Public Notion pages leaked editor emails and profile photos, researchers say
Anyone who edited a public Notion page may have had their full name, email address, and profile photo exposed through unauthenticated requests, according to security researchers who revived attention around the issue this week. The exposure appears tied to public page metadata and an internal API flow that could return editor profile details without a login.
The concern goes beyond hobby projects and personal notes. Companies use Notion for public help centers, product docs, wikis, and changelogs, which means a public page can reveal the identities and contact details of employees or contributors who touched that content. Researchers and commentators warned that this kind of data could help phishing crews build more convincing lures.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
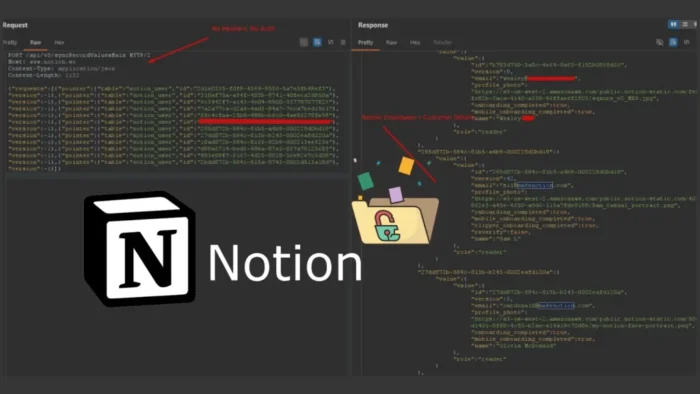
The core claim is that public pages expose editor UUIDs in accessible page data, and those identifiers can then be used in a request to Notion’s syncRecordValuesMain API path to retrieve profile information. Posts from researchers on X and follow-up reporting both describe the same basic workflow and say it works without authentication.
How the exposure reportedly works
Researchers say the issue starts when a Notion page gets published to the web. At that point, editor identifiers tied to the page become available through public-facing data, which gives attackers a starting point for enumerating people who interacted with the document.
From there, the reported attack path stays simple. A single unauthenticated POST request to an internal API endpoint can return user profile data associated with those identifiers, including names, email addresses, and avatar images.
That simplicity is what made the story spread so quickly. Researchers claimed an attacker would not need an active session, cookies, or special privileges to pull the data from public pages, which sharply increases the risk of large-scale scraping.
Why this matters for organizations
For enterprises, the biggest risk is not just privacy loss. Publicly exposed editor data can give attackers a clean list of real employees tied to specific teams, products, or documentation projects, which makes targeted phishing and impersonation easier.
This also creates a discovery problem. Public documentation often ranks well in search engines, which means exposed details tied to those pages may be easy to scrape, index, and correlate with other public information. That raises the value of the leaked data for OSINT work and for social engineering campaigns.
The timeline made the reaction worse. Multiple reports say the same behavior was disclosed through HackerOne in July 2022 and was reportedly marked as informative or out of scope at the time, only to resurface publicly in April 2026 after new testing and public discussion. I could not independently verify the full original HackerOne report text, but that timeline appears consistently across current reporting.
What Notion said
After the issue resurfaced, Notion acknowledged the criticism and said the current behavior is not acceptable, according to multiple reports that cite comments from Notion representative Max Schoening. Those reports say the company is working on a fix.
Early comments attributed to Notion said users were warned about data visibility when publishing pages to the web. Researchers pushed back on that claim and said current publishing prompts did not clearly warn that editor email addresses and profile photos could be exposed.
The reported remediation ideas include stripping personally identifiable information from public-facing responses or masking email addresses through a proxy-style system. Notion has not, at least in the public material I could verify, published a full technical advisory with a rollout date yet.
Key facts at a glance
| Item | Reported detail |
|---|---|
| Exposed data | Full names, email addresses, profile photos |
| Trigger | Editing a Notion page later published to the web |
| Access needed | None, according to researchers and follow-up reports |
| Main concern | Phishing, scraping, and employee profiling |
| Original disclosure timeline | Reportedly first raised in July 2022, resurfaced publicly in April 2026 |
What teams should do right now
- Audit every public Notion page your organization exposes on the web.
- Assume editor details on those pages may already be scrapeable or indexed.
- Limit who edits public-facing pages until Notion ships and confirms a fix.
- Review phishing exposure for staff whose names or emails appear in public docs.
- Watch for an official product update or security advisory from Notion.
FAQ
Researchers say public pages could expose editor full names, email addresses, and profile photos through accessible identifiers and an unauthenticated API request.
Current reporting says no. The described workflow did not require a login, session cookie, or privileged access.
Reports quoting Notion representative Max Schoening say the company acknowledged the current behavior as unacceptable and is working on a fix.
Because public docs can reveal real employee identities tied to real projects, which helps attackers build credible phishing and impersonation attempts.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages