Sandworm reportedly uses SSH-over-Tor tunnels for long-term hidden access

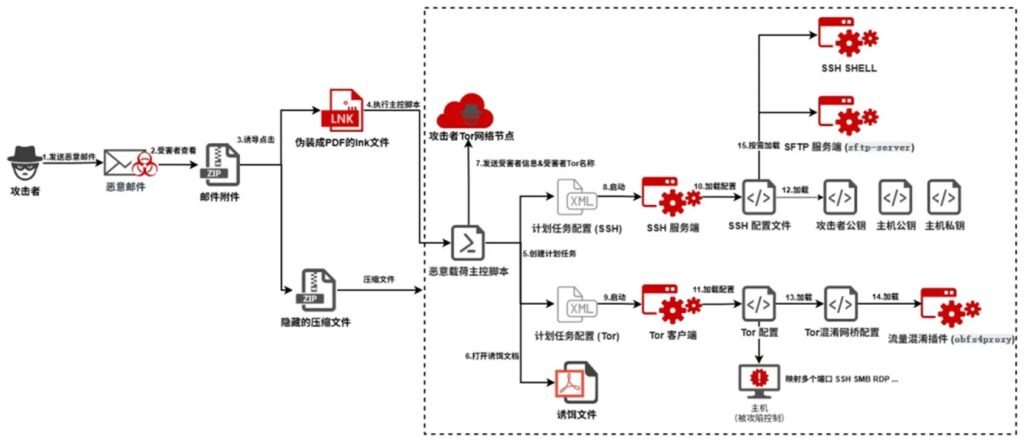
Sandworm has reportedly used a combined SSH and Tor tunneling setup to keep hidden access inside victim networks for long periods. The campaign was detailed by 360 Advanced Threat Research Institute and later summarized in English-language security reporting.
The attack uses a spear-phishing ZIP file with a malicious Windows shortcut, a decoy document, and tools disguised as familiar applications. Once opened, the toolkit builds a layered remote access channel that can hide behind encryption and Tor routing.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The key point is not just that the attackers used Tor. The more serious issue is that they nested SSH inside Tor, then mapped local services such as SMB and RDP to a hidden .onion address. That gives the operator a way to reach the infected machine without exposing a normal inbound connection.
How the attack starts
The campaign begins with a spear-phishing email that carries a ZIP archive named Iskhod_7582_Predstavlenie_na_naznachenie.zip. The archive reportedly contains a malicious .lnk shortcut disguised as a PDF document and a fake $RECYCLE.BIN folder made to look like a normal Windows system folder.
When the victim opens the shortcut, the malware chain runs in the background while a decoy PDF opens on screen. This helps the attackers reduce suspicion because the user sees something that looks expected.
The sample reporting lists the ZIP archive MD5 hash as 2156c270ffe8e4b23b67efed191b9737. Security teams can use that hash as a starting point, but they should not rely on it alone because attackers can easily change file hashes in future waves.
What the tunnel does and why it matters
The attack’s main purpose is long-term access. Researchers say the toolkit combines an OpenSSH daemon with Tor and obfs4 traffic obfuscation, which helps the traffic blend into random-looking TCP streams.
The SSH service listens only on the local loopback address, reportedly on port 20321. That design makes the SSH server harder to spot from outside the machine because it does not behave like a normal exposed remote service.
The Tor component then creates a hidden service and generates an .onion hostname. The script sends victim identity details to a hardcoded Tor command-and-control address, allowing the attacker to reconnect through the Tor network.
| Item | What current reporting shows |
|---|---|
| Threat group | Sandworm, also tracked as APT-C-13 and FROZENBARENTS |
| Reported technique | SSH nested inside Tor |
| Initial access | Spear-phishing ZIP with malicious .lnk shortcut |
| Decoy method | Fake PDF shown while payloads install |
| Persistence method | Hidden scheduled tasks |
| Local services exposed | SMB port 445 and RDP port 3389 |
| Main risk | Stealthy remote control through a Tor hidden service |
How Sandworm hid the tools
The malware uses names that look like normal software. The reports say operagx.exe is actually an OpenSSH daemon, while dropbox.exe is a Tor server. A third file, safari.exe, works as an obfs4 plugin, and obsstudio.exe acts as an SFTP server for file transfers.
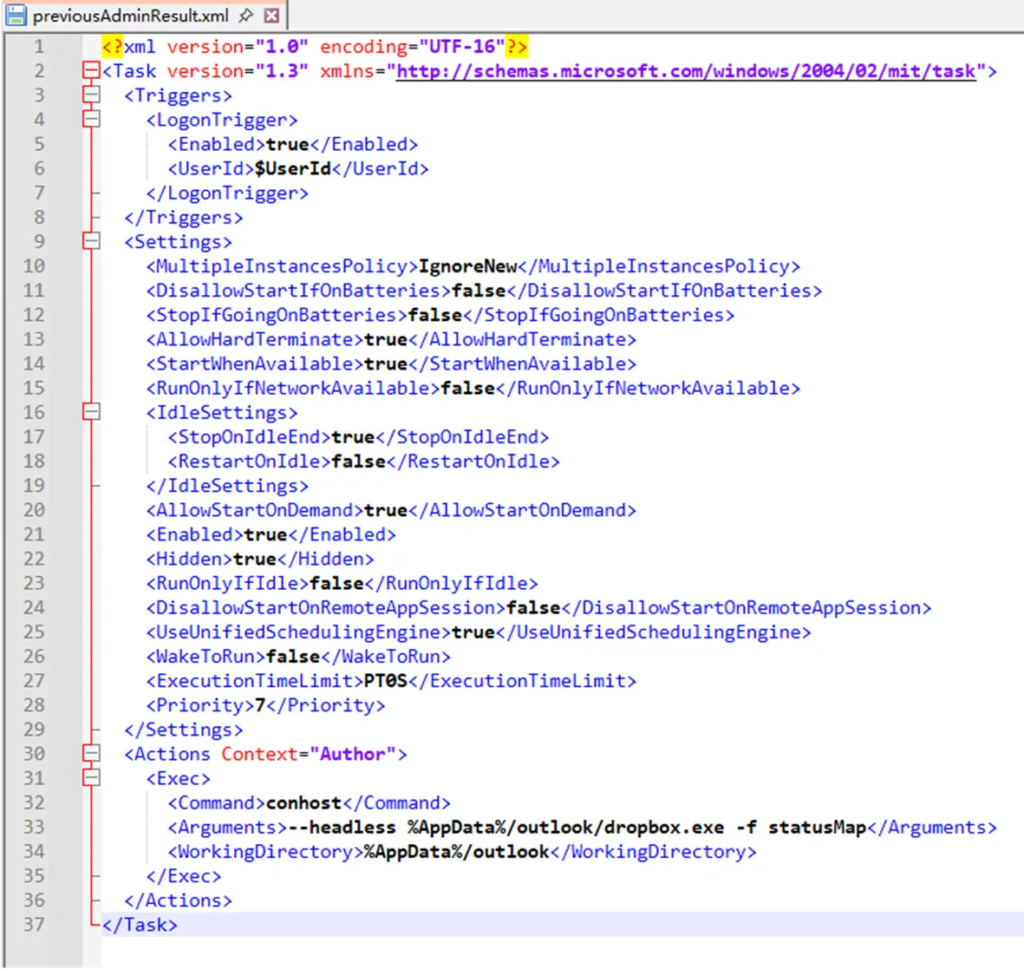
This naming strategy matters because security teams often see many legitimate browser, cloud storage, and media application files across business networks. Attackers can use that noise to hide malicious binaries in user directories or less monitored paths.
The main script also checks whether it is running on a real machine before continuing. It reportedly looks for at least 10 recent .lnk files and 50 or more running processes, which can help the malware avoid basic sandbox analysis.
What is confirmed and what is still unclear
What is confirmed is that 360’s public security news page lists a report on suspected APT-C-13, or Sandworm, using SSH and Tor tunnels for covert persistence. The page describes the group as a state-backed APT focused on long-term cyber espionage against government, diplomatic, energy, and research targets.
MITRE tracks Sandworm Team separately as group G0034 and says the group has been active since at least 2009. MITRE also links Sandworm to GRU Unit 74455 and lists major past operations, including attacks against Ukrainian electrical companies, NotPetya, Olympic Destroyer, and other campaigns.
What remains less clear from the available public reporting is the full victim list, the number of affected organizations, and whether the same tooling has been deployed in multiple regions. The public summaries focus mainly on the attack chain and tradecraft rather than campaign scale.
Why defenders may care
This tradecraft matters because it abuses tools and services that can look legitimate in the right context. SSH, Tor, scheduled tasks, SFTP, RDP, and SMB all have normal uses, but the combination creates a hidden remote access path that standard perimeter checks may miss.
The use of Tor also reduces the value of simple IP-based blocking. Defenders need endpoint visibility, scheduled task auditing, command-line monitoring, and unusual process path detection to catch this kind of setup.
MITRE’s ATT&CK guidance notes that adversaries can use SSH for remote access after they obtain valid access, and it also documents how attackers use common application-layer protocols to blend command traffic with normal network activity.
At a glance
| Area | Details |
|---|---|
| Delivery file | Iskhod_7582_Predstavlenie_na_naznachenie.zip |
| Malicious trigger | Disguised .lnk shortcut |
| Fake folder | $RECYCLE.BIN |
| Main script | currentSessionTrigger |
| Scheduled tasks | OperagxRepairTask, DropboxRepairTask |
| SSH disguise | operagx.exe |
| Tor disguise | dropbox.exe |
| Obfuscation plugin | safari.exe |
| SFTP component | obsstudio.exe |
| Local SSH port | 20321 |
| Mapped services | SMB 445 and RDP 3389 |
What security teams can do now
- Audit scheduled tasks for names that imitate browsers, cloud storage apps, or common desktop software.
- Look for OpenSSH, Tor, SFTP, or obfs4-like binaries running from unusual user-writable locations.
- Hunt for SSH daemons bound to loopback addresses on non-standard ports.
- Check for unexpected RDP and SMB exposure through local tunnels.
- Review outbound Tor and obfs4 traffic patterns, especially from endpoints that should not use anonymity networks.
- Block or quarantine ZIP attachments that contain
.lnkfiles disguised as documents. - Train users to avoid opening shortcuts inside archives, even when the file icon looks like a PDF.
- Monitor curl commands that repeatedly contact
.onioninfrastructure through Tor.
FAQ
Sandworm is a Russian state-linked threat group tracked by several names, including APT-C-13, FROZENBARENTS, APT44, and Seashell Blizzard. MITRE tracks Sandworm Team as G0034 and links it to GRU Unit 74455.
SSH-over-Tor means the attacker routes SSH remote access through the Tor network. In this campaign, the approach reportedly creates a hidden encrypted channel between the compromised machine and the attacker.
Yes. Current reporting says the infection starts when a victim opens a malicious .lnk shortcut inside a ZIP archive. A decoy PDF opens to make the action look normal.
SMB and RDP are powerful Windows services. If attackers map them through a hidden tunnel, they may access files, move laterally, or operate the machine remotely without opening normal inbound firewall paths.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more


User forum
0 messages