Microsoft device-code phishing and fake Claude Code ads show how attackers now abuse trusted sign-in and install flows
Attackers are using two fast-growing tactics to compromise business and developer accounts. One campaign abuses Microsoft’s legitimate device code sign-in flow to steal OAuth tokens without stealing passwords, while another uses fake Claude Code install pages and malicious search ads to infect macOS users with AMOS stealer. Microsoft and multiple security researchers have published warnings that match the core threat pattern described in your sample.
The Microsoft-related campaign matters because it can bypass the protection many users trust most: MFA. In a device code phishing attack, the victim signs in on a real Microsoft page, but the session they approve belongs to the attacker, who then receives access and refresh tokens. Microsoft says this technique has become a serious identity threat and specifically classifies device code flow as high risk in Conditional Access guidance.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
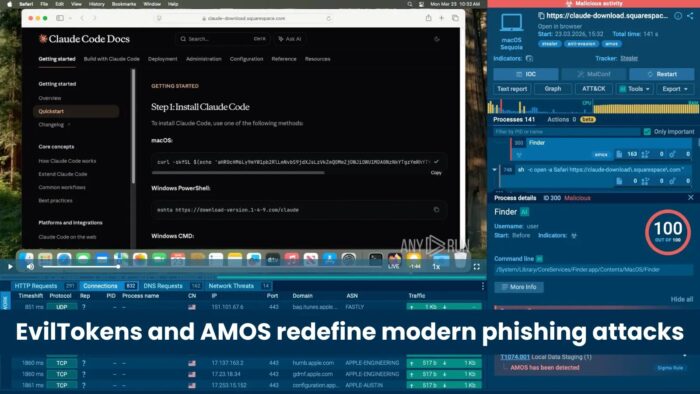
The second campaign targets developers and AI tool users. Researchers found fake Claude Code documentation pages promoted through malicious Google ads. Those pages instruct users to paste terminal commands that fetch malware, including AMOS on macOS. Independent reporting from ANY.RUN and Bitdefender shows the fake pages closely mimicked the real install experience, which made the lure more convincing.
How the Microsoft device-code attack works
Instead of building a fake Microsoft login page, attackers start a real device code flow and trick the victim into entering a code at Microsoft’s real device login page. Once the victim signs in and completes MFA, Microsoft issues tokens to the attacker’s session, not the victim’s device. Microsoft’s April 2026 threat report describes this exact flow and says the method is being scaled with AI and automation.
This tactic stands out because it removes the need to capture a password directly. That makes many classic phishing clues less obvious. Microsoft says the victim may interact with what looks like a document preview or another benign prompt, then get redirected to the legitimate device login experience where the malicious code gets approved.
Security researchers also say threat actors can use the stolen tokens for longer-term access. Microsoft’s 2025 and 2026 guidance explains that device code phishing can lead to token capture, data theft, persistent access, and movement across connected services if defenses do not limit the flow.
How the fake Claude Code malware chain works
The Claude Code-themed campaign uses a different entry point. Researchers say attackers bought or abused Google ad placements so users searching for Claude Code or related AI tools landed on a fake documentation page instead of the real one. That page then delivered a ClickFix-style prompt telling the user to paste a command into Terminal.
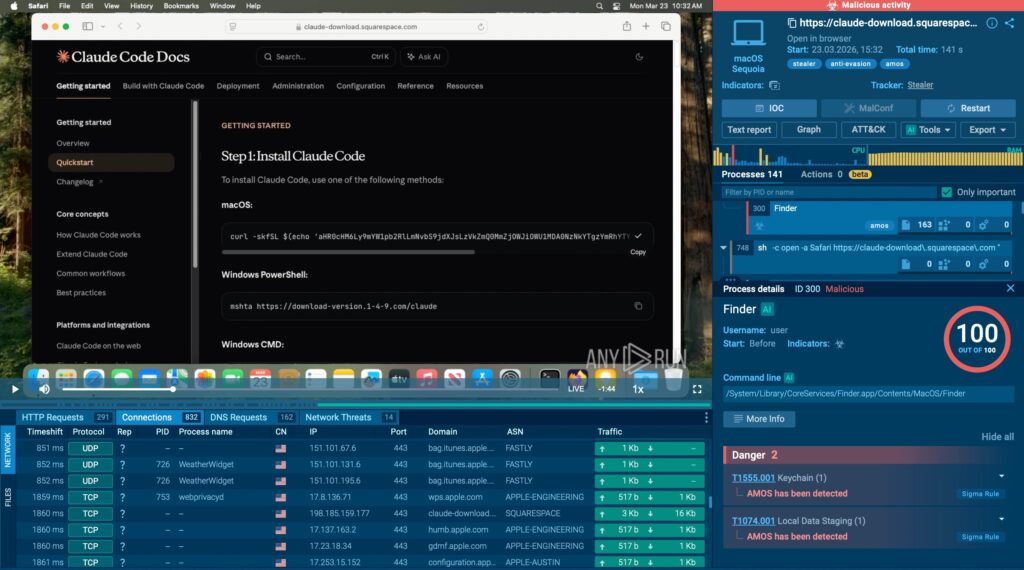
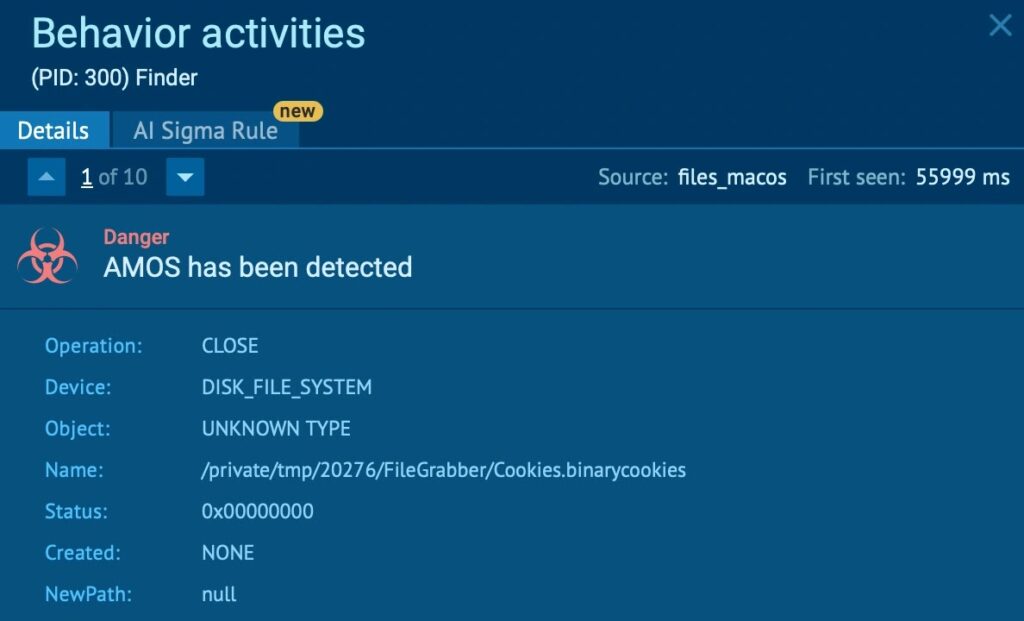
On macOS, that command can download and run AMOS, also known as Atomic macOS Stealer. Researchers say the payload can steal browser data, saved credentials, cookies, Keychain-related secrets, and other sensitive files. ANY.RUN and other reports also describe persistence involving a ~/.mainhelper component, which aligns with the sample you shared.
This threat goes beyond ordinary consumer malware. Developers often hold access to source code, cloud consoles, SSH keys, API tokens, and internal documentation. That turns one successful compromise into a possible path toward larger business breaches. The uploaded sample captured that risk accurately, but the stronger evidence comes from the public research and Microsoft’s own identity threat guidance.
Side-by-side view of both campaigns
| Campaign | Main lure | What the victim sees | What gets stolen or abused | Why it is dangerous |
|---|---|---|---|---|
| EvilTokens style device-code phishing | Phishing message with verification code | Real Microsoft device login page | OAuth access and refresh tokens | Can bypass normal password theft detection and still survive MFA |
| Fake Claude Code ClickFix chain | Malicious Google ad or fake docs page | Fake install instructions and terminal paste prompt | Credentials, cookies, files, Keychain-related data, possible backdoor access | Hits high-value developer endpoints and blends into real install behavior |
What defenders should watch for
- Device code authentication attempts from unusual locations, unmanaged devices, or unexpected users. Microsoft recommends controlling this flow through Conditional Access because it carries phishing risk.
- Sign-in events where the user insists they used a real Microsoft page, but the session still looks compromised. That pattern fits token theft through device code abuse.
- Sponsored search results or cloned documentation pages for Claude Code and similar AI tools. Multiple researchers found fake pages that copied real product docs closely.
- Terminal commands pasted from browser pages into macOS systems, especially on developer machines. That is the core user action in the ClickFix chain.
- Persistence clues such as
.mainhelperor unusual LaunchDaemon behavior on affected Macs. Researchers tied these artifacts to AMOS-related infections and follow-on access.
How organizations can reduce risk now
Microsoft says organizations should treat device code flow as a high-risk authentication method and apply Conditional Access controls where possible. Security teams should also review sign-in logs for unexpected device code activity and consider stronger phishing-resistant authentication methods, including passkeys.
For the fake install page threat, teams should train users never to paste terminal commands from ads or unverified documentation pages. Endpoint controls should flag unsigned script execution, suspicious download-and-execute chains, and outbound connections from developer endpoints after shell activity. The research on the Claude Code lure also shows value in ad-blocking, DNS filtering, and browser isolation for risky searches.
The larger lesson is simple. Attackers no longer need obviously fake pages to win. They now abuse trusted brands, real authentication pages, and normal setup flows to make the malicious step look routine. That shift makes these campaigns harder to spot and more dangerous for enterprises.
Quick response checklist
- Audit Microsoft Entra sign-in logs for unexpected device code flow events.
- Restrict or block device code flow where business need is low.
- Push phishing-resistant authentication methods for high-risk users.
- Warn developers not to trust sponsored install links for AI tools.
- Hunt for AMOS-related artifacts and unusual shell-driven downloads on macOS.
FAQ
It is a phishing method where the victim enters a valid code on a real Microsoft login page, but the resulting tokens go to the attacker’s session. Microsoft says this method can bypass the normal benefits of MFA if the victim approves the login.
Not reliably. In this attack, the victim completes MFA during the malicious approval flow, so the attacker still receives valid tokens.
Researchers say victims clicked malicious ads, landed on fake documentation pages, and pasted terminal commands that downloaded and ran AMOS or related malware.
Developers often have elevated access to code, cloud systems, credentials, and internal tools. One infected machine can give attackers a much bigger foothold.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages