Russian hackers hijack SOHO routers to spy on traffic and intercept logins
A Russian state-linked cyber campaign has compromised home and small-office routers to hijack DNS traffic and help intercept sensitive communications. Microsoft said the activity has affected more than 200 organizations and over 5,000 consumer devices, with targets spanning government, telecom, IT, and energy.
Microsoft attributes the operation to Forest Blizzard, also known as APT28 or Strontium, and linked part of the activity to Storm-2754. The company said the actors have targeted insecure SOHO routers since at least August 2025, then changed DNS settings to turn those devices into covert intelligence infrastructure.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The campaign matters because it shifts the attack surface away from hardened enterprise networks and toward neglected edge devices in homes and remote offices. Once a router is compromised, every connected laptop, phone, and workstation can start sending DNS traffic through infrastructure controlled by the attackers.
How the router hijacking works
Microsoft said the attackers first gain access to poorly secured SOHO routers, then replace legitimate DNS resolvers with actor-controlled ones. Because endpoint devices inherit network settings automatically over DHCP, victims may never notice the change while their DNS lookups move to hostile servers.
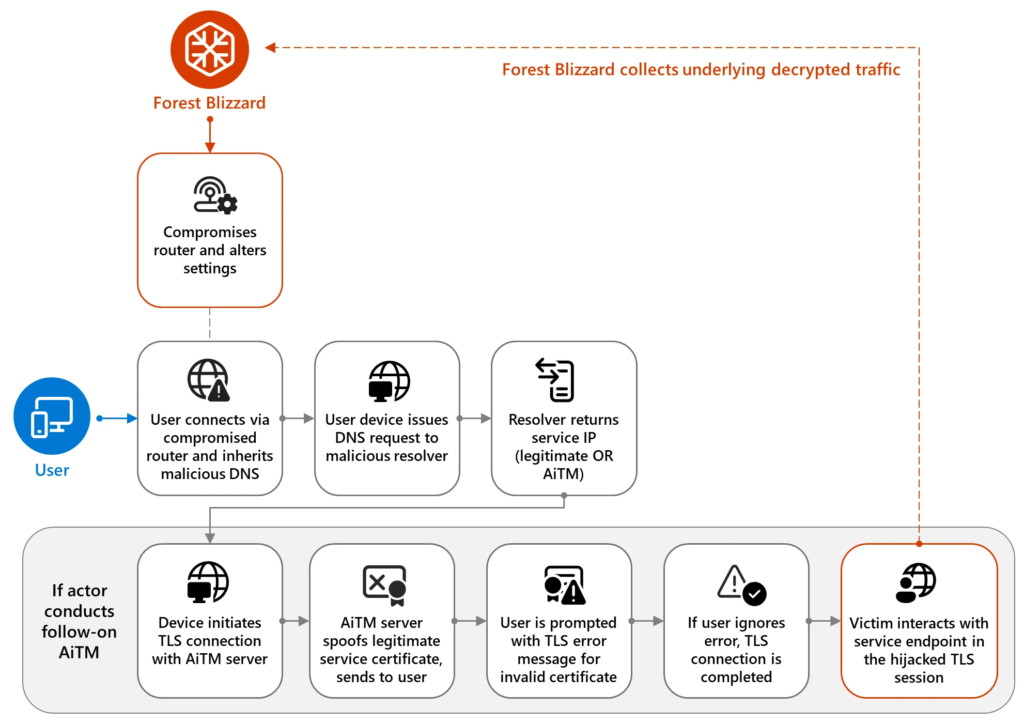
The company said Forest Blizzard likely uses dnsmasq, a common DNS forwarding and DHCP service built into many routers, to observe and respond to DNS queries on port 53. That gives the group passive visibility into domain lookups without the noise that often comes with direct intrusion into enterprise systems.
For higher-value targets, the campaign goes further. Microsoft and the UK’s NCSC said the attackers used adversary-in-the-middle techniques by returning spoofed IP addresses for specific domains, which redirected victims to attacker-controlled infrastructure that served fake TLS certificates.
Why this campaign is more dangerous
If a victim ignores the certificate warning, the TLS session can continue through the attacker’s system. Microsoft said that flow allowed Forest Blizzard to collect plaintext traffic, including credentials, email content, and cloud-hosted data from selected targets.
Microsoft said it observed AiTM activity against Microsoft Outlook on the web domains, as well as non-Microsoft government servers in at least three African countries. The company also said no Microsoft-owned assets or services were compromised in the campaign itself.
This appears to mark a notable operational step for APT28. Microsoft said it was the first time it had seen Forest Blizzard use DNS hijacking at this scale specifically to enable TLS AiTM attacks after edge-device compromise, while the NCSC said the activity shows how vulnerable routers can support espionage against both organizations and individuals.
Key facts at a glance
| Item | Confirmed detail |
|---|---|
| Threat actor | Forest Blizzard, also known as APT28 or Strontium |
| Microsoft subgroup | Storm-2754 |
| Activity start | At least August 2025 |
| Main technique | SOHO router compromise and DNS hijacking |
| Follow-on technique | Adversary-in-the-middle TLS interception |
| Confirmed impact | 200+ organizations and 5,000+ consumer devices |
| Sectors hit | Government, IT, telecom, energy |
| Notable lure outcome | Spoofed DNS replies and invalid TLS certificates |
What defenders should do now
- Reboot and update router firmware, especially on home and small-office devices that may lag behind on security patches.
- Replace default router passwords and remove weak or reused credentials.
- Audit DNS resolver settings on endpoints and routers for unauthorized changes.
- Train users never to bypass certificate warnings, especially on email and cloud login pages.
- Use VPNs and segment remote worker traffic so compromised home routers have less direct visibility into enterprise services.
- Hunt for anomalous DNS changes in endpoint and network telemetry using vendor detections where available.
Why remote workers should pay attention
This campaign shows that a cheap router in a home office can become part of a nation-state espionage chain. An attacker does not need to break into Microsoft 365 or a company VPN first if they can manipulate the DNS traffic flowing out of an employee’s network.
The risk rises further when unsupported devices stay online for years without updates. The NCSC warned that vulnerable routers can enable credential theft, fake website redirection, and follow-on compromise across connected devices.
US authorities have already moved to disrupt part of the infrastructure. The Justice Department said the FBI identified and reset compromised routers in the United States after securing court authorization to cut Russian intelligence access to the hijacking network.
FAQ
Microsoft attributed the campaign to Forest Blizzard, also known as APT28 or Strontium, a threat actor linked to Russian military intelligence.
The campaign focuses on insecure SOHO routers used in homes and small offices, especially devices that are exposed, outdated, or poorly secured.
It lets attackers control where victims go when they try to reach a domain. In this campaign, that control supported traffic monitoring and selective redirection to fake servers for credential interception.
Update router firmware, change default passwords, verify DNS settings, and never click through certificate warnings. Organizations should also assume unmanaged home routers are a real enterprise risk.1
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages