Payouts King appears to carry forward Black Basta’s playbook with a sharper ransomware package

A ransomware group called Payouts King has emerged as a credible threat, and Zscaler says several recent attacks tie back with high confidence to operators consistent with former Black Basta initial access brokers. The company’s researchers say those intrusions reused Black Basta-style social engineering, especially spam bombing, Microsoft Teams impersonation, and Quick Assist abuse, before deploying Payouts King ransomware for data theft and selective encryption.
That link matters, but it needs careful wording. Zscaler does not say Payouts King is simply Black Basta under a new name. It says some attacks in early 2026 matched activity from previous Black Basta access brokers and that several of those attacks were attributed to Payouts King with high confidence. That is stronger than a vague similarity claim, but narrower than saying the whole group fully replaced Black Basta.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The Black Basta background is real. Public reporting and later analysis show the group’s internal chats leaked in February 2025, which exposed operations and added pressure on the gang’s ecosystem. Security researchers have since tracked follow-on activity from actors believed to be tied to that network.
How the attacks begin
According to Zscaler, the intrusions often start with spam bombing that floods a victim’s inbox with junk mail. The attackers then contact the target through Microsoft Teams while posing as internal IT staff and steer them into using Quick Assist, a legitimate Windows remote-support tool. Once they gain remote access, they move quickly to deploy malware, steal data, and later run the ransomware stage.
That sequence matches a broader trend seen in other research on suspected former Black Basta operators. ReliaQuest has also described attacks that begin with inbox flooding and shift into Teams-based fake IT contact within minutes, which supports Zscaler’s account of the social-engineering chain.
The social-engineering angle matters because it lets attackers bypass many defenses without exploiting a software flaw first. If a user hands over remote access through a trusted Microsoft tool, the attackers can blend into ordinary help-desk behavior long enough to establish a foothold.
What Payouts King does after access
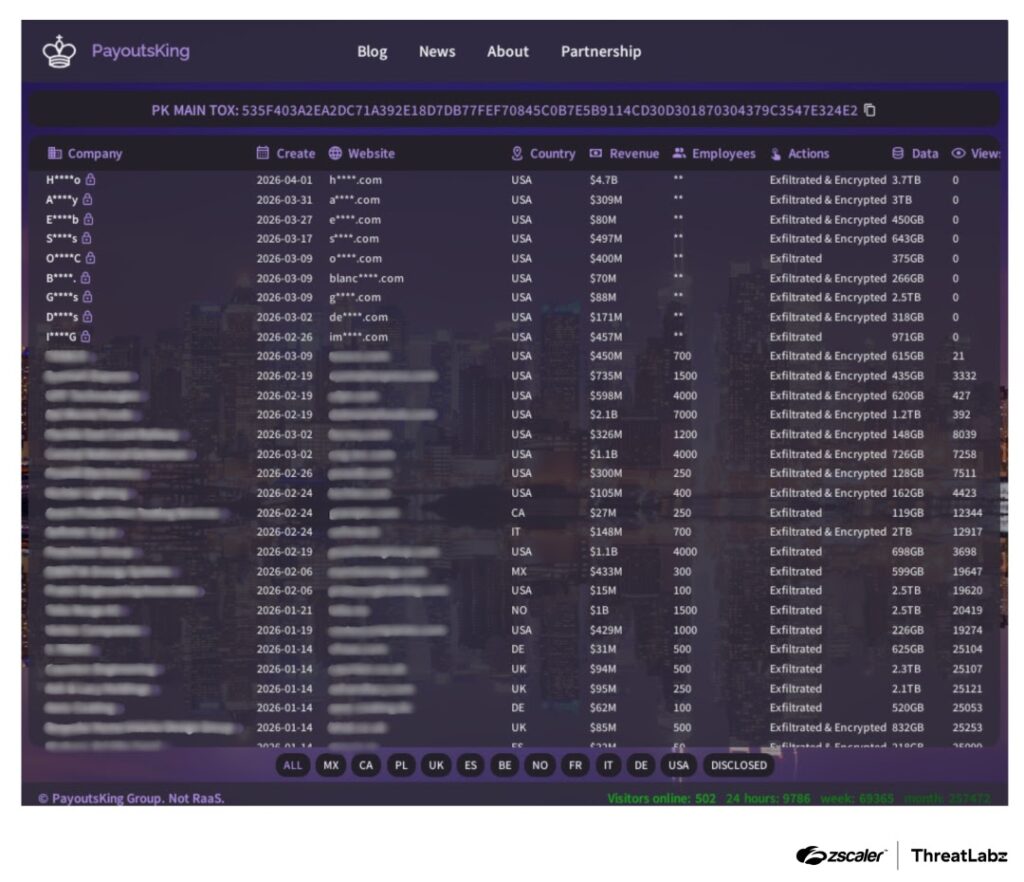
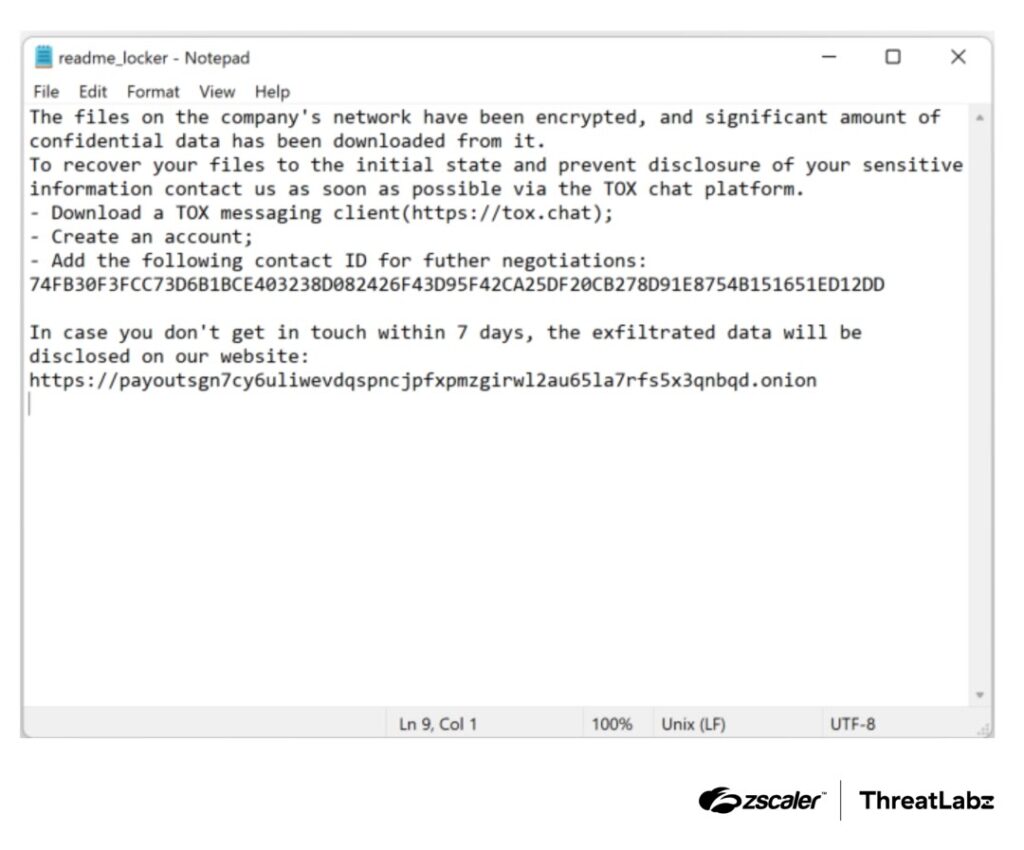
Zscaler says Payouts King steals large amounts of data and then selectively encrypts files, rather than blindly locking everything it can reach. The group also runs a Tor-based leak site and drops a ransom note called readme_locker.txt with contact details through TOX, which fits the now-standard double-extortion model used across much of the ransomware ecosystem.
On the encryption side, Zscaler says the malware uses 4,096-bit RSA together with 256-bit AES in CTR mode. For large files, it speeds execution by splitting data into 13 blocks and only partially encrypting each one, a technique that helps attackers finish the operation faster before defenders can react.
The malware also appears built to frustrate analysis. Zscaler says it uses stack-based string encryption, hashed Windows API resolution, a custom CRC routine, and an anti-sandbox check that requires a specific identity parameter before encryption will start. That design helps the ransomware avoid easy detonation in automated analysis systems.
Why defenders should pay attention
Payouts King does not look like a crude copycat. Zscaler’s write-up presents it as a technically mature ransomware family with careful evasion, selective encryption, and a social-engineering chain that already worked well for earlier Black Basta-linked actors. That combination makes it more dangerous than a new name with recycled branding.
The use of Teams impersonation and Quick Assist also creates a practical problem for defenders. These are normal enterprise tools, so blocking them outright can disrupt support operations. That means organizations need tighter policy controls around who can initiate remote support, who can contact employees as IT, and how help-desk identity gets verified. This is an inference drawn from the tooling and access pattern described by Zscaler and ReliaQuest.
The timing also matters. With Black Basta’s old ecosystem fractured after the 2025 leak, defenders should expect splinter groups and former affiliates to keep reappearing under new labels while preserving old tactics. Payouts King fits that pattern closely, even if the precise organizational structure behind it remains partly opaque.
Key details at a glance
| Item | Details |
|---|---|
| Group | Payouts King |
| Main link | Zscaler ties some early 2026 attacks to activity consistent with former Black Basta access brokers |
| Initial access | Spam bombing, fake IT contact in Microsoft Teams, Quick Assist abuse |
| Extortion model | Data theft plus selective file encryption |
| Ransom note | readme_locker.txt |
| Contact method | TOX |
| Encryption | 4,096-bit RSA plus 256-bit AES-CTR |
| Anti-analysis | String obfuscation, hashed API resolution, custom CRC, anti-sandbox parameter check |
| Post-encryption actions | Deletes shadow copies, clears recycle bin, wipes event logs |
Source for the table: Zscaler ThreatLabz.
What organizations should do now
- Train employees to treat spam bombing, unexpected Teams messages, and urgent remote-support requests as connected signs of a possible ransomware setup.
- Restrict Quick Assist and similar remote tools to approved IT staff and documented support flows. Zscaler specifically calls out Quick Assist abuse in these attacks.
- Require a second verification channel before any employee accepts remote-help requests that arrive through Teams or email. This directly addresses the impersonation stage described in the research.
- Use behavior-based endpoint detection and proactive hunting for shadow-copy deletion, log wiping, and suspicious process termination attempts against security tools. Zscaler says Payouts King targets many antivirus and EDR processes through low-level system calls.
- Prepare for data theft as well as encryption. Leak-site pressure remains part of the operation, so incident response should include containment of exfiltration paths and not only file recovery.
FAQ
Not based on the public evidence cited here. Zscaler says several attacks were tied with high confidence to Payouts King and that the activity was consistent with previous Black Basta initial access brokers. That suggests overlap in operators or access networks, not a full one-line rebrand claim.
Zscaler says they often begin with spam bombing, then move into fake IT contact through Microsoft Teams, followed by Quick Assist abuse to gain remote access.
Researchers say it combines strong encryption, partial encryption for speed, anti-sandbox checks, obfuscation, and aggressive efforts to terminate security software and erase recovery artifacts.
Because both tools are legitimate and familiar in many workplaces. Attackers can blend social engineering with normal support workflows and reach a foothold before defenders realize the request was fake.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages