Storm-1175 exploits web-facing flaws to deploy Medusa ransomware, Microsoft warns

Microsoft says Storm-1175 is running high-speed ransomware attacks that target vulnerable web-facing systems, steal data, and then deploy Medusa ransomware. The company says some intrusions moved from initial access to impact within 24 hours, while many others unfolded over five to six days.
According to Microsoft Threat Intelligence, the financially motivated group has exploited more than 16 vulnerabilities since 2023 across products such as Microsoft Exchange, PaperCut, Ivanti, ScreenConnect, TeamCity, SimpleHelp, CrushFTP, GoAnywhere MFT, SmarterMail, and BeyondTrust. Microsoft also says the group mainly weaponizes recently disclosed flaws, but it has also used zero-days before public disclosure.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
The warning matters because Storm-1175 focuses on internet-exposed assets that many organizations still have not patched or isolated properly. Microsoft says the recent victims heavily affected healthcare, along with education, professional services, and finance organizations in Australia, the United Kingdom, and the United States.
How Storm-1175 gets in and moves fast
Microsoft says the group attacks the short window between vulnerability disclosure and patch adoption. In one case, it weaponized SAP NetWeaver flaw CVE-2025-31324 one day after disclosure. The company also says Storm-1175 exploited SmarterMail flaw CVE-2026-23760 and GoAnywhere MFT flaw CVE-2025-10035 a week before public disclosure.
After gaining access, Storm-1175 often plants a web shell or another remote access payload. Microsoft says the group then creates a new user account, adds it to the administrators group, and starts reconnaissance and lateral movement from that account.
Microsoft also says the attackers rely heavily on remote monitoring and management tools after compromise. The list includes Atera, Level RMM, N-able, DWAgent, MeshAgent, ConnectWise ScreenConnect, AnyDesk, and SimpleHelp, along with tools such as PowerShell, PsExec, Impacket, and Cloudflare tunnels renamed to look legitimate.
Storm-1175 at a glance
| Item | Details |
|---|---|
| Threat actor | Storm-1175 |
| Ransomware used | Medusa |
| Main entry path | Vulnerable web-facing assets |
| Tempo | Sometimes within 24 hours from access to impact |
| Industries hit recently | Healthcare, education, professional services, finance |
| Regions highlighted by Microsoft | Australia, United Kingdom, United States |
| Key post-compromise tools | RMM software, PowerShell, PsExec, Impacket, Cloudflare tunnels |
What happens after the break-in
Microsoft says credential theft plays a major role in the attacks. The group has used Impacket, Mimikatz, WDigest changes, Task Manager LSASS dumps, Veeam password recovery scripts, NTDS.dit access, and SAM access to strengthen control inside the environment.
The attackers also tamper with defenses before pushing ransomware. Microsoft says Storm-1175 modifies Defender Antivirus settings in the registry and uses encoded PowerShell commands to add the C:\ drive to antivirus exclusions, which helps payloads run without alerts.
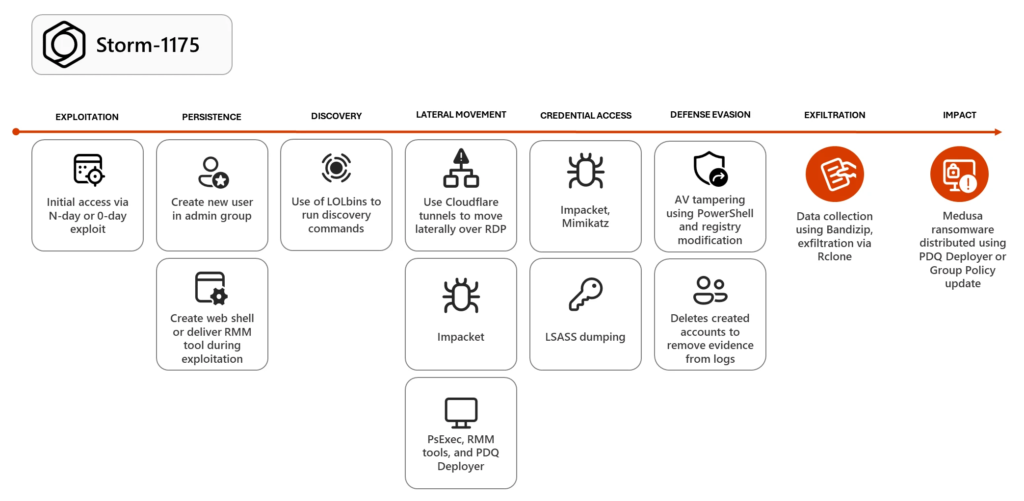
For data theft and final deployment, Microsoft says the group uses Bandizip to collect files and Rclone to exfiltrate them. It then often uses PDQ Deployer to launch a script called RunFileCopy.cmd and spread Medusa ransomware, while some cases involved Group Policy updates to push the payload across the domain.
Why this campaign stands out
- Microsoft says Storm-1175 can move from access to ransomware deployment in as little as one day.
- The group mixes N-day exploitation with zero-day use, which raises pressure on patching teams.
- The attackers use legitimate admin and RMM tools, which can make malicious activity harder to separate from normal IT traffic.
- Medusa uses double extortion, so victims face both encryption and data leak pressure.
Microsoft’s guidance for defenders
Microsoft recommends reducing exposure first. The company says organizations should understand their external attack surface, isolate web-facing systems from the public internet where possible, and place unavoidable public-facing servers behind a WAF, reverse proxy, or perimeter network.
The company also recommends stronger credential protection. Microsoft specifically points to least privilege, Credential Guard, tenant-wide tamper protection, Defender always-on protection, and the DisableLocalAdminMerge setting to stop local admin changes to antivirus exclusions through Group Policy.
For environments that use approved RMM tools, Microsoft says teams should enforce MFA where possible. It also recommends Microsoft Defender XDR automatic attack disruption and attack surface reduction rules to help block common ransomware techniques and contain attacks in progress.
Priority actions
| Priority | Action | Why it matters |
|---|---|---|
| High | Patch exposed internet-facing systems quickly | Storm-1175 targets the gap between disclosure and patch adoption |
| High | Remove or isolate unnecessary public-facing services | Reduces initial access opportunities |
| High | Monitor for new admin users and credential theft signals | Microsoft says these often appear early in the attack chain |
| High | Turn on tamper protection and review Defender exclusions | The group tampers with Defender settings |
| Medium | Lock down RMM tools and require MFA | Attackers abuse legitimate remote admin tools |
| Medium | Enable Credential Guard and least privilege controls | Limits credential theft and lateral movement |
| Medium | Use attack surface reduction and automatic attack disruption | Helps block or contain ransomware behavior |
What this means for organizations
Microsoft’s report shows a ransomware crew that does not waste time. It looks for exposed systems, grabs a foothold, steals credentials, weakens defenses, exfiltrates data, and then deploys ransomware with tools that many IT teams already know.
That makes web-facing asset hygiene more important than ever. Organizations that leave critical services exposed, delay patches, or allow broad admin privileges give groups like Storm-1175 the exact opening they want.
The biggest takeaway is simple. If a vulnerable external system stays online long enough, Storm-1175 may not need much time to turn it into a full Medusa ransomware incident.
FAQ
Microsoft tracks Storm-1175 as a financially motivated cybercriminal actor associated with high-velocity Medusa ransomware campaigns.
Microsoft says the group focuses on vulnerable web-facing systems and weaponizes recently disclosed flaws for initial access.
No. Microsoft says the actor usually uses N-day vulnerabilities, but it has also used zero-days, including cases where exploitation happened a week before public disclosure.
Microsoft highlights alerts tied to credential theft, suspicious new user creation, tampering with Defender settings, unauthorized RMM use, and signs of ransomware deployment or exfiltration.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages