PNG vulnerabilities in libpng can crash apps and expose memory on affected systems
Two newly disclosed libpng vulnerabilities can let attackers crash apps that parse crafted PNG files, and in some cases leak heap data or corrupt memory. The bugs affect the widely used reference library behind PNG image handling in many apps, services, and embedded systems. libpng lists both issues as high severity and says users should update immediately.
The first flaw, CVE-2026-33416, is a use-after-free bug tied to pointer aliasing in png_set_tRNS and png_set_PLTE. GitHub’s advisory says affected versions run from 1.2.1 through 1.6.55, and the fix shipped in libpng 1.6.56, with the trunk line also patched in 1.8.0.
The second flaw, CVE-2026-33636, affects ARM and AArch64 builds that use Neon-optimized palette expansion. GitHub says the vulnerable range is 1.6.36 through 1.6.55 when hardware optimizations are enabled, while generic C builds and other SIMD paths such as SSE2, VSX, and LSX are not affected.
What CVE-2026-33416 does
According to the libpng advisory, the bug exists because libpng shared a single heap allocation between internal structures with different lifetimes. If an application frees that shared memory through png_free_data() or triggers a second setup call, one pointer is cleared while the other remains dangling and later code can still read from or write to freed memory.
The impact can go beyond a crash. The advisory says the stale pointer can lead to read-after-free behavior that may expose sensitive heap contents, and write-after-free behavior that can corrupt heap memory with attacker-influenced values. GitHub also says researchers demonstrated proof-of-concept arbitrary code execution in some -no-pie environments, which means exploitability depends heavily on allocator behavior and system protections.
That nuance matters. Your sample treats remote code execution as a broad outcome, but the official advisory is narrower. A crash, memory disclosure, and heap corruption are solidly supported. Code execution was demonstrated only in specific conditions, not as a general result across all affected systems.
What CVE-2026-33636 does
The second bug sits in libpng’s ARM Neon palette expansion path. GitHub says the code processes image rows in fixed-size chunks and fails to stop before a final partial chunk, which leads to reads and writes before the start of the intended row buffer.
This issue is reachable during normal decoding of attacker-controlled PNG input when Neon is enabled. The advisory says reliable process crashes are confirmed, information disclosure and heap corruption are plausible, and arbitrary code execution has not been demonstrated for this flaw.
The official libpng release notes and advisory also narrow the blast radius. This is not a universal bug across all libpng deployments. It affects ARM or AArch64 builds with Neon enabled, and it does not affect the generic C code path. That means some servers and apps will be exposed while others using the same library name may not be.
Affected versions and patched releases
| Vulnerability | Affected versions | Patched versions | Main impact |
|---|---|---|---|
| CVE-2026-33416 | 1.2.1 through 1.6.55 | 1.6.56, 1.8.0 trunk | Use-after-free, memory leak risk, heap corruption, possible code execution in limited setups |
| CVE-2026-33636 | 1.6.36 through 1.6.55 on ARM/AArch64 with Neon enabled | 1.6.56, 1.8.0 trunk | Process crashes, possible data leakage, heap corruption |
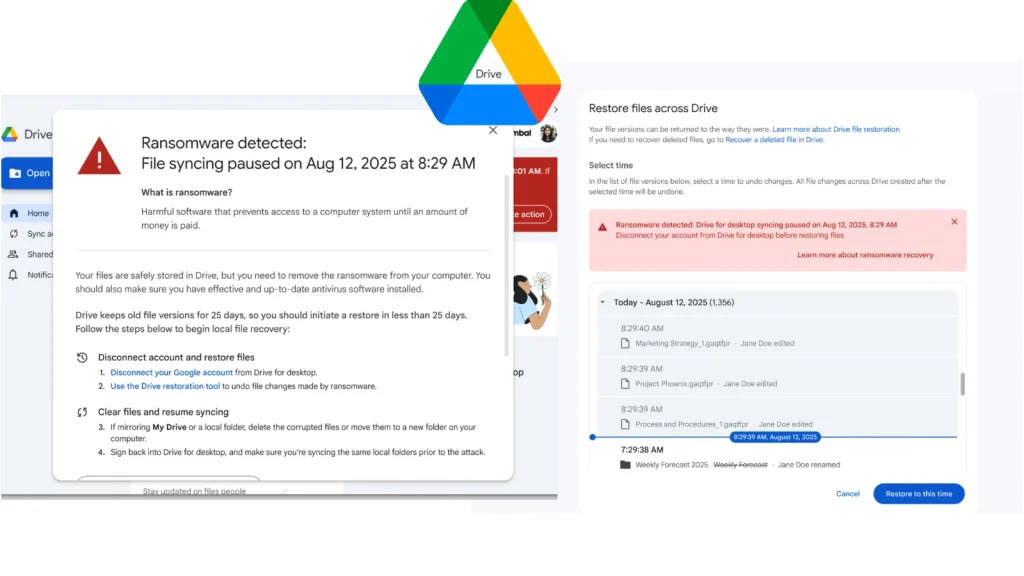
libpng’s maintainer says both bugs are fixed in version 1.6.56 and urges users to update right away. The project’s 2026 news page also notes that the trigger images are valid PNG files, which means simple format checks will not reliably weed them out.
What developers and admins should do
The clearest fix is to update libpng to 1.6.56 or newer. That addresses both high-severity bugs in the current stable branch.
If you cannot patch immediately, GitHub says you can fully avoid CVE-2026-33636 by rebuilding libpng with ARM Neon hardware optimizations disabled, for example with -DPNG_ARM_NEON_OPT=0. That workaround only covers the Neon flaw, so it does not replace a full upgrade.
Teams that handle untrusted image uploads should review any service that decodes PNGs, especially web back ends, media pipelines, mobile apps, and embedded products built on ARM. The biggest near-term risk is denial of service through crashes, but the use-after-free bug adds memory safety concerns that justify fast patching.
Quick takeaways
- Update libpng to 1.6.56 or later.
- Treat CVE-2026-33416 as the broader bug because it affects versions back to 1.2.1.
- Treat CVE-2026-33636 as architecture-specific because it needs ARM or AArch64 with Neon enabled.
- Do not overstate universal code execution risk. The official advisories support crashes and memory exposure more broadly than RCE.
FAQ
CVE-2026-33416 affects libpng 1.2.1 through 1.6.55. CVE-2026-33636 affects 1.6.36 through 1.6.55 on ARM or AArch64 builds with Neon enabled
Yes. libpng fixed both bugs in version 1.6.56, and the trunk line is also patched in 1.8.0.
For CVE-2026-33416, GitHub says researchers demonstrated proof-of-concept code execution in some -no-pie environments. For CVE-2026-33636, the advisory says code execution has not been demonstrated.
No. The ARM-specific flaw needs ARM or AArch64 with Neon enabled. Generic C builds are not affected.
Yes, for the ARM Neon bug only. GitHub says rebuilding with -DPNG_ARM_NEON_OPT=0 avoids CVE-2026-33636, though it may reduce performance.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages