SloppyLemming targets Pakistan and Bangladesh with BurrowShell and a Rust-based RAT
A cyber-espionage group known as SloppyLemming has been linked to a year-long campaign targeting government and critical infrastructure organizations in Pakistan and Bangladesh. Recent reporting that cites Arctic Wolf says the group used two malware chains between January 2025 and January 2026, delivering a custom backdoor called BurrowShell and a Rust-based keylogger/RAT through phishing lures disguised as PDFs and Excel files.
The campaign fits the group’s older pattern. Cloudflare said in 2024 that SloppyLemming had routinely targeted Pakistani government, defense, telecommunications, technology, and energy organizations, while also going after Bangladesh, Sri Lanka, Nepal, and China. Cloudflare also linked the actor to heavy abuse of Cloudflare Workers as part of its espionage operations.
One point needs careful wording. The sample article presents the India alignment as settled fact. Public reporting I found describes that link as suspected or consistent with prior assessments, not as an officially confirmed attribution. Cloudflare said SloppyLemming aligns with the adversary OUTRIDER TIGER tracked by CrowdStrike, while current reporting says the new victimology and infrastructure use are consistent with South Asia-focused intelligence collection.
What the latest campaign reportedly used
| Element | What reporting says |
|---|---|
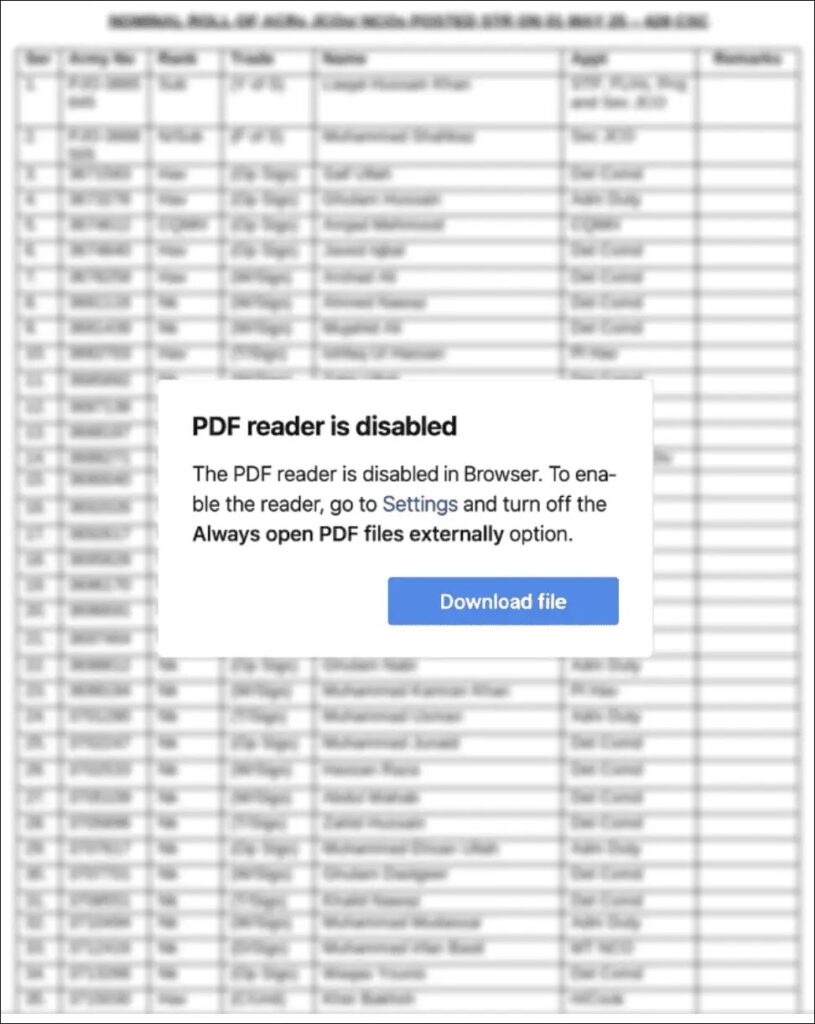
| Initial lure | Spear-phishing with PDF files and macro-enabled Excel documents. |
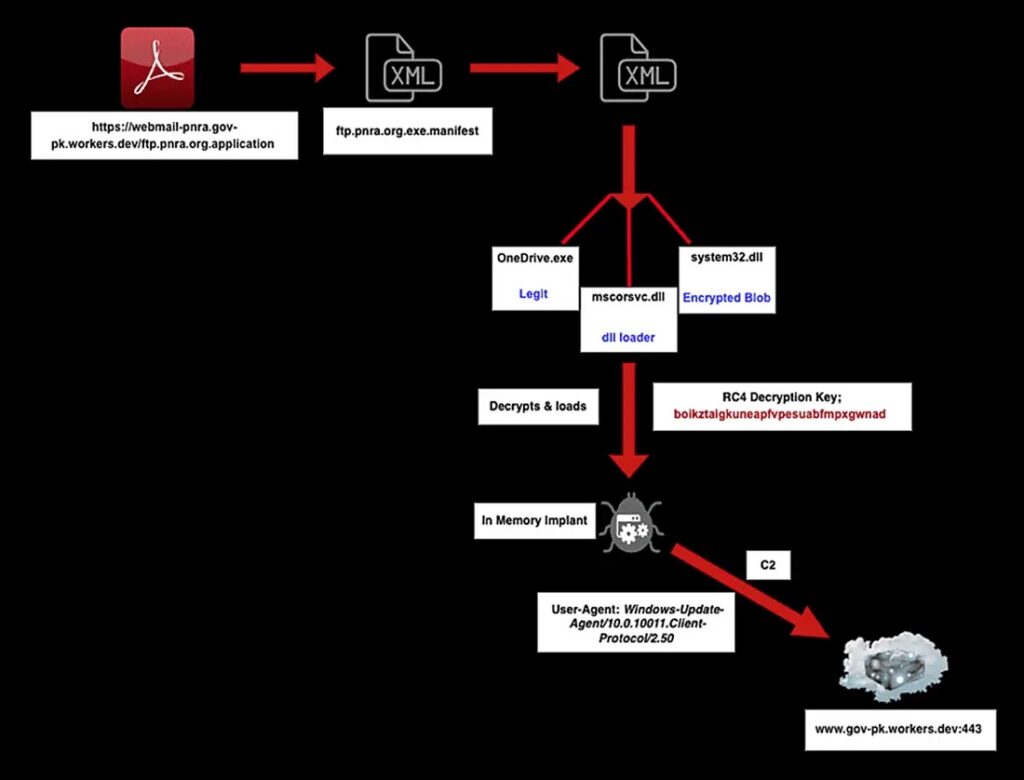
| Main malware | BurrowShell, described as an in-memory backdoor or shellcode implant. |
| Second payload | A Rust-based keylogger/RAT with network enumeration and port-scanning features. |
| Execution method | DLL side-loading / DLL search order hijacking using trusted Microsoft binaries. |
| Infrastructure | 112 Cloudflare Workers domains registered over the one-year period, up sharply from the 13 previously flagged by Cloudflare. |
According to the current reporting, BurrowShell stands out because it stays in memory after decrypting its payload and disguises command-and-control traffic as Windows Update communications over port 443. The Rust implant appears more focused on collection, especially keystrokes and local network discovery.
That mix suggests a flexible espionage operation rather than a one-size-fits-all malware dropper. One tool appears suited for persistence, command execution, and proxying, while the other supports information theft and local reconnaissance.
Why the Cloudflare Workers angle matters
The infrastructure story is one of the strongest signs that this is part of a broader, long-running operation. Cloudflare previously documented SloppyLemming’s routine use of Workers in South Asia-focused espionage, and the new reporting says the actor expanded that infrastructure significantly in 2025.
That does not mean Cloudflare Workers are unsafe by design. Cloudflare’s own documentation shows that Workers and workers.dev domains are legitimate hosting and routing features. The real issue is that threat actors can abuse fast, low-friction cloud infrastructure to rotate domains and stand up phishing or C2 endpoints quickly.
Reported target focus
| Country | Reported targets |
|---|---|
| Pakistan | Government, defense, nuclear oversight, telecommunications, and critical infrastructure organizations. |
| Bangladesh | Energy utilities, financial institutions, media, and government-linked entities. |
The Pakistan focus lines up closely with Cloudflare’s earlier findings, which already described Pakistan as the actor’s primary target. The Bangladesh targeting also fits the group’s established regional scope, but the new reporting suggests the campaign became more organized and infrastructure-heavy over the past year.
What defenders should do
- Block or closely inspect Cloudflare Workers links used in unsolicited documents, especially ones that mimic government or utility domains.
- Disable Office macros from externally received files unless there is a strict business need. The second infection path reportedly relied on Excel macros.
- Watch for trusted Microsoft binaries loading DLLs from unusual paths, especially side-loading patterns tied to
.NETtools or Windows activation-related files. - Hunt for suspicious Run registry persistence and encrypted outbound traffic to domains that do not match your normal environment.
- Treat document lures with fake “download” buttons or blurred previews as high risk. Those are common social-engineering patterns in this campaign.
FAQ
SloppyLemming is a cyber-espionage actor tracked by Cloudflare since at least late 2022. Cloudflare says it targets South and East Asian organizations, with Pakistan as a primary focus.
Current March 2026 reporting describes BurrowShell as a newly documented backdoor used in this campaign. Public details so far come mainly through reporting that cites Arctic Wolf.
Not publicly in the sources I found. The alignment is presented as suspected or consistent with prior assessments, not as an official confirmed attribution.
Rust-based malware has become more common because it is portable, efficient, and often harder for defenders to classify quickly than older, more familiar codebases. In this case, reporting says the Rust component handled keylogging and local discovery tasks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages