OpenClaw Framework Triggers Underground Chatter Through Vulnerable Skills Ecosystem
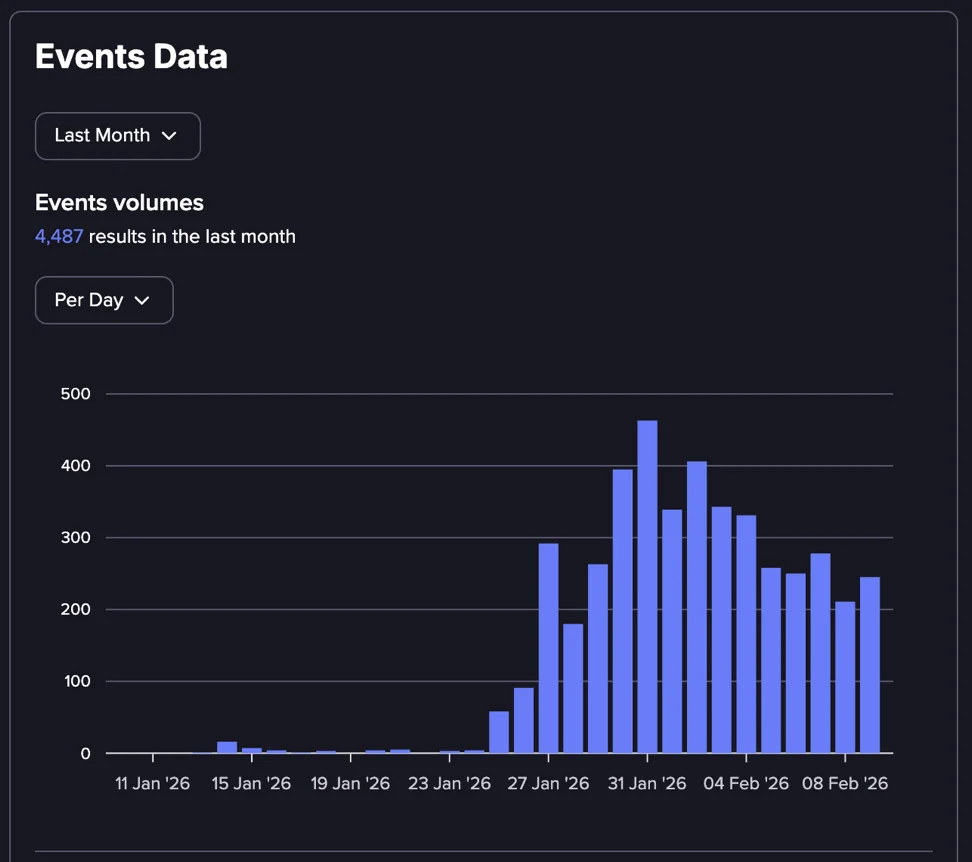
Flare analysis reveals OpenClaw automation platform dominates threat feeds despite limited criminal exploitation. 3,072 mentions across forums show research amplification over active attacks. ClawHub skills marketplace emerges as primary supply chain attack vector. No official CVE assignments confirmed to date.
Peter Steinberger launched ClawDBot (later OpenClaw) November 2025 as AI task automation. Modular skills execute email, schedule, system commands via agent nodes. ClawHub plugin marketplace mirrors npm/PyPI risks without sandboxing.
CVE-2026-25253 enables one-click RCE stealing authentication tokens. Malicious skills deliver infostealers, RATs disguised as productivity tools. Full agent permissions grant credential, file, network access unrestricted.
Flare tracked 2,764 underground records: 1,365 ClawDBot, 864 MoltBot references. 193 skills security discussions, 90 ClawHub mentions confirm ecosystem focus. Only 53 infostealer, 8 botnet references indicate early experimentation.
No commercial tool sales, botnet panels, or pricing threads observed. Research reports drive 70% conversation volume currently. Hype cycle precedes weaponization typical of emerging platforms.
Local agents run root privileges by default. Publicly exposed gateways lack authentication hardening. Dynamic remote code execution bypasses static analysis completely.
Threat Telemetry Table
| Term | Mentions | Context |
|---|---|---|
| OpenClaw | 3,072 | Primary platform |
| ClawDBot | 1,365 | Original naming |
| MoltBot | 864 | Related tooling |
| ClawHub | 90 | Skills marketplace |
| Infostealers | 53 | Payload delivery |
Attack Surface Mapping
- CVE-2026-25253: One-click RCE token theft
- Skills marketplace: Poisoned plugin distribution
- Agent permissions: Root/system execution
- Prompt injection: AI workflow hijacking
- OAuth abuse: Legitimate API exploitation
Shadow deployments evade security team visibility entirely. Trusted automation context grants immediate privilege escalation.
Discussion Analysis
- 70% research/speculation driven
- 20% skills security concerns
- 7% early experimentation
- 3% payload references
- No commercial operations
Enterprise automation platforms require immediate skills allowlisting. Research amplification signals imminent criminal adoption. Plugin ecosystems demand npm-level scrutiny.
FAQ
ClawHub malicious skills marketplace.
CVE-2026-25253 one-click exploitation.
3,072 OpenClaw across 2,764 records.
Early experimentation, no commercial ops.
Root/system by default unsandboxed.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages