React2Shell attacks hit 766 Next.js hosts in 24 hours, exposing cloud keys and credentials
A fast-moving attack campaign has exploited the React2Shell flaw to break into hundreds of internet-facing hosts running vulnerable React Server Components and Next.js deployments. Cisco Talos said the attackers compromised 766 hosts in a 24-hour period and stole a wide range of secrets, including cloud credentials, database strings, SSH keys, GitHub tokens, and payment-related secrets.
The vulnerability behind the campaign is CVE-2025-55182, widely known as React2Shell. NVD describes it as a pre-authentication remote code execution flaw in React Server Components caused by unsafe deserialization of payloads sent to Server Function endpoints. Next.js separately tracked its downstream exposure as CVE-2025-66478 and urged users to patch immediately.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This means the risk goes beyond website defacement or a short outage. Once attackers gain code execution, they can pull secrets from application servers, containers, and developer environments, then use them for deeper intrusions, lateral movement, or supply chain abuse. Cisco Talos said the stolen data included package registry credentials, which could let attackers publish malicious updates to trusted software packages.
What happened and why it matters
Cisco Talos tracks the activity under the name UAT-10608. The company said the group automated the full attack chain, from locating exposed hosts to harvesting and exfiltrating credentials, which explains how the campaign moved so quickly across cloud environments and regions.
Talos said the attackers likely used internet-wide scanning platforms such as Shodan or Censys to find reachable Next.js targets. Once they found a vulnerable endpoint, a single crafted HTTP request could trigger remote code execution with no authentication required. Google Threat Intelligence and Microsoft previously warned that threat actors were already exploiting React2Shell soon after disclosure, which shows how quickly this bug became operationally useful.

The campaign also shows why React2Shell remained a top priority even after the initial disclosure in December 2025. Vercel called CVE-2025-55182 a critical vulnerability that required immediate action across React, Next.js, and other frameworks, while Next.js published its own advisory and a remediation utility to help customers update exposed apps.
How the attack worked
According to Cisco Talos, UAT-10608 used a custom command-and-control platform called NEXUS Listener to manage the flood of stolen data. The platform gave operators a web dashboard where they could browse compromised victims, sort credentials by category, review collection phases, and see which targets yielded the most valuable secrets.
After exploiting the vulnerable Server Function endpoint, the attackers dropped a lightweight shell script into a temporary directory using a randomized file name. That script then fetched a multi-stage credential harvester from attacker-controlled infrastructure and began collecting secrets from the compromised environment.
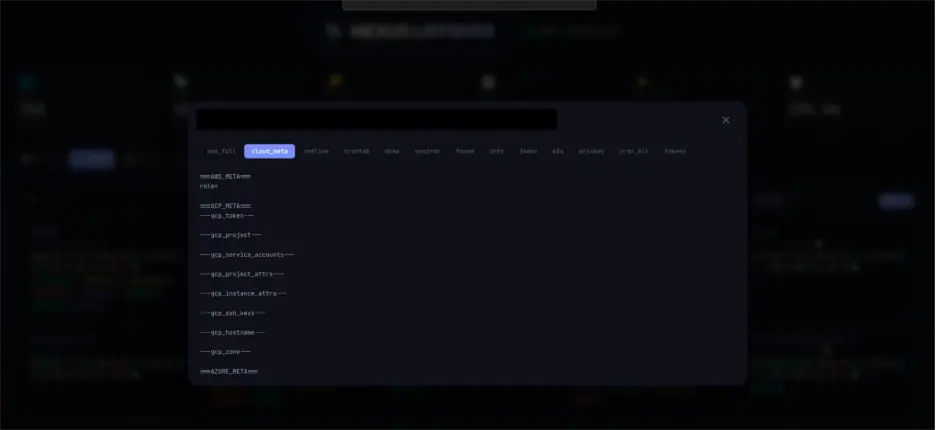
Talos said the operation pulled data such as AWS keys, Azure and Google Cloud credentials, database passwords, SSH private keys, GitHub tokens, Stripe live secret keys, Kubernetes service account credentials, environment variables, and shell history. More than 10,120 files were collected from the breached systems.
Key facts at a glance
| Item | Confirmed detail |
|---|---|
| Main flaw | CVE-2025-55182 in React Server Components |
| Downstream Next.js tracking | CVE-2025-66478 |
| Severity | CVSS 10.0 |
| Attack type | Unauthenticated remote code execution |
| Group | UAT-10608 |
| Confirmed impact | 766 hosts breached in 24 hours |
| Notable stolen data | Cloud keys, DB creds, SSH keys, GitHub tokens, Stripe secrets |
| C2 framework | NEXUS Listener |
What defenders should do right now
- Patch React and Next.js deployments to the latest fixed versions without delay.
- Rotate all secrets that may have touched vulnerable hosts, including AWS keys, database passwords, SSH keys, API tokens, GitHub tokens, and payment credentials.
- Audit application containers and cloud roles for excessive permissions, especially long-lived credentials stored in environment files.
- Monitor outbound traffic from app containers and servers, especially unexpected HTTP connections to unknown infrastructure and activity on port 8080, which Talos linked to this operation.
- Stop reusing SSH key pairs across systems and enforce stronger cloud instance hardening such as IMDSv2 where applicable.
FAQ
React2Shell is the name widely used for CVE-2025-55182, a critical remote code execution flaw in React Server Components. It lets an attacker send a crafted request that can execute code on a vulnerable server before login.
No. The bug sits in React Server Components, but frameworks that rely on that functionality also inherit the risk. Next.js tracked its downstream impact under CVE-2025-66478.
Cisco Talos said the attackers did not just grab a few passwords. They harvested cloud keys, database secrets, package registry credentials, and other sensitive files at scale, which can lead to follow-on intrusions and software supply chain abuse.
Talos said UAT-10608 compromised 766 hosts in a single 24-hour window through an automated workflow.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages