natural target for copycat extortion or reputational pressure. Threat actors often attach fresh narratives to companies that have recently disclosed one incident because the public is more likely to believe a second one. That pattern does not disprove the claim, but it does make independent validation even more important.
What security teams should watch for
| Priority | Why it matters |
|---|---|
| Patch React and Next.js immediately if exposed | AWS says React2Shell has been actively exploited since disclosure. |
| Review cloud roles with broad Secrets Manager or warehouse access | Even if this claim is false, overprivileged task roles remain a common cloud risk. AWS continues to tighten security defaults in services like Redshift for exactly this reason. |
| Audit publicly exposed React Server Components deployments | AWS says vulnerable applications can be exposed even when teams do not realize RSC paths are reachable. |
| Separate “breach claims” from “confirmed incidents” in communications | Public accuracy matters, especially when alleged victims include government users or regulated data sets. |
What this means for LexisNexis right now
If LexisNexis confirms the incident, this would become a major story because the alleged exposure touches legal data, enterprise accounts, and potentially government-linked users. If the company denies it, the focus will shift to whether the actor fabricated the claim, exaggerated a limited intrusion, or misrepresented older or test data.
Right now, the responsible conclusion is narrower. A threat actor has made a technically plausible claim involving a real critical vulnerability, but the breach itself remains unconfirmed in public official sources.
FAQ
I could not find a public company statement or notice confirming this new alleged incident involving LexisNexis Legal & Professional. The story is still best described as an unverified threat actor claim.
Yes. AWS says React2Shell, or CVE-2025-55182, is a critical unsafe deserialization flaw in React Server Components that can allow unauthenticated remote code execution in affected setups.
Yes, but it was a different incident. In 2025, LexisNexis Risk Solutions disclosed a breach tied to GitHub data exposure affecting more than 364,000 individuals.
Not from the public sources I found. Those details appear to come from the threat actor’s own claims rather than an official disclosure or independently verified forensic report.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages