New Kiss Loader malware uses Early Bird APC injection in emerging attack campaign

A newly discovered malware loader called Kiss Loader has appeared in a developing Windows attack campaign, and researchers say it uses Early Bird APC injection to run malicious code inside explorer.exe before the process fully starts. G DATA said it first identified the threat in early March 2026 and described it as a previously unseen loader that still looked under active development when analysts found it.
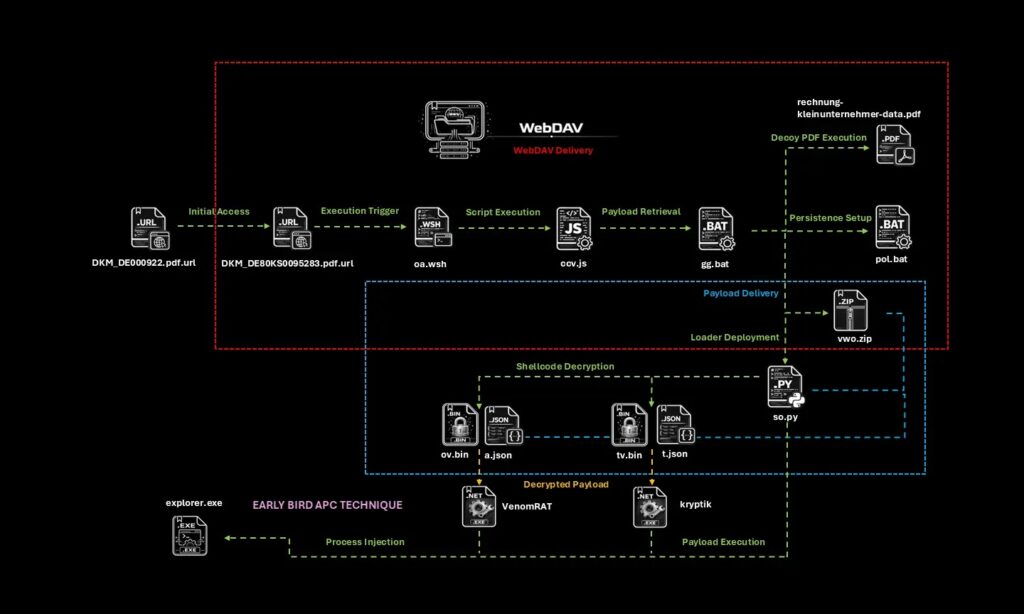
The campaign starts with a Windows Internet Shortcut file disguised as a PDF, named DKM_DE000922.pdf.url. When a victim opens it, the shortcut connects to attacker infrastructure exposed through a TryCloudflare tunnel and begins downloading the next stage. G DATA said that setup gave the operator a flexible way to update or swap files during the campaign.
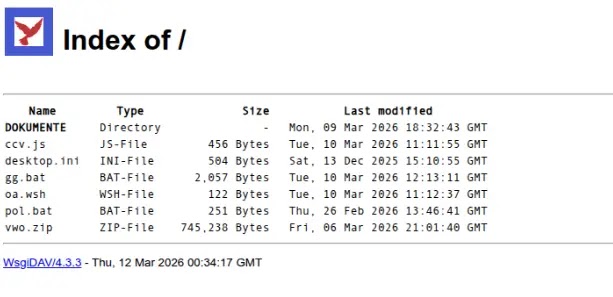
Researchers also found signs that the operation was not fully polished yet. According to G DATA, the attacker’s WebDAV directory remained openly accessible, which let analysts inspect the hosted files directly. The loader also produced unusually verbose runtime output, which the company said strongly suggested ongoing testing or debugging.
Your sample article correctly covered the main elements of the campaign, including the disguised .url file, TryCloudflare delivery, WebDAV hosting, VenomRAT and Kryptik payloads, and the Early Bird APC injection method.
How the infection chain works
G DATA’s analysis shows that the attack begins with the .url file, which poses as a harmless PDF. Once launched, it fetches additional files from the attacker-controlled environment. The infection chain then moves through scripts and archived components before reaching the Python-based loader.
The archive contains a Python loader that decrypts payloads using keys stored in JSON configuration files. That design helps hide the final malware until late in the execution flow. G DATA said it recovered two final payloads during analysis: VenomRAT and a .NET Reactor-protected file identified as Kryptik.
A batch script also places a persistence file in the Windows Startup folder so the malware can relaunch after a reboot, while a decoy PDF opens to reduce suspicion. These details also appeared in the sample text you shared.
Why Early Bird APC injection matters
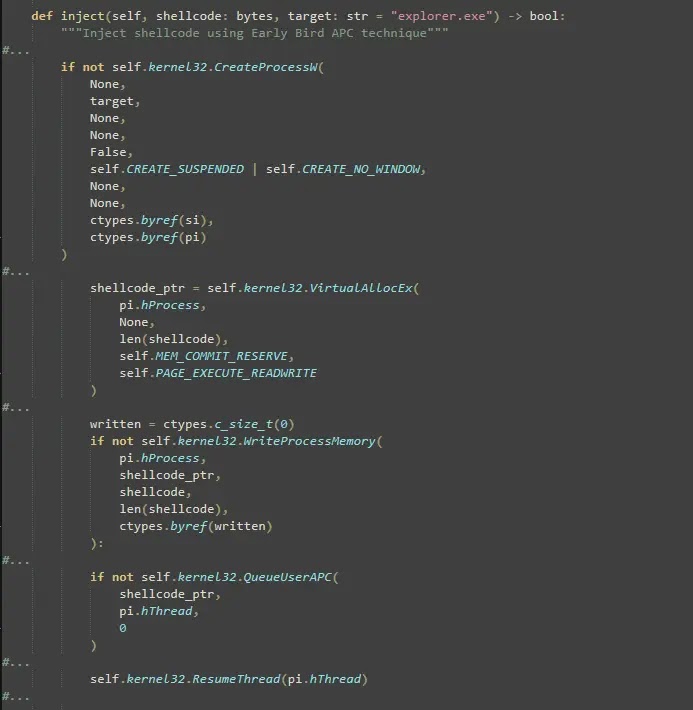
The loader’s most important evasion feature is its use of Early Bird APC injection. G DATA said Kiss Loader creates explorer.exe in a suspended state, writes the decrypted shellcode into the process, queues an APC on the main thread, and then resumes execution. That sequence allows the malicious code to run before Explorer begins normal work.
This technique helps the malware hide inside a trusted Windows process instead of standing out as a separate malicious thread. Security researchers have tracked Early Bird APC injection for years as a stealth-focused code injection method because it can execute payloads before some defenses fully inspect process behavior.
G DATA also said the shellcode was built with Donut, an open-source tool that converts .NET assemblies into memory-resident shellcode. That means the payload can run without dropping a conventional executable to disk, which makes detection harder for older antivirus products.
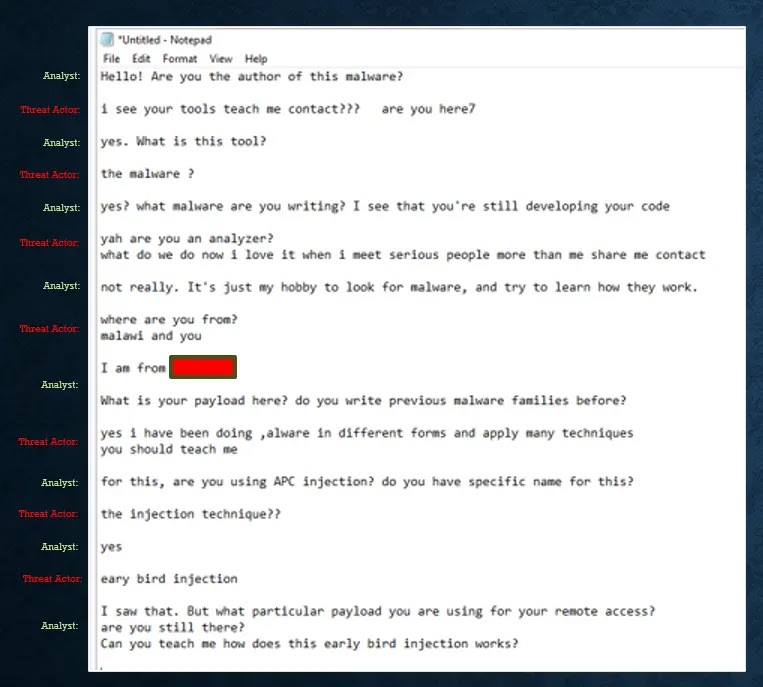
Researcher’s direct interaction with the suspected attacker
One of the most unusual parts of the case involved a live interaction during analysis. G DATA said a researcher left a message in Notepad on the compromised machine, and later received a response from the person believed to be operating the malware. According to the company, the reply confirmed active presence on the host and acknowledged the use of Early Bird APC injection in the loader.
That detail does not change the technical risk by itself, but it does suggest the campaign was still in a hands-on development phase when researchers encountered it. G DATA specifically said the loader and supporting infrastructure appeared to be under active construction.
Key technical findings
- Initial lure: Windows Internet Shortcut file disguised as a PDF
- Delivery path: TryCloudflare tunnel and exposed WebDAV hosting
- Loader type: Python-based malware loader
- Injection method: Early Bird APC injection into explorer.exe
- Payloads recovered: VenomRAT and Kryptik
- Shellcode framework: Donut
- Persistence method: Startup folder placement through script-based execution
Indicators of compromise
| File / Hash | Type |
|---|---|
| 6abd118a0e6f5d67bfe1a79dacc1fd198059d8d66381563678f4e27ecb413fa7 | DKM_DE000922.pdf.url |
| e8f83d67a6b894399fad774ac196c71683de9ddca3cf0441bb95318f5136b553 | oa.wsh |
| 549c1f1998f22e06dde086f70f031dbf5a3481bd3c5370d7605006b6a20b5b0b | ccv.js |
| 6d62b39805529aefe0ac0270a0b805de6686d169348a90866bf47a07acde2284 | gg.bat |
| b4525711eafbd70288a9869825e5bb3045af072b5821cf8fbc89245aba57270a | pol.bat |
| e8dbdab0afac4decce1e4f8e74cc1c1649807f791c29df20ff72701a9086c2a0 | vwo.zip |
| 5cab6bf65f7836371d5c27fbfc20fe10c0c4a11784990ed1a3d2585fa5431ba6 | so.py (Kiss Loader) |
| 130ca411a3ef6c37dbd0b1746667b1386c3ac3be089c8177bc8bee5896ad2a02 | Decrypted ov.bin, identified as VenomRAT |
| 2b40a8a79b6cf90160450caaad12f9c178707bead32bcc187deb02f71c25c354 | Decrypted tv.bin, identified as Kryptik |
These indicators came from the sample text you provided.
What defenders should do
Security teams should treat .url files from untrusted sources as potentially dangerous, especially when they masquerade as document downloads. Researchers also recommend monitoring for APC-based injection into explorer.exe and looking for suspicious outbound connections tied to temporary Cloudflare tunnel infrastructure.
Teams should also review exposure around WebDAV-hosted content and tighten authentication controls on directories that could be abused for payload delivery. G DATA’s findings suggest that small operational mistakes by attackers, such as open repositories and debug-heavy loaders, can create useful detection opportunities.
FAQ
Kiss Loader is a newly observed malware loader that G DATA said appeared in early March 2026. It delivers later-stage payloads and uses Early Bird APC injection to hide inside explorer.exe.
The infection begins with a Windows Internet Shortcut file disguised as a PDF. When opened, it connects through a TryCloudflare tunnel and downloads additional malicious files.
It allows malware to queue malicious code in a suspended legitimate process and run that code before the process starts normal execution. That can make detection harder.
G DATA said it recovered VenomRAT and a .NET Reactor-protected sample identified as Kryptik.
G DATA said the infrastructure and tooling still appeared to be under development when researchers found it. The exposed WebDAV directory and verbose debug output supported that view.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages