Nearly 6 million internet-facing FTP servers remain exposed in 2026, Censys warns
Nearly 6 million internet-facing hosts still run FTP in 2026, according to a new Censys exposure brief. The firm says it observed about 5,949,954 hosts with at least one public-facing FTP service in April 2026, down 40% from more than 10.1 million in 2024.
That drop is real, but the risk has not disappeared. Censys says the main problem now is not a handful of purpose-built FTP environments. It is the large number of default or inherited deployments spread across shared hosting providers, broadband networks, and older infrastructure that still leaves the protocol exposed to the public internet.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
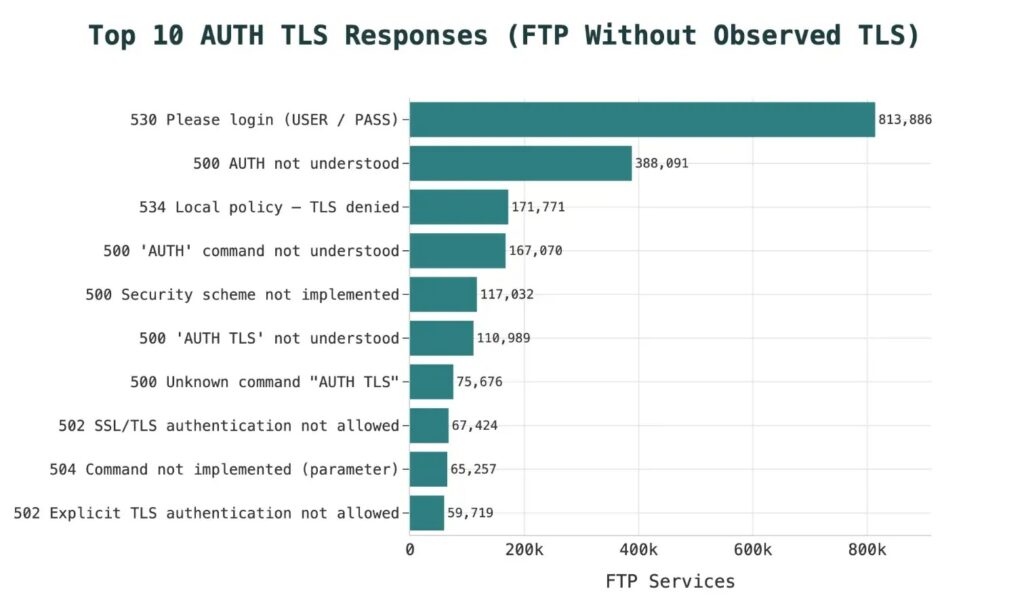
Encryption remains the biggest dividing line. Censys found that about 58.9% of observed FTP hosts completed a TLS handshake, while roughly 2.45 million hosts showed no observed evidence of TLS on any FTP service. Censys also notes that this does not prove every one of those systems transmits data in cleartext, but it does mark a large population with no observed evidence of encrypted FTP sessions.
Why the remaining FTP footprint still matters
FTP still creates unnecessary risk because it was built for a different internet. If administrators leave it running with weak defaults or without properly enforced encryption, credentials and files can remain exposed to interception or downgrade-style operational mistakes. This is the core concern Censys highlights in its 2026 brief.
The report also shows that the problem varies sharply by geography. Among the top 10 hosting countries, mainland China and South Korea had the lowest TLS adoption rates at 17.9% and 14.5%, respectively. Censys also found that Japan accounted for 71% of all FTP servers worldwide that still relied on deprecated TLS 1.0 and 1.1.
That mix matters because it shows two overlapping problems. Some servers still show no observed TLS at all, while others do support encryption but still rely on legacy protocol versions that modern security teams have spent years trying to retire.
Default configurations still drive the exposure
Censys says Pure-FTPd remains the most common daemon on the public internet, running on roughly 1.99 million services. The report ties much of that footprint to cPanel hosting environments, where Pure-FTPd often arrives as part of the default software stack rather than a deliberate standalone deployment.
The firm also points to a notable Microsoft IIS FTP issue. More than 150,000 IIS FTP services reportedly return a “534” response that suggests TLS was never properly configured. Censys says IIS can appear to require encryption by policy, but a fresh installation may still accept cleartext credentials if no certificate is actually bound to the FTP site.
Another blind spot comes from port assumptions. Censys says scanning only port 21 misses a meaningful part of the attack surface because tens of thousands of FTP services run on alternate ports such as 10397 or 2121, often in telecom or NAS-related environments.
Quick breakdown
| Metric | Censys finding |
|---|---|
| Internet-facing FTP hosts | ~5,949,954 |
| Change since 2024 | Down 40% from 10.1 million |
| Hosts with observed TLS handshake | ~58.9% |
| Hosts with no observed evidence of TLS | ~2.45 million |
| Most common FTP daemon | Pure-FTPd |
| Large IIS concern | 150,000+ services returning “534” with TLS not fully configured |
| Regional weak TLS adoption | China 17.9%, South Korea 14.5% |
| Legacy TLS concentration | Japan hosts 71% of FTP servers still using TLS 1.0/1.1 |
What organizations should do next
Censys says the first question should not be how to harden FTP. It should be whether FTP still needs to exist at all. In many environments, SFTP can replace it outright and remove much of the protocol risk by using SSH-based encryption by default.
If an organization must keep FTP online, Censys recommends enforcing explicit TLS and refusing cleartext connections. For Windows Server admins using IIS FTP, the report says teams should verify that a valid certificate is actually bound to the FTP site and confirm that SSL policy is doing what they think it is doing.
The bigger lesson is simple. The remaining exposure does not come mostly from advanced attacks or newly discovered flaws. It comes from old defaults, legacy dependencies, and services that stay online long after safer replacements became available.
Recommended actions
- Replace FTP with SFTP where possible.
- Enforce explicit TLS on any FTP service that must remain online.
- Refuse cleartext connections instead of allowing fallback behavior.
- Check IIS FTP certificate bindings and SSL policy carefully.
- Scan for FTP on nonstandard ports, not just port 21.
- Review shared hosting and inherited platform defaults that may have enabled FTP silently.
FAQ
Censys says it observed about 5,949,954 internet-facing hosts running at least one FTP service in April 2026.
Yes, but slowly. Censys says the total fell 40% from more than 10.1 million hosts in 2024, yet millions of public FTP services still remain exposed.
Not necessarily. Censys says the lack of an observed TLS handshake means it saw no evidence of encryption, but that does not guarantee every such server transmitted files or credentials in cleartext during scanning.
Censys says many IIS FTP deployments appear to require TLS but still lack a bound certificate, which can leave cleartext credential acceptance in place despite what admins may expect from the configuration.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more


User forum
0 messages