One-click Windows Admin Center flaw can let attackers run commands through a tampered link

A newly disclosed Windows Admin Center vulnerability can let an attacker run arbitrary commands after getting a target to open a malicious link. Cymulate Research Labs says the issue affects both Azure-integrated and on-premises deployments, but the impact is much worse for self-managed installations because the attack chain can reach code execution on managed systems. Microsoft assigned the issue CVE-2026-32196.
Microsoft has already applied a server-side fix to Azure-managed Windows Admin Center instances, so cloud customers do not need to patch anything manually for that hosted path. On-premises deployments still need attention from administrators, because the local installation must be updated to close the exposure.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The attack stands out because it needs very little from the victim. Cymulate says a single click on a crafted URL can start the exploit chain, which then abuses weaknesses in how Windows Admin Center handles control flow, redirects, and browser-side trust.
Why this Windows Admin Center bug matters
Windows Admin Center is a browser-based management tool that many IT teams use to manage Windows servers, PCs, clusters, and hybrid infrastructure from one place. That trusted role gives attackers an opening. If they can hijack a legitimate-looking Admin Center flow, they can turn a normal management session into a compromise path.
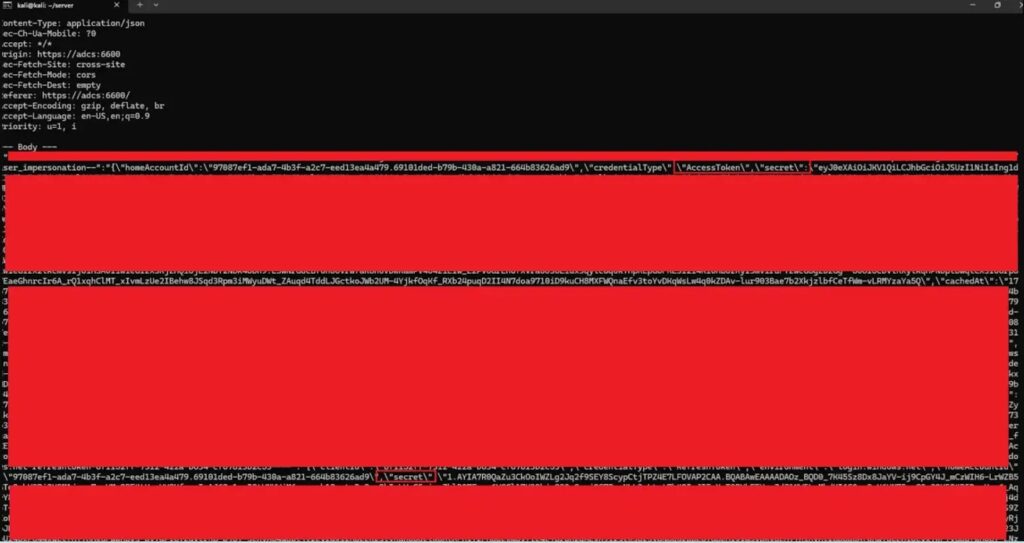
Cymulate says the full chain combines several problems. These include response-based cross-site scripting, weak redirect validation, and, in on-premises setups, insecure storage of Azure access and refresh tokens in browser local storage. Together, those issues can let attackers steal tokens, impersonate users, and in some deployments execute arbitrary PowerShell commands on managed servers.
In Azure-managed environments, the research points to credential theft and spoofing risks through trusted Microsoft-hosted flows. In on-premises environments, the outcome can be more severe because the gateway can be pushed into executing commands on connected systems. If the on-prem gateway also links to Azure, attackers may gain the victim’s cloud privileges as well.
How the exploit chain works
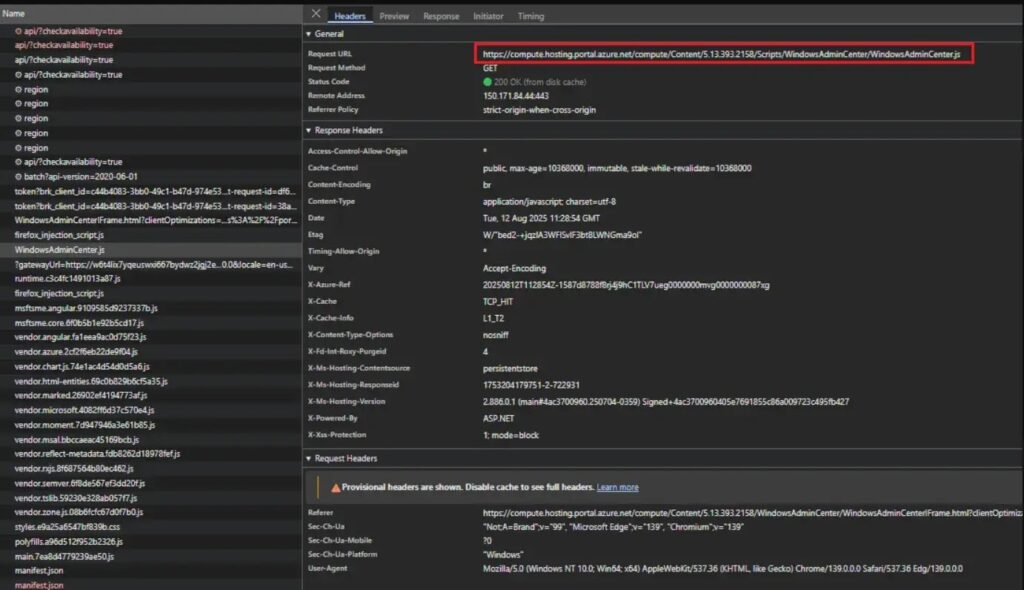
According to Cymulate, the attacker first prepares a tampered Windows Admin Center URL and hosts supporting content on a controlled server. The victim then opens the link, often through phishing, a disguised redirect, or another believable prompt. Windows Admin Center follows that path and receives a malicious response that includes injected script.
Because the application does not handle that response safely enough, the script executes inside a highly privileged browser context tied to Admin Center. From there, the attacker can pivot based on the deployment model. In Azure-connected cases, the script can target credentials and tokens. In on-premises cases, the same foothold can help drive command execution through the gateway and the systems it manages.
Cymulate says it disclosed the flaws to Microsoft on August 22, 2025. The company says Microsoft addressed the Azure-managed path on the service side, while self-hosted customers must update their own installations.
Key details at a glance
| Item | Details |
|---|---|
| CVE | CVE-2026-32196 |
| Product | Windows Admin Center |
| Main risk | One-click remote code execution and credential or token theft |
| Researcher | Cymulate Research Labs |
| User interaction | Required, usually one click on a crafted URL |
| Azure-managed WAC | Server-side fix already applied by Microsoft |
| On-premises WAC | Customers need to update their deployment |
Windows Admin Center’s current release history shows version 2511 as the latest general availability release, and Microsoft says it has been updated multiple times to address security improvements and critical bugs. Microsoft’s Azure extension release notes also show ongoing fixes in April 2026. Those notes do not spell out this CVE directly, but they support the broader point that admins should move to the latest available build and extension level.
For defenders, the practical message is simple. If you run Windows Admin Center on your own infrastructure, you should treat this as an urgent patching issue. If your environment uses Windows Admin Center with Azure connectivity, you should also review token exposure, browser storage practices, and admin session hygiene because the research shows how browser-side weaknesses can turn into much larger hybrid compromises.
What admins should do now
- Update on-premises Windows Admin Center to the latest Microsoft release.
- Review whether any older self-hosted gateways remain active in the environment.
- Limit exposure of admin portals to trusted networks and users only. This is an inference based on the one-click browser attack path described by Cymulate.
- Check for signs of suspicious redirects, unusual admin prompts, or unexpected token use in hybrid environments. This is also an inference from the documented token theft and redirect abuse path.
FAQ
It is a Windows Admin Center vulnerability chain that Cymulate says can lead to one-click remote code execution, credential theft, and Azure token theft depending on deployment type.
For Azure-managed Windows Admin Center instances, yes. Cymulate says Microsoft applied a server-side fix, so those customers do not need to take manual action for that hosted path.
Organizations running on-premises Windows Admin Center remain the main concern until they update to a patched release.
Cymulate describes the chain as unauthenticated and one-click, meaning the attacker mainly needs to lure the victim into opening a crafted link.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages