Phishing campaign abuses LogMeIn Resolve and ScreenConnect to gain remote access at US organizations

A phishing campaign has abused legitimate remote monitoring and remote access tools to compromise more than 80 organizations in the United States. Sophos said the attackers used malicious links that delivered preconfigured LogMeIn Resolve installers, giving them unattended access to victim machines without dropping traditional malware first.
Sophos tracks the cluster as STAC6405 and said the activity began as early as April 2025, with most observed attacks taking place in October and November 2025. The campaign relied on social engineering themes such as Punchbowl invitations and tender solicitations, including emails sent from compromised third-party accounts that looked trustworthy to recipients.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
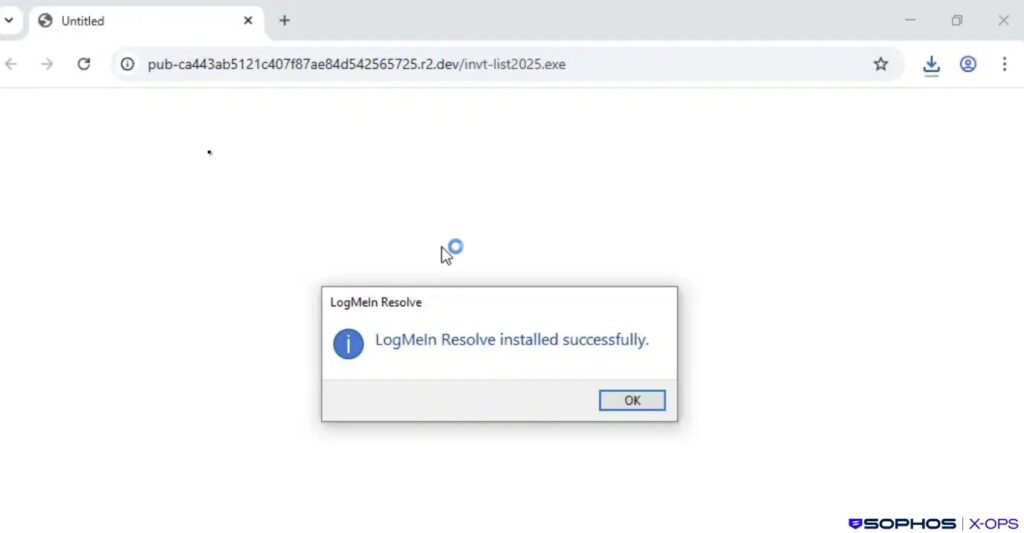
The case matters because it shows how threat actors keep turning legitimate IT tools into covert access channels. GoTo markets LogMeIn Resolve as a platform for unattended access and remote support, while ConnectWise promotes ScreenConnect for attended and unattended remote access. Those same features can help attackers stay quiet once a victim runs the installer.
How the phishing chain worked
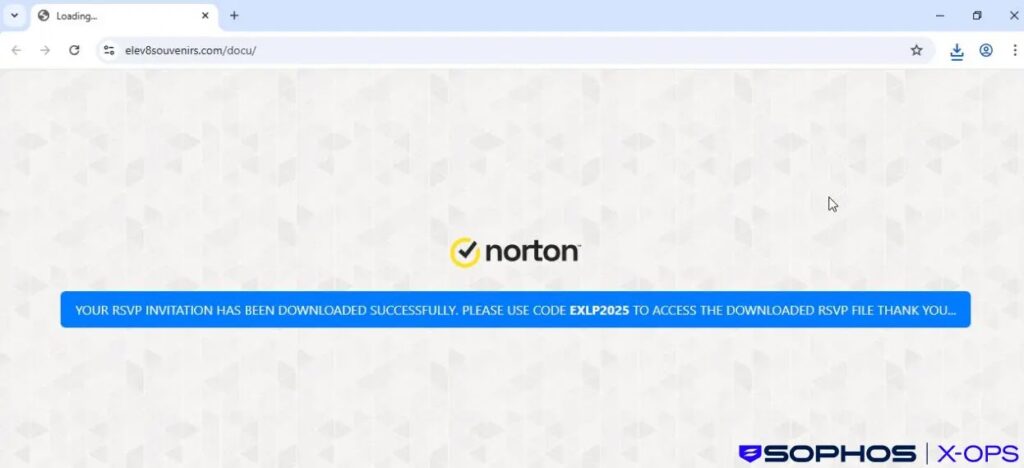
Sophos said each phishing email linked to an attacker-controlled distribution site that hosted a legitimate LogMeIn Resolve installer already configured to register the device to an account controlled by the attacker. The files used ordinary-looking names such as Invitation.exe, ContractAgreementToSign.exe, and statmtsPDF10.25.exe to reduce suspicion.
The threat actor also rotated landing pages over time. Sophos said researchers saw themed sites that mimicked Microsoft Teams and Norton, likely to improve credibility or tailor delivery to different users and environments.
Once the victim ran the file, the attacker gained unattended remote access through LogMeIn Resolve. Sophos said the installed agent wrote a configuration file containing a hard-coded relay domain controlled by the attacker and registered a Windows service with a unique ID tied to that configuration.
Why the campaign stands out
In most cases, the attack stopped after initial access. Sophos said the operators often remained idle once they had remote access, a pattern that fits initial access broker behavior where access gets sold or handed off for later exploitation. That is an analytical assessment from Sophos, not a confirmed public attribution to a larger criminal group.
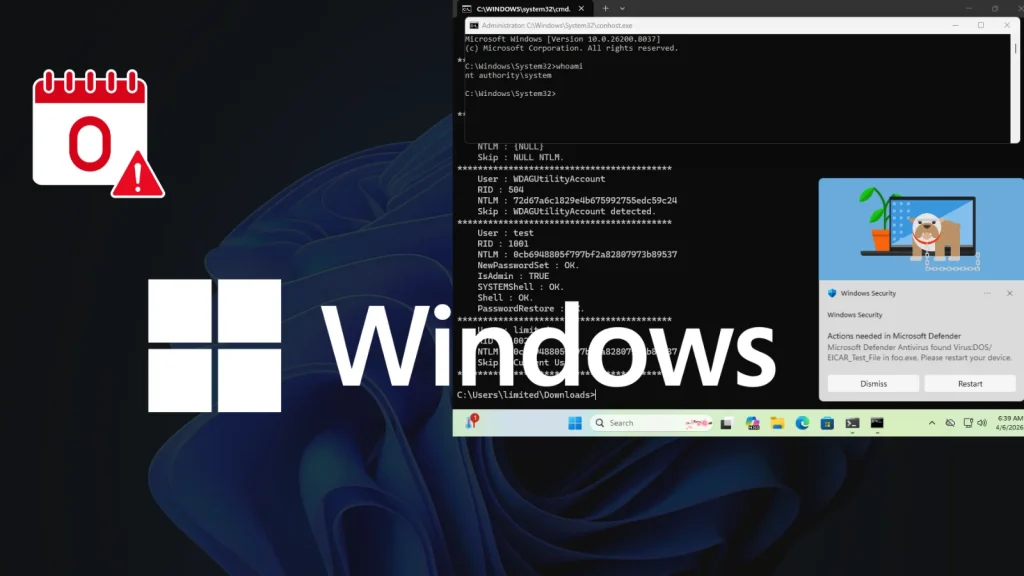
In two intrusions, however, the operators moved fast into a second stage. In one case, they abused an existing ScreenConnect installation on the victim machine to download a ZIP archive packed with HeartCrypt Packer-as-a-Service, containing HideMouse.exe and a malware sample Sophos assessed as behaviorally similar to ValleyRAT.
Sophos said that malware waited four to nine minutes before injecting code into csc.exe, then began stealing browser credentials, session tokens, crypto wallet data, and other system information. In a separate incident, the downloaded binary launched a ScreenConnect client as a service alongside a Java-based remote access tool, and the attacker started enumerating firewall rules before defenders contained the breach.
Key details at a glance
| Item | Confirmed detail |
|---|---|
| Threat cluster | STAC6405 |
| Earliest observed activity | April 2025 |
| Main activity window | October to November 2025 |
| Primary lure themes | Punchbowl invitations and tender solicitations |
| Initial access tool | LogMeIn Resolve |
| Secondary tool observed | ScreenConnect |
| Confirmed impact | More than 80 US organizations |
| Notable second-stage tools | HeartCrypt, HideMouse, ValleyRAT-like malware |
What organizations should do now
- Restrict software installation to approved applications and trusted delivery channels. Sophos recommended blocking unauthorized RMM tools through application control where possible.
- Remove RMM tools that are not required for daily business operations. This recommendation appears directly in Sophos’s guidance for this campaign.
- Enforce strong credential hygiene with password managers or passkeys so a single phish does not open the door to broader compromise.
- Block campaign URLs and indicators of compromise at mail, web, and endpoint layers as soon as they appear.
- Review whether remote access platforms are limited by policy, MFA, and role-based access controls. ConnectWise says ScreenConnect supports role-based restrictions and MFA, and those controls can reduce abuse when configured properly.
- Review how unattended access gets deployed in your environment. GoTo’s own documentation shows unattended access can be rolled out across many machines through installer-based workflows, which is why installer trust must be tightly controlled.
Why legitimate remote tools create a harder defense problem
This campaign did not rely on a custom exploit at the start. It relied on trust. A victim received a convincing message, downloaded a real remote support tool, and unknowingly linked their machine to the attacker’s account. Sophos said that legitimate-software angle helped the operators establish a foothold quietly before any obvious malware appeared.
That makes detection harder because the tools themselves are common in enterprise IT. ConnectWise describes ScreenConnect as a platform for discreet remote access, and GoTo promotes LogMeIn Resolve for unattended access and device management. Security teams need to distinguish approved use from attacker-controlled enrollment, not just flag the product name.
The broader lesson is simple. If a phishing campaign can enroll a device into a legitimate remote access service, the line between malware and admin tooling starts to blur. Organizations need installer controls, stronger verification around remote access enrollment, and clear visibility into which accounts own unattended endpoints. This last sentence is an inference drawn from the campaign mechanics Sophos described and from the vendors’ documented remote access capabilities.
FAQ
STAC6405 is Sophos’s tracking name for the phishing campaign that abused LogMeIn Resolve and, in some cases, ScreenConnect to gain remote access to victim systems in the United States.
Usually no. Sophos said the initial step often involved a legitimate LogMeIn Resolve installer that quietly enrolled the victim system into an attacker-controlled account.
Sophos said more than 80 organizations across multiple industry sectors in the US were affected.
Review whether any endpoints were enrolled into LogMeIn Resolve or ScreenConnect by unknown accounts, block campaign infrastructure, and remove unauthorized RMM tools from endpoints.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages