North Korean Hackers Target Drug Companies With Fake Excel Files and Dropbox-Based Malware

North Korean hackers linked to the Kimsuky group are targeting pharmaceutical companies with a fake Excel-themed file that secretly launches malware on Windows systems.
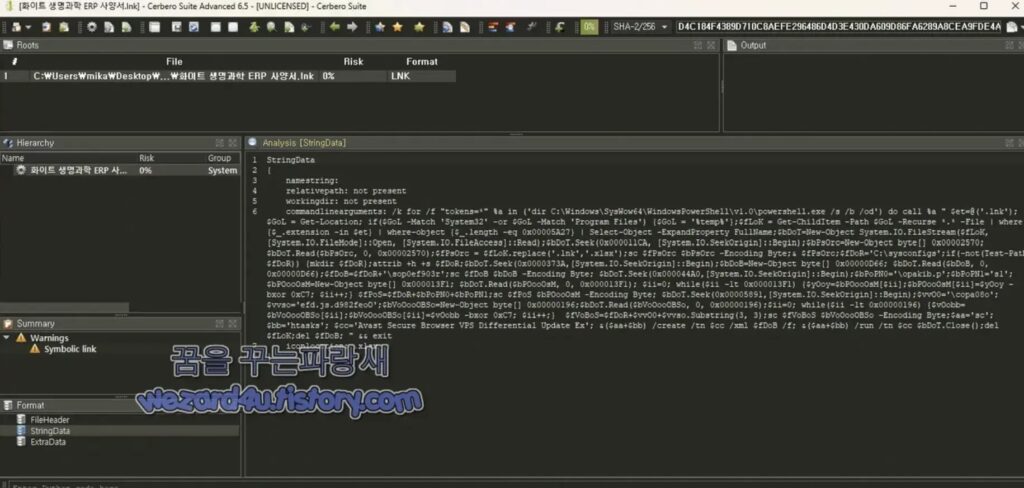
The attack uses a Windows shortcut file named White Life Science ERP Specification.lnk. It appears to be a business spreadsheet, but it contains multiple hidden payloads that run through PowerShell, JavaScript, and Windows Task Scheduler. The goal is to gain silent access to the victim’s machine and collect system information from the infected environment.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign matters because pharmaceutical companies hold sensitive research, intellectual property, patient-related information, manufacturing data, and regulatory documents. A successful compromise could help attackers steal confidential material or maintain long-term access inside a high-value network.
How the fake Excel attack works
The file name is designed to look routine for a life sciences or pharmaceutical employee. A document called “White Life Science ERP Specification” could easily pass as an internal planning file, vendor document, or system specification.
In reality, the .lnk file acts as a container. Researchers found that it holds a decoy Excel document, a PowerShell script, a JavaScript launcher, and a Task Scheduler XML file inside a single shortcut file.
Once the victim opens it, Windows runs a hidden command chain. The infection path moves from LNK to XML to JavaScript to PowerShell, which makes the attack harder to catch at one clear point.
Why the campaign is tied to Kimsuky
Kimsuky is a North Korea-linked cyber espionage group that has operated since at least 2012. MITRE says the group first focused on South Korean government targets, think tanks, and experts, then expanded its activity across government, education, business services, manufacturing, and international organizations.
The use of malicious LNK files, PowerShell, scheduled tasks, hidden folders, and cloud services also matches recent Kimsuky tradecraft. SOC Prime reported earlier in April 2026 that Kimsuky campaigns used malicious LNK attachments, PowerShell, XML task definitions, VBS or PS1 scripting, and Dropbox-linked activity.
This latest pharmaceutical-themed campaign shows how the group continues to adapt its lures to high-value industries. Drug companies are attractive targets because they combine research value with complex supply chains and heavy document exchange.
Key details from the campaign
| Detail | Information |
|---|---|
| Threat group | Kimsuky |
| Country link | North Korea |
| Target sector | Pharmaceutical and life sciences companies |
| Lure file | White Life Science ERP Specification.lnk |
| File type | Windows shortcut disguised as an Excel document |
| Main tools used | PowerShell, JavaScript, Windows Task Scheduler |
| Persistence method | Scheduled task impersonating a browser update |
| Data channel | Dropbox API |
| Main risk | Espionage, system profiling, remote command execution |
The fake document does not need a complex exploit to work. It relies on user execution, file disguise, and Windows scripting features that already exist on most systems.
Inside the payload and persistence chain
The shortcut runs cmd.exe, which launches PowerShell through the SysWOW64 path. This starts the 32-bit PowerShell process on a 64-bit Windows machine.
Attackers often use this approach because some security tools focus more heavily on 64-bit process paths. It can also help the malware blend into older compatibility workflows.
The PowerShell script decrypts embedded components using XOR encoding and drops them into a hidden folder named C:\sysconfigs. That folder name looks close to a real Windows system directory, which may reduce suspicion during a quick manual review.
How the malware keeps access
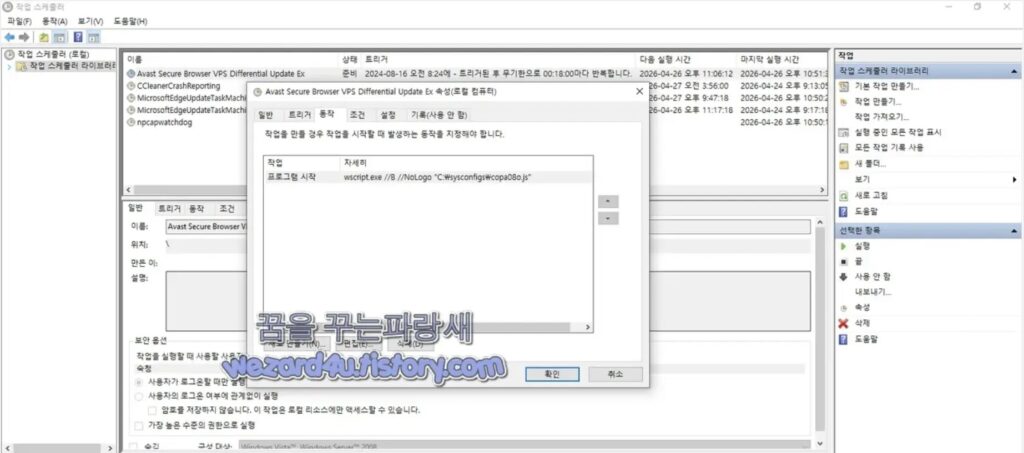
The campaign creates a scheduled task named Avast Secure Browser VPS Differential Update Ex. That name makes the persistence look like a normal browser update job.
The task launches a JavaScript file named copa08o.js, which then helps run the main PowerShell payload named opakib.ps1.
Once active, the PowerShell payload connects to Dropbox through its API. It collects details such as the victim’s domain name, username, operating system version, public IP address, and running processes. It then encodes the data before uploading it to Dropbox.
Why Dropbox abuse is effective
Cloud service abuse gives attackers a practical advantage. Many companies allow Dropbox, GitHub, Google Drive, Microsoft services, or similar platforms because employees use them for legitimate work.
That creates a visibility problem. Security tools may see traffic going to a known cloud provider rather than an obvious attacker-controlled server.
Kimsuky and related North Korean activity have used cloud services before. Fortinet reported in April 2026 that DPRK-linked campaigns used GitHub as command-and-control infrastructure, while SOC Prime described Dropbox abuse in related Kimsuky LNK campaigns.
File indicators reported in the campaign
| Indicator type | Value |
|---|---|
| File name | White Life Science ERP Specification.lnk |
| MD5 | 5c3bf036ab8aadddb2428d27f3917b86 |
| SHA-1 | e9c16aa2e322a65fc2621679ca8e7414ebcf89c0 |
| SHA-256 | d4c184f4389d710c8aefe296486d4d3e430da609d86fa6289a8cea9fde4a1166 |
| Dropped folder | C:\sysconfigs |
| PowerShell payload | opakib.ps1 |
| JavaScript launcher | copa08o.js |
| Scheduled task name | Avast Secure Browser VPS Differential Update Ex |
Security teams should add these indicators to endpoint detection, SIEM, and threat-hunting workflows. They should also search for suspicious scheduled tasks that impersonate security tools or browser update processes.
What pharmaceutical companies should do now
Drug companies should treat this campaign as an espionage risk, not just a routine malware alert. The lure targets business workflows, and the payload focuses on stealth, persistence, and system profiling.
IT teams should make Windows show file extensions by default. This simple change helps users see when a supposed spreadsheet ends in .lnk.
Security teams should also restrict unnecessary PowerShell execution, especially from shortcut files, temporary folders, and unusual SysWOW64 paths.
Recommended actions:
- Enable Windows file extension visibility for all users.
- Block or quarantine
.lnkfiles delivered through email. - Monitor PowerShell launched from
SysWOW64. - Hunt for the
C:\sysconfigsfolder. - Review scheduled tasks with names that imitate browser or security updates.
- Monitor Dropbox API traffic from systems that do not need Dropbox.
- Add the reported hashes to endpoint detection tools.
- Use application control to restrict script execution.
- Train staff to report unexpected ERP, specification, or vendor documents.
- Isolate any machine that opened the suspicious shortcut file.
Why this is a serious supply chain concern
Pharmaceutical companies work with suppliers, regulators, consultants, laboratories, hospitals, and software providers. That constant document exchange gives attackers many opportunities to disguise malware as ordinary business material.
A fake ERP specification can look believable in this environment. Employees may expect spreadsheets, project files, requirements documents, and system templates from vendors or internal teams.
This makes prevention harder. Companies need technical controls that stop disguised shortcut files before a user has to make the final decision.
FAQ
The main threat is a malicious Windows shortcut file disguised as an Excel document. It launches scripts that create persistence and connect to Dropbox for data exchange.
The campaign has been attributed to Kimsuky, a North Korea-linked cyber espionage group.
The campaign targets pharmaceutical and life sciences companies, especially organizations that may handle sensitive research, manufacturing, or drug-related data.
The report describes a Windows shortcut file disguised as an Excel document. The attack relies on user execution and scripted payload delivery rather than a traditional Excel vulnerability.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages