RingH23 toolkit revives sanctioned Funnull operation, hits CDN nodes and MacCMS updates at scale

Threat actors linked by researchers to Funnull, a U.S.-sanctioned infrastructure provider, have launched a large-scale compromise campaign using a modular toolkit dubbed RingH23. The operation targets CDN management nodes and the MacCMS (AppleCMS) software supply chain to inject malicious JavaScript and redirect users to gambling, adult, and other illegal sites.
XLab says its telemetry shows large reach for the malicious JavaScript infrastructure, including typosquatted CDN lookalike domains that drew hundreds of thousands of unique visitors in a single day during peak activity.
XLab links RingH23 to Funnull based on infrastructure overlap and tradecraft consistency, and it describes a shift from renting or hijacking third-party services toward operating a more self-owned server-side framework.
Funnull appeared in U.S. government reporting in 2025 after Treasury sanctioned the company for supporting “pig butchering” cryptocurrency investment scams and linked it to over $200 million in U.S. victim-reported losses.
What RingH23 does
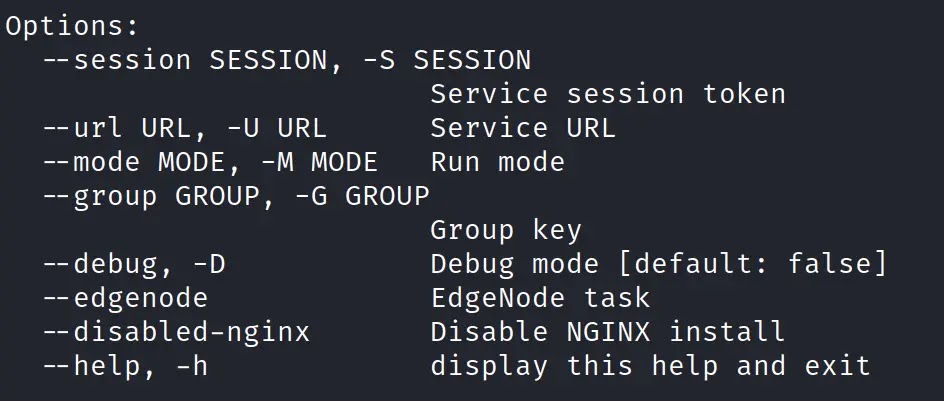
RingH23 gives operators end-to-end control over compromised Linux servers, especially nodes that sit in front of high-traffic websites. XLab describes components that handle initial deployment, persistence, traffic manipulation, and stealth, with several payloads designed to survive reboots and hide from common admin tools.
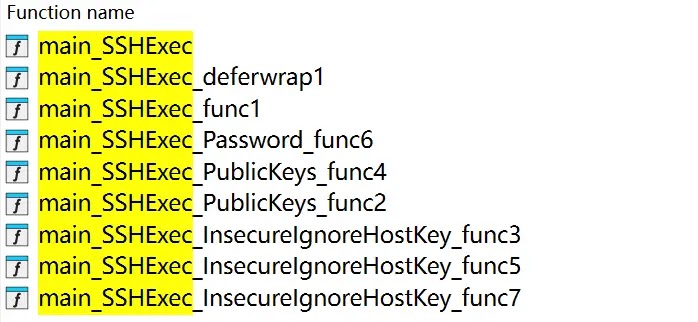
The campaign focuses on two infection routes. In one route, attackers compromise a GoEdge CDN management node and then push payloads to connected edge nodes via SSH commands. In the second route, attackers poison the MacCMS (maccms.la edition) update channel so admins pull a malicious PHP backdoor during updates, which triggers after the first admin login.
Quick view: two infection routes, one shared goal
| Route | Initial compromise point | What spreads next | End result on victim sites |
|---|---|---|---|
| CDN route | GoEdge management node | Forced edge-node downloads and execution | JavaScript injection and traffic hijacking |
| CMS route | MacCMS update channel | Malicious PHP backdoor and follow-on payload fetch | JavaScript injection and traffic hijacking |
| XLab reports both routes and ties them to RingH23’s modular payload set. |
Scale indicators XLab highlights
XLab points to typosquatted domains that impersonate well-known CDN brands and host the injected scripts. It lists several examples, including lookalikes for jQuery, jsDelivr, Cloudflare, and ByteDance.
XLab says one impersonation domain, “clondflare,” peaked on August 30, 2025 with 340,000 unique client visits in a day, and it notes its data covers about 5% of the domestic market, which implies broader exposure when extrapolated.
Inside the RingH23 component stack (as described by XLab)
| Component (XLab label) | Format | Purpose | Notable behavior |
|---|---|---|---|
| udev.sh / udev.rules | scripts/rules | Persistence | Uses udev-based persistence on Linux |
| module.so (Badnginx2s) | Nginx module | Traffic hijack | Injects malicious JS and performs wallet address replacement |
| ring04h_office_bin (Badredis2s) | binary | Backdoor | Maintains long-term access; uses remote C2 infrastructure |
| libutilkeybd.so (Badhide2s) | shared library | Rootkit-like hiding | Uses LD_PRELOAD to hide files, processes, and connections |
| XLab summarizes these modules and the responsibilities each one handles in the chain. |
Why defenders should care even if they do not run MacCMS
CDN nodes and reverse proxies sit in a high-leverage position. If an attacker controls them, the attacker can inject scripts into many downstream sites without touching each origin server. XLab frames RingH23 as a toolset designed for that exact advantage.
The MacCMS route also shows a familiar supply-chain risk pattern. Admins trust update channels and often grant them deep permissions by design, which turns an update compromise into near-instant server compromise.
What to do now (operator checklist)
- Treat your CDN management node as a Tier-0 asset and restrict SSH management paths, admin access, and database access for edge-node credentials.
- Hunt for unexpected Nginx modules, especially unknown “module.so” files, and compare active module lists against your known-good baseline.
- Check Linux persistence points for udev rules you did not deploy, and review recent changes under /etc/udev and related rule directories.
- Search for LD_PRELOAD abuse and suspicious entries that reference unknown shared libraries, since XLab links Badhide2s behavior to that technique.
- If you run MacCMS, treat the update channel as untrusted until you verify integrity, and review webroot for unexpected PHP files that behave like loaders or backdoors.
Detection ideas teams can deploy quickly
- Add DNS detections for obvious typosquats that mimic major CDNs, since XLab lists multiple lookalike domains used to host injected scripts.
- Alert on unusual outbound traffic from CDN edge nodes to unknown C2 endpoints, especially when nodes rarely initiate outbound sessions in your environment.
- Monitor integrity of Nginx config and module load directives, then trigger alerts when someone adds a new module in production without a change ticket.
FAQ
RingH23 is a modular Linux toolkit XLab attributes to a Funnull-linked operation, built for persistence, stealth, and web traffic hijacking at scale.
XLab says attackers compromise a GoEdge management node, harvest or use edge access, and push payloads to connected edge nodes through SSH execution.
XLab reports poisoning of the MacCMS (maccms.la edition) update channel, which delivers a malicious PHP backdoor and triggers after the admin’s first login.
Treasury sanctioned Funnull in May 2025 and linked the company to infrastructure that supported virtual currency investment scams, with over $200 million in reported U.S. losses.
XLab describes server-side JavaScript injection that redirects visitors. The impact lands on users through hijacked web traffic rather than a classic endpoint exploit chain.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages