New GopherWhisper APT Abuses Slack, Discord, and Outlook in Government Attacks

A newly documented China-aligned threat group called GopherWhisper has been using Slack, Discord, Microsoft 365 Outlook, and file.io to hide command-and-control traffic inside legitimate online services. ESET uncovered the group after finding a custom Go-based backdoor on systems belonging to a Mongolian government organization.
The group has been active since at least November 2023 and appears focused on cyberespionage. ESET says GopherWhisper infected roughly 12 systems inside the Mongolian government target, while Slack and Discord command traffic suggested dozens of other victims may exist.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign stands out because the attackers did not rely only on traditional malware infrastructure. Instead, they used trusted collaboration platforms and cloud services that many organizations already allow through their networks.
Why GopherWhisper matters
GopherWhisper shows how APT groups can blend into normal business traffic. Slack, Discord, Outlook, Microsoft Graph, and file.io can all look less suspicious than unknown command servers, especially in environments where employees use cloud platforms daily.
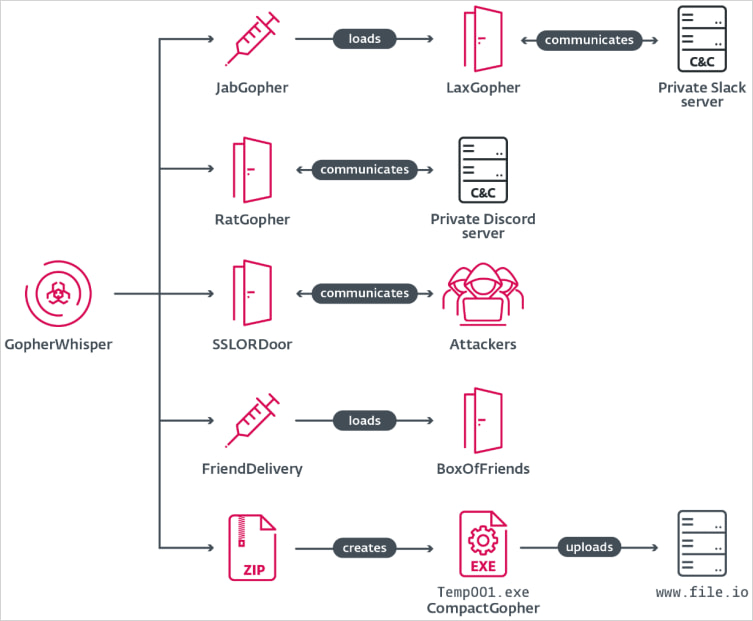
ESET says the group’s malware set includes several custom tools, most of them written in Go. The toolkit includes LaxGopher, RatGopher, BoxOfFriends, JabGopher, FriendDelivery, CompactGopher, and SSLORDoor.
The name GopherWhisper comes from two details. Many tools are written in Go, whose mascot is the gopher, and one malicious component used the filename whisper.dll.
How the attackers used legitimate services
LaxGopher uses a private Slack server for command-and-control. It can retrieve commands, execute them through the Windows Command Prompt, and download additional malware.
RatGopher uses a private Discord server for the same purpose. It receives commands, executes them, sends results back to a configured channel, and can upload or download files through file.io.
BoxOfFriends uses Microsoft 365 Outlook through the Microsoft Graph API. Instead of sending normal network traffic to a suspicious server, the malware creates and modifies Outlook draft emails to exchange commands with the attacker.
At a glance
| Item | Details |
|---|---|
| Threat group | GopherWhisper |
| Attribution | China-aligned APT |
| First known activity | At least November 2023 |
| Main known target | Mongolian government entity |
| Confirmed infected systems | Around 12 systems in one Mongolian government organization |
| Possible wider victim count | Dozens, based on C2 traffic |
| Main language used | Go |
| Other language used | C++ |
| Services abused | Slack, Discord, Microsoft 365 Outlook, Microsoft Graph, file.io |
| Main goal | Cyberespionage and data theft |
| Researcher | ESET |
GopherWhisper’s malware toolkit
ESET’s analysis shows a modular toolset built for persistence, command execution, payload delivery, and exfiltration. The tools overlap in purpose but use different communication channels, giving the attackers backup options.
| Tool | Purpose |
|---|---|
| LaxGopher | Go-based Slack backdoor for command execution and payload downloads |
| RatGopher | Go-based Discord backdoor for command execution and file transfers |
| BoxOfFriends | Go-based Outlook and Microsoft Graph backdoor using draft emails for C2 |
| JabGopher | Injector that launches svchost.exe and injects LaxGopher |
| FriendDelivery | Malicious DLL loader and injector for BoxOfFriends |
| CompactGopher | Go-based file collection and compression tool that exfiltrates data to file.io |
| SSLORDoor | C++ backdoor using OpenSSL BIO over raw sockets on port 443 |
SSLORDoor gives the attackers another route for remote control. ESET says it can execute commands, enumerate drives, and perform file operations such as reading, writing, deleting, and uploading files.
CompactGopher handles data theft. It compresses files from the command line and uploads them to file.io through the service’s public API.
ESET recovered attacker messages
The attackers made a major operational mistake by hardcoding credentials in some Go-based backdoors. ESET used those credentials to access attacker-controlled Slack, Discord, and Microsoft Outlook accounts.
That access gave researchers unusual visibility into the group’s internal activity. ESET recovered 6,044 Slack messages going back to August 21, 2024, and 3,005 Discord messages dating back to November 16, 2023.
Source: ESET
The recovered traffic included commands, uploaded files, and experimental activity. This helped ESET understand how the attackers operated after compromise and how the toolset evolved.
Why ESET links the group to China
ESET says several signals point to a China-aligned actor. The timing of Slack and Discord commands largely matched working hours in the UTC+8 time zone, which aligns with China Standard Time.
Researchers also found the zh-CN locale in Slack metadata. When ESET shifted timestamps to UTC+8, it saw little activity outside an 8 a.m. to 5 p.m. working-day pattern.
ESET also created a new group name because it found no clear code overlap, tactics overlap, or targeting overlap that would connect the toolset to a previously tracked APT group.
Why Slack, Discord, and Outlook make detection harder
Using trusted platforms gives attackers several advantages. Many security tools treat cloud and collaboration services as normal traffic, especially when users and IT teams rely on them every day.
This can help malware avoid basic network blocks. A connection to Microsoft Graph, Slack, Discord, or file.io may look like regular user activity unless defenders inspect context, identity, behavior, and endpoint activity.
The technique also complicates response. Blocking an entire service may disrupt business operations, so defenders need targeted detections rather than broad deny rules.
What defenders should watch for
- Unusual Slack, Discord, file.io, or Microsoft Graph traffic from servers that do not normally use those services.
- Suspicious Outlook draft activity tied to accounts with no normal reason to automate drafts.
- Go binaries running from unusual directories.
- Unexpected
svchost.exechild processes or DLL injection behavior. - Command Prompt execution triggered by unknown binaries.
- File compression activity followed by uploads to file-sharing services.
- Hardcoded tokens, API keys, or suspicious OAuth activity.
- Connections to Discord or Slack from government or restricted environments.
Why this campaign is important for government networks
Government networks often hold diplomatic, legal, administrative, and policy data. That makes them valuable targets for long-running espionage campaigns.
GopherWhisper’s approach suggests patience and flexibility. The group used multiple backdoors, several C2 channels, and a dedicated exfiltration tool rather than relying on a single payload.
The campaign also reflects a broader trend. APT groups increasingly use legitimate cloud platforms because those services help them hide in normal traffic and reduce the need for attacker-owned infrastructure.
FAQ
GopherWhisper is a newly documented China-aligned APT group identified by ESET. It uses custom malware and legitimate services such as Slack, Discord, Outlook, Microsoft Graph, and file.io for espionage operations.
ESET found GopherWhisper malware inside a Mongolian government organization. Its analysis of Slack and Discord traffic suggests there may be dozens of other victims.
ESET found that most of the group’s tools are Go-based. Go malware can run across platforms more easily, and attackers often use it to build compact custom tools.
The BoxOfFriends backdoor used Microsoft Graph API access to create and modify Outlook draft emails for command-and-control communication.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages