More than 2,000 internet-exposed FortiClient EMS servers raise concern as Fortinet confirms active exploitation

More than 2,000 FortiClient EMS instances appear reachable from the public internet at a time when Fortinet has confirmed in-the-wild exploitation of a critical FortiClient EMS flaw. Fortinet’s advisory says CVE-2026-35616 is an improper access control issue that may let an unauthenticated attacker execute unauthorized code or commands through crafted requests.
The exposure matters because FortiClient EMS is the central management layer for endpoint clients and policy control. If an attacker compromises that server, they may gain a path into endpoint management workflows, administrator functions, and broader enterprise access tied to the EMS environment. This risk is an inference from the product’s role and the severity of the flaw, not a quoted Fortinet statement.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
CISA has already added CVE-2026-35616 to the Known Exploited Vulnerabilities catalog. NVD shows the flaw entered KEV on April 6, 2026, with a federal remediation deadline of April 9, 2026. That alone tells defenders this is not a theoretical issue.
What Fortinet has confirmed
Fortinet says CVE-2026-35616 affects FortiClient EMS 7.4.5 through 7.4.6 and has been exploited in the wild. The company urges customers to install the hotfix for 7.4.5 and 7.4.6, and says the upcoming 7.4.7 release will include the fix as well. Fortinet also says the 7.2 branch is not affected.
NVD describes CVE-2026-35616 as an improper access control vulnerability in FortiClient EMS 7.4.5 through 7.4.6 that may allow an unauthenticated attacker to execute unauthorized code or commands via crafted requests. NVD also shows a CVSS v3.1 vector of AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H, which reflects a remotely exploitable, no-authentication scenario with high impact across confidentiality, integrity, and availability.
This is not the only recent FortiClient EMS problem. Fortinet previously disclosed CVE-2026-21643, an SQL injection flaw that it also said was exploited in the wild. Fortinet’s advisory says that issue affected FortiClient EMS 7.4.4 and was fixed in 7.4.5 or later.
Why the “2,000 exposed instances” figure matters
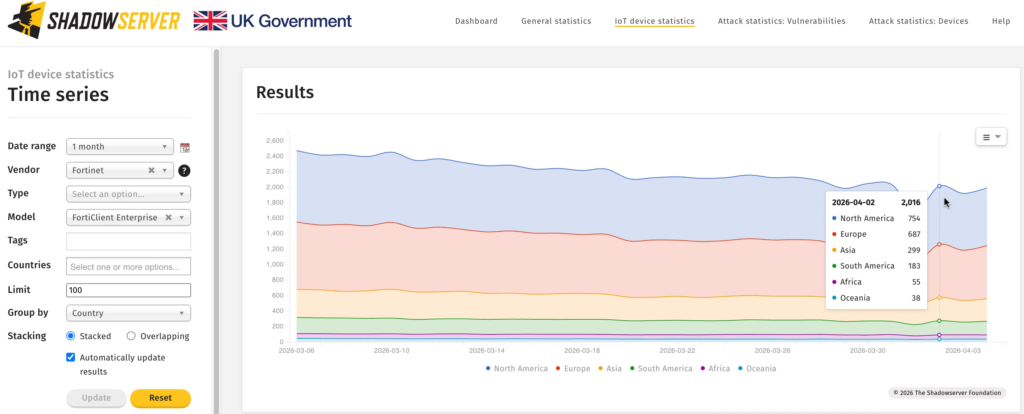
Public reporting that cites Shadowserver says roughly 2,000 FortiClient EMS instances are exposed online, with the United States and Germany among the largest visible groups. I could open Shadowserver’s dashboard shell, but the numeric dataset did not render directly in the fetched page, so I’m attributing the count to reputable reporting that cites Shadowserver rather than claiming I read the live number off the dashboard myself.
That combination creates the real story here. One actively exploited FortiClient EMS bug would already justify immediate patching. Two recent unauthenticated FortiClient EMS flaws, paired with a large number of internet-facing deployments, create a much bigger attack surface for opportunistic scanning and targeted intrusion attempts.
Even if only a fraction of those public instances remain vulnerable, the exposure window still looks serious. Internet-facing management software almost always draws attention quickly once a CVE becomes public, especially when exploitation is already underway. That last point is an inference based on common attack patterns, supported by the confirmed active exploitation status of both CVEs.
FortiClient EMS vulnerabilities at a glance
| Item | Details |
|---|---|
| Newly KEV-listed flaw | CVE-2026-35616 |
| CVE-2026-35616 issue type | Improper access control |
| CVE-2026-35616 affected versions | FortiClient EMS 7.4.5 through 7.4.6 |
| CVE-2026-35616 status | Exploited in the wild |
| Earlier exploited flaw | CVE-2026-21643 |
| CVE-2026-21643 issue type | SQL injection |
| CVE-2026-21643 affected version | FortiClient EMS 7.4.4 |
| CVE-2026-21643 fix | Upgrade to 7.4.5 or above |
| Reported exposure | About 2,000 internet-exposed instances, per public reporting citing Shadowserver |
What organizations should do now
- Apply Fortinet’s hotfix for FortiClient EMS 7.4.5 and 7.4.6 immediately, or move to a fixed release path as Fortinet recommends.
- Upgrade any FortiClient EMS 7.4.4 deployment to 7.4.5 or later to address CVE-2026-21643.
- Remove direct internet exposure from the EMS management interface wherever possible. Put access behind a VPN, management network, or strict allowlist. This is best-practice guidance based on the product’s role and the confirmed attack activity.
- Review logs for unexpected API requests, suspicious outbound connections, and administrative changes. Fortinet’s advisories confirm the flaws allow unauthorized code or command execution, so defenders should assume post-exploitation activity is possible.
- Treat unpatched internet-facing EMS servers as high priority exposure until they are fixed or removed from public reach.
FAQ
It is a FortiClient EMS improper access control vulnerability that may let an unauthenticated attacker execute unauthorized code or commands via crafted requests. Fortinet says it has been exploited in the wild.
Fortinet says FortiClient EMS 7.4.5 through 7.4.6 are affected, while 7.2 is not affected.
That is a separate FortiClient EMS SQL injection flaw that Fortinet also said was exploited in the wild. Fortinet’s advisory says it affected 7.4.4 and was fixed in 7.4.5 or later.
Yes. NVD shows CVE-2026-35616 was added to CISA’s Known Exploited Vulnerabilities catalog on April 6, 2026, with an April 9, 2026 due date for federal agencies.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages