Microsoft-signed file used to deliver LOTUSLITE in espionage campaign targeting Indian banks

A newly documented espionage campaign has targeted India’s banking sector with an updated LOTUSLITE backdoor, and the attackers used a legitimate Microsoft-signed executable to help the malware slip past trust-based defenses. Acronis Threat Research Unit said the malware arrived through DLL sideloading, a technique that abuses a signed program to load a malicious library placed beside it.
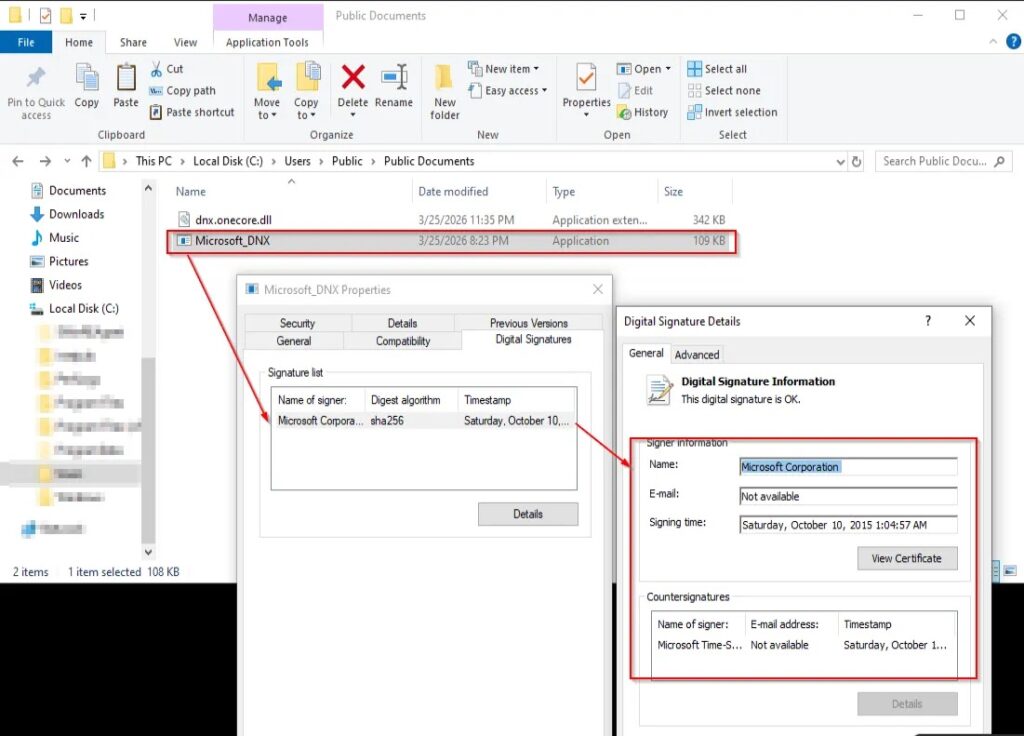
The signed file at the center of the activity is Microsoft_DNX.exe, an older Microsoft developer component. Researchers said the attackers bundled it with a malicious DLL so Windows would load the rogue code as if it belonged to the trusted application. That choice matters because many security tools treat Microsoft-signed binaries as low risk unless another behavior stands out.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Acronis linked the operation to the Mustang Panda activity cluster with moderate confidence. The researchers based that assessment on shared infrastructure and operating patterns, while noting that the campaign also overlapped with activity tied to Korea-focused geopolitical lures.
How the infection chain works
The attack starts with a lure archive themed around India’s financial sector. Inside, victims find the legitimate Microsoft_DNX.exe file and a malicious DLL crafted to load when the executable runs. Because the binary looks for the DLL by name rather than by a verified full path, the attacker only needs to place the fake library in the same folder.
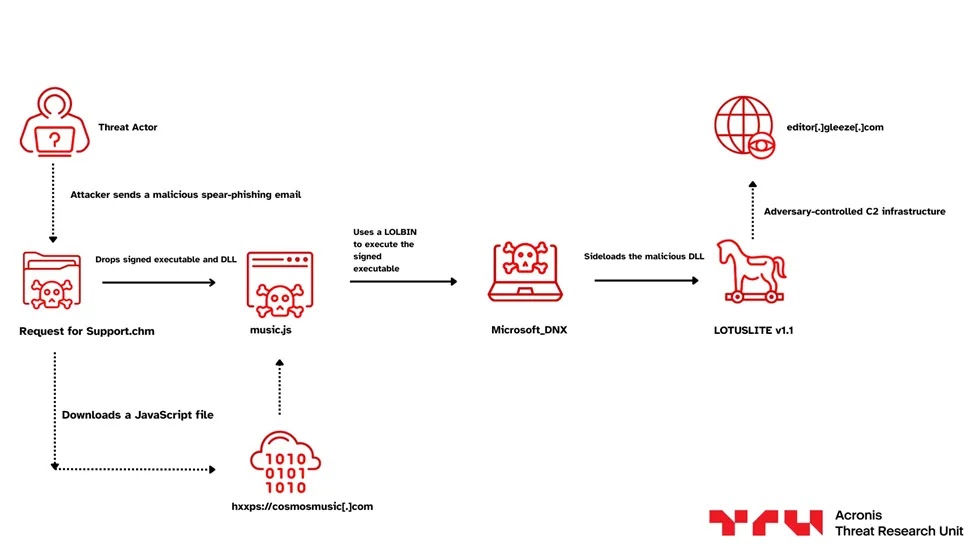
When the victim launches the signed executable, the malicious DLL takes over execution. Acronis said the DLL resolves the export function DnxMain, which hands control to the backdoor. From there, LOTUSLITE connects to a dynamic DNS command-and-control server over HTTPS, blending its traffic into normal encrypted web activity.
The malware supports remote shell access, file operations, and session management. Those functions point to long-term intelligence collection rather than smash-and-grab disruption, which is one reason researchers framed the campaign as espionage-focused.
Why defenders should pay attention
This case shows why signed software cannot serve as a security guarantee by itself. The attackers did not need to tamper with Microsoft’s binary. They only needed to abuse how it searched for a library at runtime. That keeps the visible starting point legitimate while moving the real payload into a place many defenses inspect less aggressively.
Researchers also said this LOTUSLITE variant changed a command-and-control magic value compared with earlier samples. That small tweak can help the malware dodge detection logic built around older network signatures.
The campaign also appears broader than a single-country operation. Acronis said it saw related infrastructure and lure material used in activity tied to Korean diplomatic and policy themes, which suggests the operators keep the same core toolkit while changing the surface story to fit each target set.
Key details at a glance
| Item | Details |
|---|---|
| Malware | LOTUSLITE backdoor |
| Delivery method | DLL sideloading |
| Trusted file abused | Microsoft_DNX.exe |
| Primary target theme | India’s banking sector |
| Secondary theme observed | Korea-related geopolitical targets |
| Suspected actor | Mustang Panda, with moderate confidence |
| Main capabilities | Remote shell, file operations, session management |
| C2 method | Dynamic DNS over HTTPS |
The table above reflects the public findings Acronis published this week about the latest LOTUSLITE activity.
What security teams should do
- Watch for unusual DLL loading by legitimate Microsoft executables, especially from user-writable or temporary directories.
- Restrict DLL loading with application control rules that enforce trusted paths, not just trusted signatures.
- Hunt for Microsoft_DNX.exe running in unusual folders or from archives tied to financial, diplomatic, or policy-themed lures.
- Inspect outbound HTTPS traffic to dynamic DNS infrastructure when the source process chain looks unusual.
- Focus detection on behavior and execution chains, because file reputation alone may miss signed-binary sideloading.
FAQ
LOTUSLITE is a backdoor used in targeted espionage campaigns. In this case, Acronis said the malware supported remote shell access, file handling, and session management.
They used it to improve trust and lower suspicion. A signed executable can look harmless at launch even when it loads a malicious DLL from the same folder.
Acronis said the lure material pointed to India’s banking sector, while related infrastructure and content also overlapped with Korea-focused geopolitical activity.
Acronis assessed with moderate confidence that the activity aligns with Mustang Panda, based on infrastructure and operational behavior.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages