METATRON brings local AI-assisted pentesting to Linux with offline LLM analysis
A new open-source security tool called METATRON is drawing attention because it runs AI-assisted penetration testing workflows entirely on the local machine. According to the project’s GitHub page, the tool is a command-line assistant for Linux that combines standard recon utilities with a locally hosted language model, so users do not need cloud access, API keys, or paid subscriptions.
The main appeal is privacy. METATRON says scan data stays on the tester’s device because it uses Ollama as the local model runner and feeds tool output into a custom metatron-qwen model configuration. That makes it easier to use in environments where sending internal host data to external AI services is not acceptable.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
In simple terms, METATRON is a Linux pentesting assistant that automates recon, passes the results into a local model, and then generates vulnerability analysis, exploit suggestions, and remediation advice. The project currently targets Parrot OS and other Debian-based systems, based on its published setup steps and package requirements.
How METATRON works
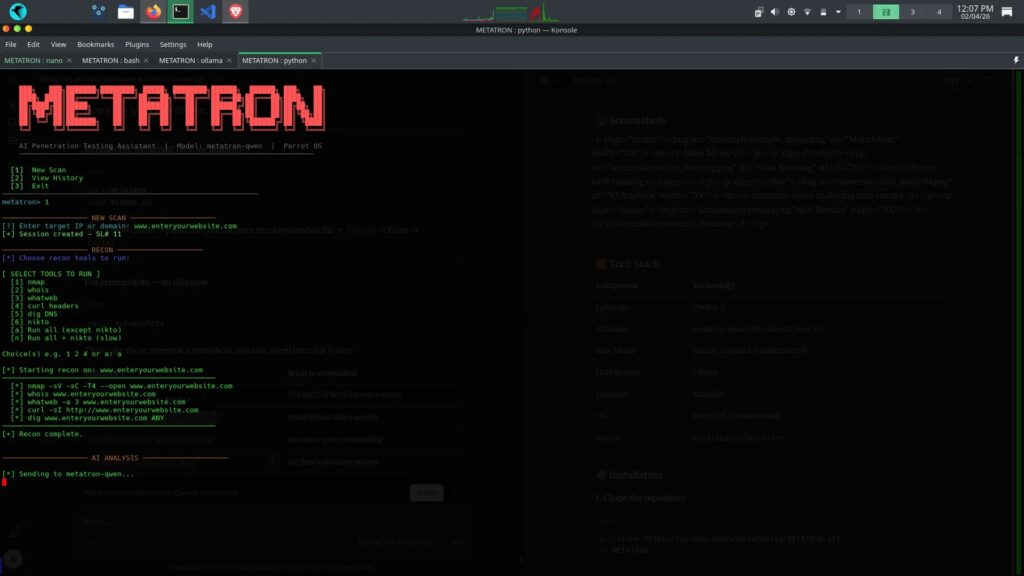
The GitHub README says users provide a target IP address or domain, and the tool then runs familiar utilities including nmap, whois, whatweb, curl, dig, and nikto. It collects the output from those tools and hands the results to the local LLM for interpretation.
The project also includes an agentic loop. According to the README, the AI can ask for more tool runs in the middle of analysis if it decides it needs more information before producing a result. That gives METATRON a more iterative workflow than a basic one-pass scanner.
METATRON further adds DuckDuckGo-based web search and CVE lookup without an API key. That means the tool can supplement local scan findings with public vulnerability context while still keeping the core workflow centered on the local machine.
The local model and system design
The repository describes the AI layer as metatron-qwen, a fine-tuned Qwen 3.5-based model served through Ollama. The published Modelfile points to huihui_ai/qwen3.5-abliterated:9b as the base model and sets a 16,384-token context window with temperature 0.7, top_k 10, and top_p 0.9.
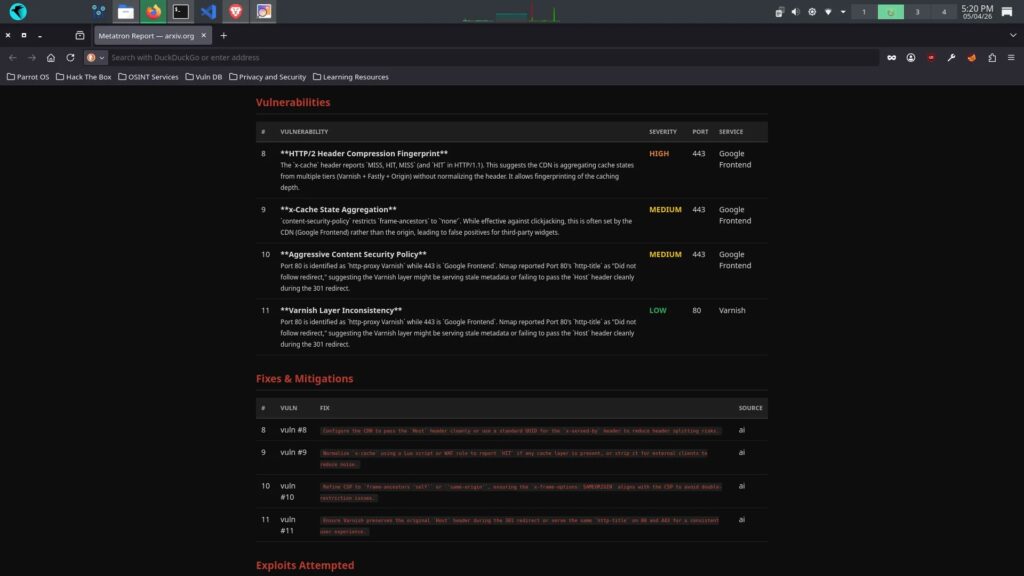
On the storage side, METATRON uses MariaDB. The README says scan history, vulnerabilities, fixes, exploit attempts, and summaries are stored across five linked tables, all tied back to a central session number.
That design makes the project more than a simple wrapper around existing tools. It is trying to build an audit trail that testers can revisit, edit, delete, or export later as HTML or PDF reports directly from the CLI.
METATRON at a glance
| Item | Details |
|---|---|
| Project name | METATRON |
| License | MIT |
| Platform focus | Parrot OS and other Debian-based Linux systems |
| Interface | CLI |
| Core recon tools | nmap, whois, whatweb, curl, dig, nikto |
| Model runner | Ollama |
| Base model in Modelfile | huihui_ai/qwen3.5-abliterated:9b |
| Database | MariaDB |
| Report export | PDF and HTML |
Why security teams may care
For defenders, consultants, and internal red teams, the strongest selling point is data handling. Many organizations do not want target banners, internal IP ranges, or scan outputs sent to external AI platforms. METATRON’s local-first design tries to solve that by keeping inference on-device.
The hardware cost is not trivial, though. The project says the 9B model requires at least 8.4 GB of RAM, while systems with less memory should switch to the 4B variant by editing the Modelfile. That means local privacy comes with real compute requirements.
It is also important to keep expectations realistic. METATRON looks useful as a recon and analysis assistant, but its own repository frames it as a tool for authorized testing and educational use. It should be treated as a helper for security workflows, not as a replacement for human validation.
Strengths and limitations
- Runs locally with no cloud dependency.
- Uses familiar reconnaissance tools instead of inventing a closed workflow.
- Stores results in MariaDB with session-based history.
- Supports PDF and HTML report export.
- Requires local Linux setup, model downloads, and enough RAM for the selected model.
- Carries the usual dual-use concerns that come with penetration testing software, so authorization matters.
FAQ
METATRON is an open-source CLI penetration testing assistant for Linux that combines standard recon tools with a local LLM for offline analysis.
No. The project says it runs entirely on the local machine with Ollama and does not require cloud access, API keys, or subscriptions.
The repository describes it as built for Parrot OS and other Debian-based Linux distributions.
The published feature list includes nmap, whois, whatweb, curl, dig, and nikto, along with DuckDuckGo-based search and CVE lookup.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages