Silver Fox Hackers Use Stolen EV Certificates to Spread AtlasCross RAT Malware

A China-linked threat group known as Silver Fox is actively running a large malware campaign using stolen Extended Validation certificates to bypass security checks and infect systems. The attackers target Chinese-speaking users by impersonating trusted apps like Zoom, Signal, and Surfshark, making the campaign difficult to detect.
Security researchers confirm that the malware, called AtlasCross RAT, uses advanced stealth techniques to stay hidden, execute commands remotely, and disable protections inside infected machines. The use of valid EV certificates allows the malicious files to appear trustworthy to both users and automated defenses.
This campaign shows how attackers now combine social engineering with highly technical evasion methods to gain long-term access to systems.
How the AtlasCross RAT Attack Works
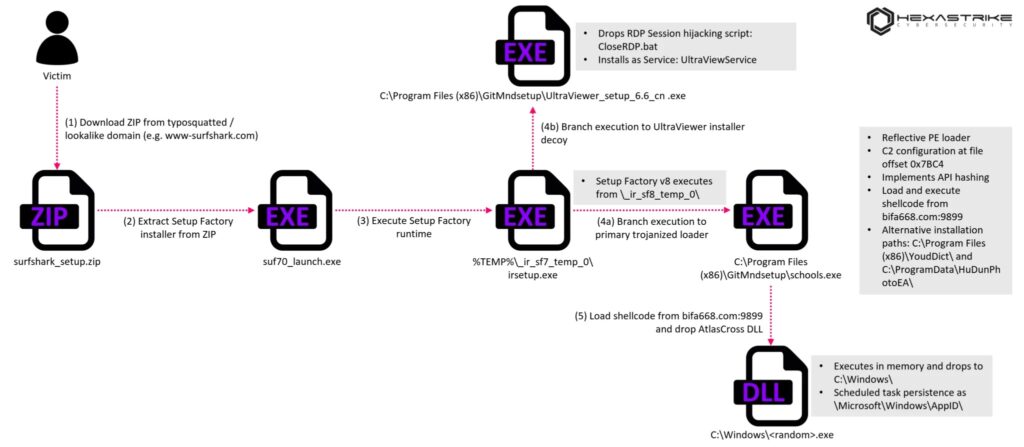
The infection begins when users visit fake websites designed to look like legitimate software providers. These domains closely mimic real brands, increasing the chances of successful downloads.
Once the victim downloads the file, they receive a compressed archive containing multiple layers of installers. The setup appears legitimate, but it secretly delivers malware in the background.
Key steps in the attack chain:
- Victim downloads software from a fake website
- ZIP file contains a multi-layer installer
- Installer drops a malicious loader and a legitimate decoy app
- Malware executes silently in memory without writing files to disk
- A second-stage payload connects to a remote command server
The attackers also use a stolen EV certificate linked to a company called DUC FABULOUS CO., LTD, which remains valid until May 2027. This allows the malware to pass security warnings and appear signed by a trusted entity.
What Makes This Malware Hard to Detect
AtlasCross RAT uses several advanced techniques to avoid detection and analysis. Instead of relying on basic malware methods, it operates in memory and hides its activity from security tools.
Main evasion techniques include:
- Fileless execution that avoids writing payloads to disk
- API obfuscation using PEB walking and hashing
- Encrypted communication with command servers
- Use of legitimate processes to mask malicious activity
The malware also retrieves additional payloads over raw TCP connections, making network monitoring more difficult.
PowerChell Framework Disables Windows Security
At the center of this campaign is a custom tool called PowerChell. This component allows the malware to execute PowerShell commands without launching the standard powershell.exe process.
This approach helps the attackers avoid detection by traditional monitoring tools.
PowerChell capabilities include:
- Disables AMSI to prevent malware scanning
- Turns off Event Tracing for Windows logging
- Bypasses restricted PowerShell execution modes
- Suppresses script logging completely
By embedding the .NET runtime directly into the malware process, attackers gain full control over execution without triggering alerts.
Data Theft and System Control Features
Once installed, AtlasCross RAT gives attackers deep control over the infected system. It can collect sensitive data, manipulate processes, and maintain long-term access.
Observed capabilities include:
- DLL injection into WeChat for data harvesting
- Hijacking Remote Desktop sessions using built-in Windows tools
- Terminating connections from local security software
- Maintaining encrypted communication with command servers
The malware uses ChaCha20 encryption with random keys, which makes traffic analysis and detection more complex.
Known Indicators of Compromise (IOCs)
Security teams should monitor the following indicators linked to this campaign:
| Indicator Type | Value | Description |
|---|---|---|
| EV Certificate | 2C1D12F8BBE0827400A8440AF74FFFA8DCC8097C | Stolen certificate tied to DUC FABULOUS CO., LTD |
| C2 Domain | bifa668.com | Command and control server |
| IP Address | 61.111.250[.]139 | Remote server used for communication |
| Beacon Signature | 53 46 75 63 6b 00 00 00 | Malware handshake pattern |
| Fake Domain | www-surfshark[.]com | Phishing download page |
| Fake Domain | signal-signal[.]com | Malware distribution site |
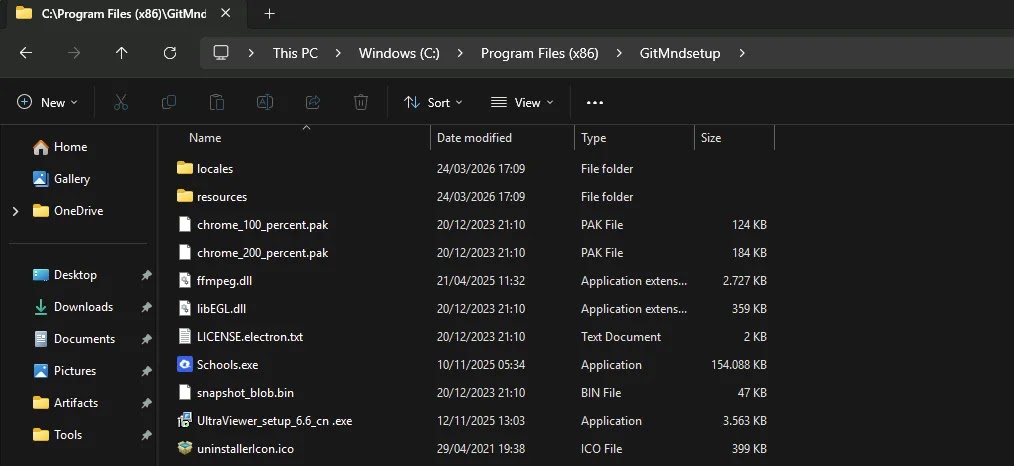
| File Path | C:\Program Files (x86)\GitMndsetup\ | Payload installation directory |
Why This Campaign Matters
This operation highlights a shift in how advanced threat actors operate. Instead of directly attacking systems with obvious malware, they now focus on trust exploitation and stealth.
Key concerns for organizations:
- Signed malware reduces user suspicion
- Fileless attacks bypass traditional antivirus tools
- Security tools may fail to detect network-level interference
- Long-term persistence increases data exposure risks
The move from killing security processes to silently disrupting their network communication shows a more advanced and strategic approach.
How to Protect Your Systems
Organizations and users can reduce risk by applying strict security practices and monitoring suspicious activity.
Recommended actions:
- Verify software downloads only from official sources
- Monitor unusual PowerShell activity in memory
- Check for unauthorized scheduled tasks
- Inspect network traffic for unknown TCP connections
- Validate digital certificates used by applications
Security teams should also audit systems for unexpected loading of System.Management.Automation.dll, which may indicate hidden PowerShell execution.
FAQ
AtlasCross RAT is a remote access trojan that allows attackers to control infected systems, steal data, and execute commands remotely.
EV certificates make malware appear legitimate, helping it bypass security checks and gain user trust.
It runs in memory, encrypts communication, and disables Windows security features like AMSI and logging systems.
The campaign mainly targets Chinese-speaking users and professionals through fake software download websites.
Traditional antivirus may struggle due to fileless execution and certificate abuse, but advanced detection tools can identify suspicious behavior.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages