PyTorch Lightning and Intercom packages hit by credential-stealing supply chain attack

A new supply chain attack has hit the Python, npm, and PHP package ecosystems, with malicious versions of Lightning and Intercom packages used to steal developer credentials and spread through repositories.
The main affected Lightning versions are 2.6.2 and 2.6.3, which were pushed to PyPI on April 30, 2026. The project’s advisory says these versions included malicious code consistent with credential harvesting and tells users to remove them, rotate exposed secrets, rebuild affected environments, and pin to version 2.6.1.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign also affected Intercom’s npm package intercom-client version 7.0.4 and the PHP package intercom/intercom-php version 5.0.2. Security researchers linked the attacks to Mini Shai-Hulud, a cross-ecosystem supply chain campaign that targets developer and CI/CD secrets.
What happened
Lightning is widely used in AI and machine learning workflows, which makes the PyPI compromise especially serious for developer workstations, model training environments, and CI pipelines. PyPI currently lists Lightning 2.6.1 as the latest version, while the project advisory identifies 2.6.2 and 2.6.3 as affected.
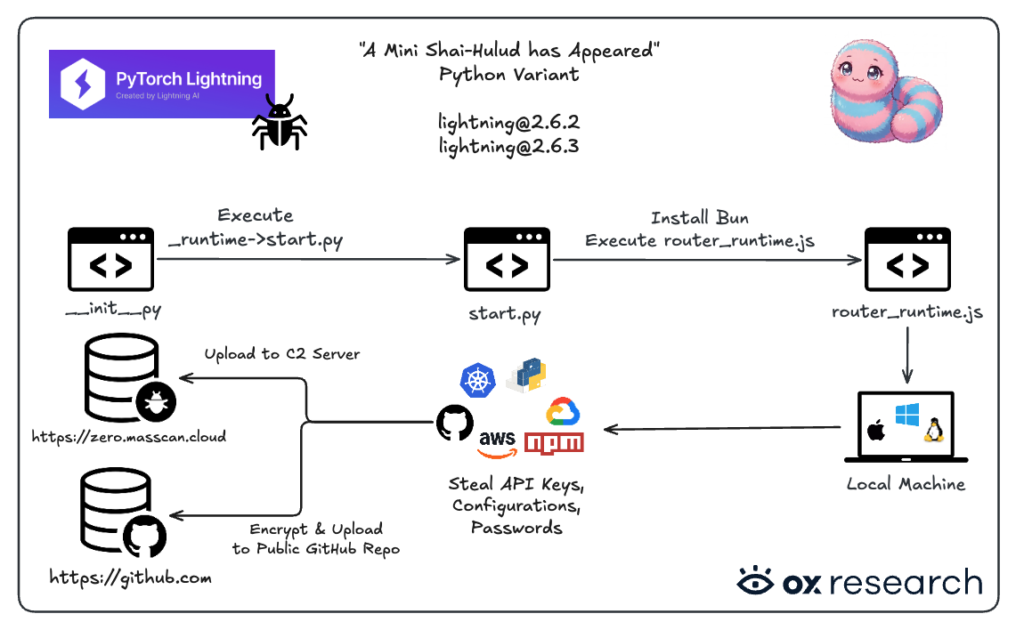
Aikido found that the malicious Lightning package executed code when the package was imported. The malicious code launched a background process from a hidden runtime directory before the legitimate package fully loaded.
Socket and other researchers said the attack used a hidden payload chain involving Python, Bun, and an obfuscated JavaScript file called router_runtime.js. That payload searched for valuable credentials and attempted to use stolen GitHub tokens to spread further.
At a glance
| Package | Ecosystem | Affected version | Main risk | Recommended action |
|---|---|---|---|---|
| lightning | PyPI | 2.6.2 and 2.6.3 | Credential harvesting after import | Remove affected versions and pin to 2.6.1 |
| intercom-client | npm | 7.0.4 | Install-time credential theft | Remove 7.0.4 and downgrade to 7.0.3 |
| intercom/intercom-php | Packagist | 5.0.2 | Composer plugin abuse and secret theft | Audit installs and reinstall from a clean source |
How the Lightning compromise worked
The malicious Lightning versions included a hidden _runtime directory. When a developer imported the package, the code started a Python script named start.py, which then launched a larger JavaScript payload through the Bun runtime.
This approach matters because the malicious behavior did not need a developer to run a separate command. Installing and importing the package could expose the environment.
The payload targeted credentials commonly found on developer machines and CI systems. These included GitHub tokens, npm tokens, SSH keys, cloud credentials, Kubernetes secrets, Vault tokens, Docker credentials, and .env files.
Why GitHub tokens made the attack more dangerous
The malware did not only steal credentials. Researchers said it also checked stolen GitHub tokens and tried to use valid tokens to poison repositories.
Socket reported that the payload could write files into branches across repositories where the stolen token had write access. This gave the attack worm-like behavior because one compromised developer environment could become a bridge into more packages and repositories.
The malicious commits were designed to look like they came from a trusted development workflow. Researchers also found references that impersonated Anthropic’s Claude Code identity in some poisoned commits.
Intercom packages were also compromised
The same campaign reached Intercom’s npm package. Socket confirmed that intercom-client version 7.0.4 contained malicious files named setup.mjs and router_runtime.js, which were not present in the previous version.
The npm package used a preinstall hook, which means the malicious code could run during installation. Users did not need to import the package in application code for the environment to face exposure.
Intercom’s own status page said the malicious intercom-client 7.0.4 release was briefly published and that the latest legitimate version is 7.0.3. It also told users who installed 7.0.4 to remove the package and rotate credentials accessible from that environment.
The attack moved into PHP through Packagist
The campaign also reached intercom/intercom-php version 5.0.2 on Packagist. Socket said the malicious version changed the PHP SDK into a Composer plugin so it could run code during install or update events.
The PHP package used a setup script to download Bun and run the same style of obfuscated JavaScript payload. This gave attackers another path into developer machines and CI runners that use PHP or Laravel workflows.
Socket also said Intercom traced the root cause of the Intercom package compromise to a local install of pyannote-audio, which introduced the compromised Lightning package as a transitive dependency. That finding shows how one infected dependency can cross from PyPI into npm and Packagist.
What credentials were targeted
- GitHub tokens
- npm tokens
- SSH keys
- AWS credentials
- Google Cloud credentials
- Azure credentials
- Kubernetes configuration files
- Vault tokens
- Docker credentials
- .env files
- CI/CD secrets
Why developers and AI teams should act quickly
This incident is serious because it targets the tools developers trust during normal work. A compromised dependency can run in local machines, notebooks, build systems, CI runners, and production pipelines.
AI teams face extra risk because Lightning is common in machine learning workflows. If a compromised training environment has access to cloud keys, model repositories, datasets, or private GitHub repositories, attackers may gain access to much more than one Python package install.
The safest response is to treat any environment that installed Lightning 2.6.2 or 2.6.3, intercom-client 7.0.4, or intercom/intercom-php 5.0.2 as potentially compromised until reviewed.
Recommended actions
- Remove Lightning 2.6.2 and 2.6.3 from all developer and CI environments.
- Pin Lightning to version 2.6.1 until the project publishes further safe release guidance.
- Remove intercom-client 7.0.4 and downgrade to the latest legitimate version listed by Intercom.
- Audit Composer environments for intercom/intercom-php 5.0.2.
- Rotate GitHub tokens, npm tokens, SSH keys, cloud keys, service account credentials, and CI/CD secrets.
- Review GitHub repositories for unexpected branches, workflow files, .claude folders, and .vscode tasks.
- Check CI logs for unusual Bun downloads or execution of router_runtime.js.
- Rebuild affected developer machines and CI runners from a clean state where possible.
- Review cloud audit logs for unusual API calls after the package installation window.
What this means for software supply chain security
The Lightning and Intercom incidents show how quickly a package compromise can move between ecosystems. Python, JavaScript, and PHP projects often share the same developers, GitHub tokens, cloud credentials, and CI infrastructure.
Attackers understand that. By targeting package managers, install hooks, and developer credentials, they can turn trusted tools into delivery channels for more compromises.
For organizations, the lesson is clear. Dependency security can no longer stop at scanning source code. Teams also need token hygiene, least-privilege CI secrets, package pinning, trusted publishing controls, and fast incident response when a registry package turns malicious.
FAQ
The affected Lightning versions are 2.6.2 and 2.6.3. The project advisory tells users to remove those versions and pin to 2.6.1.
The package included credential-harvesting code that ran after import. It used a hidden runtime directory, Python, Bun, and an obfuscated JavaScript payload.
Yes. Intercom-client version 7.0.4 on npm was compromised. Intercom said users should remove it and rotate credentials that were accessible from affected environments.
Yes. Researchers found malicious behavior in intercom/intercom-php version 5.0.2 on Packagist. The package abused Composer plugin execution to run code during install or update events.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages